Quick overview
High-level deployment flow:- Open your Virtual WAN resource in the Azure portal.
- Select the hub to host the NVA.
- Create a Network Virtual Appliance entry and choose a Marketplace vendor image.
- Configure vendor- and deployment-specific options (scale units, licensing/token, credentials, image version).
- Review and create — Azure provisions the NVA and integrates it with the hub routing fabric.
- Virtual WAN hub selection — selects region and the hub attachment.
- Infrastructure scale units — capacity units used to size the appliance for expected throughput (refer to vendor docs for exact per‑unit throughput).
- Licensing and authentication token — vendor tokens, BYOL, or Marketplace billing options.
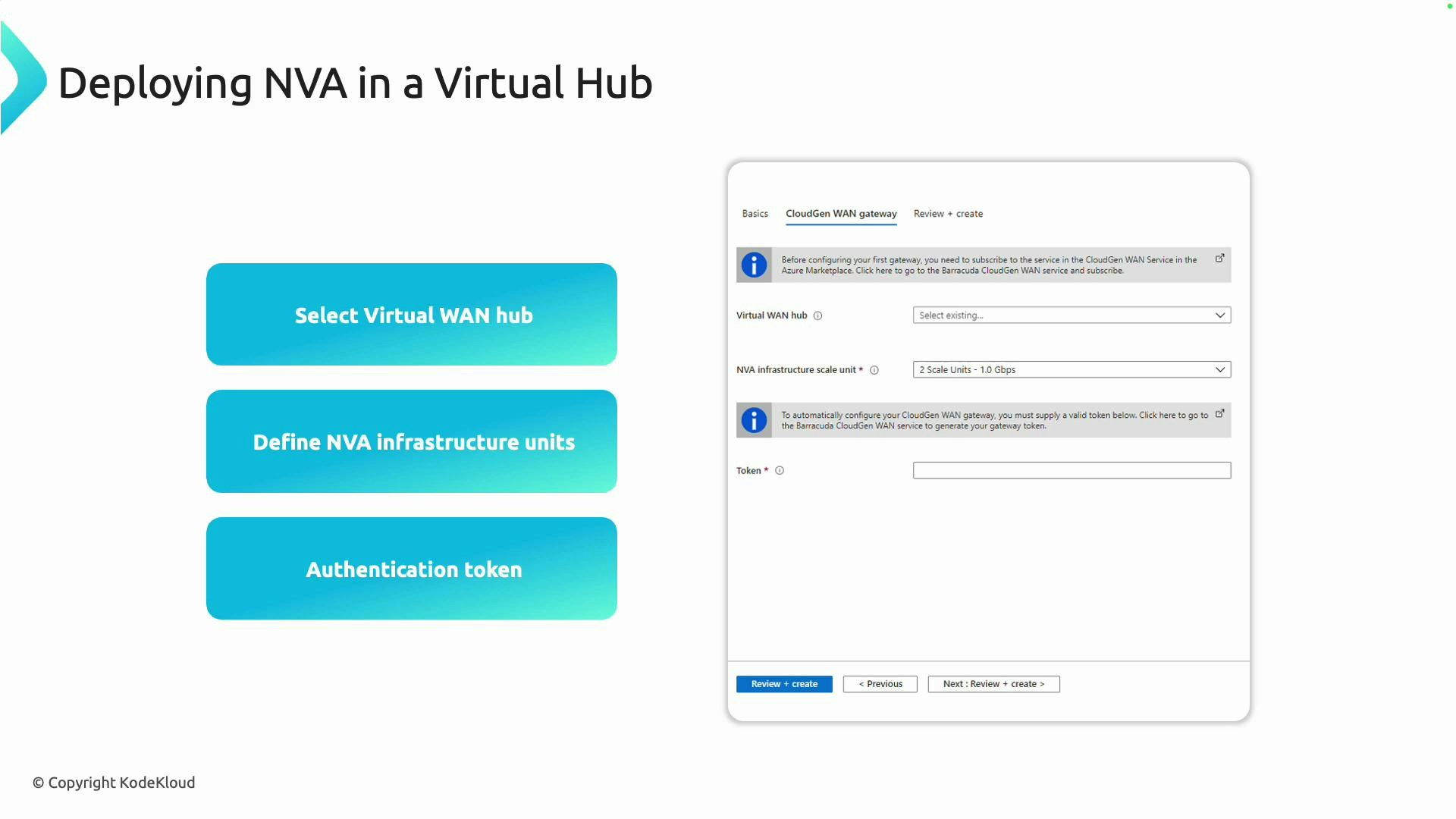
Check vendor documentation for exact scale unit throughput and licensing requirements. Bandwidth per scale unit varies by vendor and SKU.
