What is an address space?
When you create an Azure VNet, the first step is defining its address space — the boundaries of your virtual network. Azure VNets use private IP ranges from RFC 1918. Choose a range that fits your scale and future growth.| RFC 1918 Range | Typical Use Case |
|---|---|
10.0.0.0/8 | Very large networks, extensive multi-subnet designs |
172.16.0.0/12 | Medium-sized networks with multiple segments |
192.168.0.0/16 | Smaller networks, labs, or simple deployments |
10.1.0.0/16 as your VNet address space gives you 65,536 addresses, which you can subdivide into many subnets.
Azure also exposes a special platform-managed IP address used by services like DNS and DHCP relays: 168.63.129.16. Do not assign this address to your resources.
Azure reserves the first four and the last IP address of each subnet for platform operations. That means you effectively lose five IPs per subnet — plan subnet sizes accordingly.