Portal walkthrough — step by step (high level)
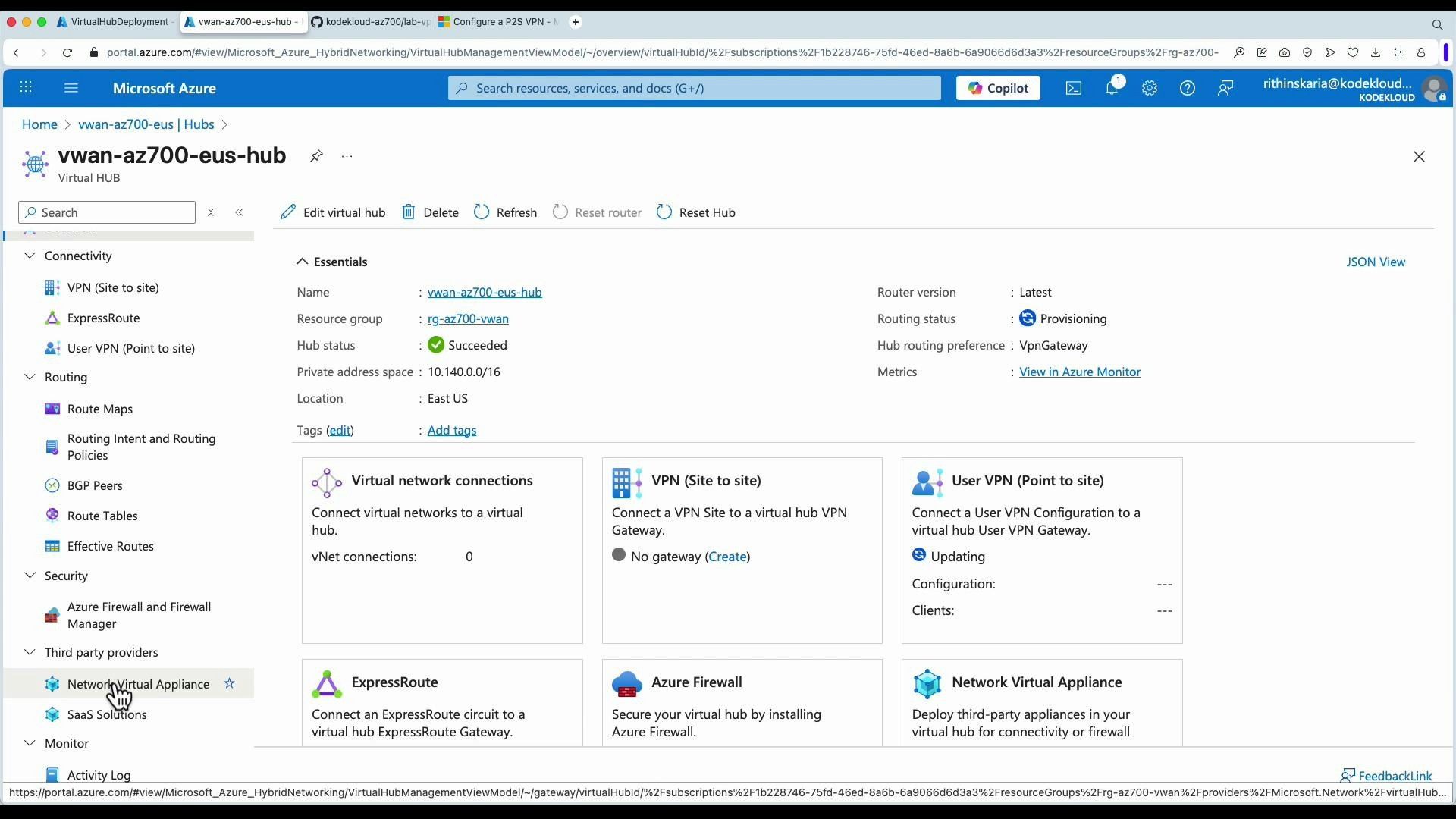
Open your Virtual WAN resource in the Azure portal and navigate to Hubs. Then:- Select the hub you want to extend.
- In the hub management blades, choose Network Virtual Appliances.
- Click Create network virtual appliance. This opens the Marketplace and lists supported vendor images.
- Select a vendor listing and click Create to start the deployment workflow.
- Complete the vendor-specific configuration pages (subscription, resource group, region, license model, credentials, image version, scale units).
- Review and create. Azure provisions and integrates the appliance into the hub.
- Choose the Fortinet Marketplace listing, select the plan (BYOL or pay‑as‑you‑go), and click Create.
- Provide FortiGate credentials, license details (or BYOL token), region, and image version.
- Specify scale units and any vendor-specific deployment options then deploy.
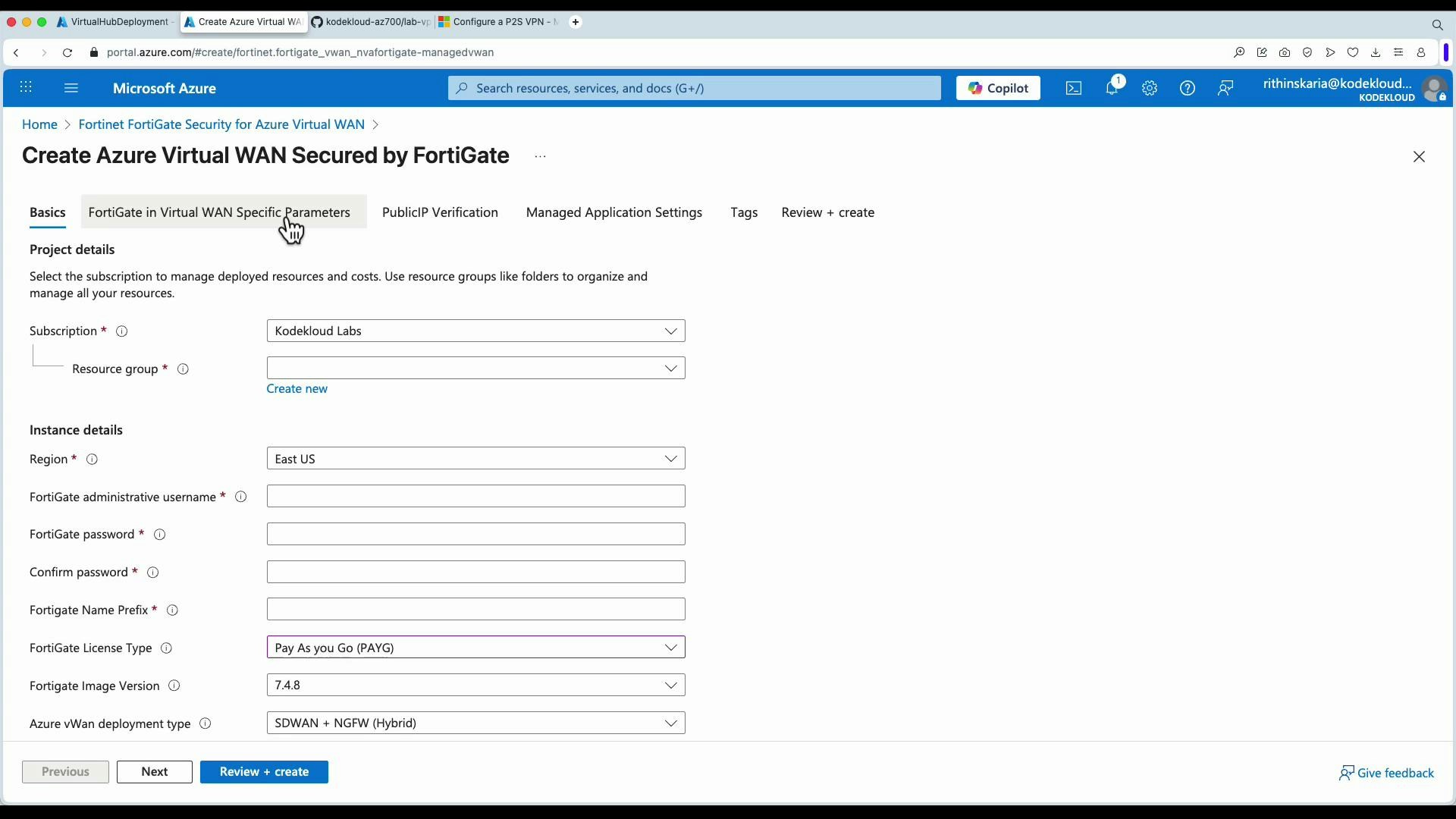
Vendor-specific settings (licensing, tokens, image versions) are managed by the vendor’s Marketplace offering. Ensure you have the correct license or subscription before deploying.
Common configuration checklist
| Configuration item | Purpose | Notes |
|---|---|---|
| Virtual WAN hub | Attach NVA to the correct hub/region | Must match hub where traffic will be steered |
| Scale units | Capacity sizing for expected throughput | Verify vendor documentation for per-unit throughput |
| Licensing/token | License the appliance (BYOL, token, PAYG) | Some vendors require tokens obtained after Marketplace subscription |
| Credentials | Admin account and SSH/RDP options | Use secure credential handling and Key Vault when possible |
| Image version | Select vendor image and patch level | Keep images updated to address security fixes |
Vendor selection — quick comparison
| Vendor examples | Typical use cases |
|---|---|
| Fortinet (FortiGate) | Next‑gen firewall, NGFW features in Virtual WAN |
| Cisco | Enterprise firewall and SD‑WAN integration |
| Check Point | Advanced firewalling and threat prevention |
| Barracuda | Cloud firewalling and security services |
| VMware | SD‑WAN and virtualization-centric network services |
Summary
- NVAs are third‑party VMs that provide network functions and can be attached to Azure Virtual WAN hubs.
- Navigate to Virtual WAN > Hubs > Network virtual appliances in the portal to create an NVA.
- Select a Marketplace vendor image, configure hub, scale units, licensing/token, and credentials, then review and create.
- Azure provisions the VM(s) and connects them into the hub routing fabric — always consult vendor documentation for sizing and licensing details.
Links and references
- Azure Virtual WAN documentation
- Azure Marketplace
- Vendor docs (example):
- Fortinet: https://www.fortinet.com/
- Barracuda: https://www.barracuda.com/
- Cisco: https://www.cisco.com/
- Check Point: https://www.checkpoint.com/
- VMware SD‑WAN: https://www.vmware.com/products/sd-wan.html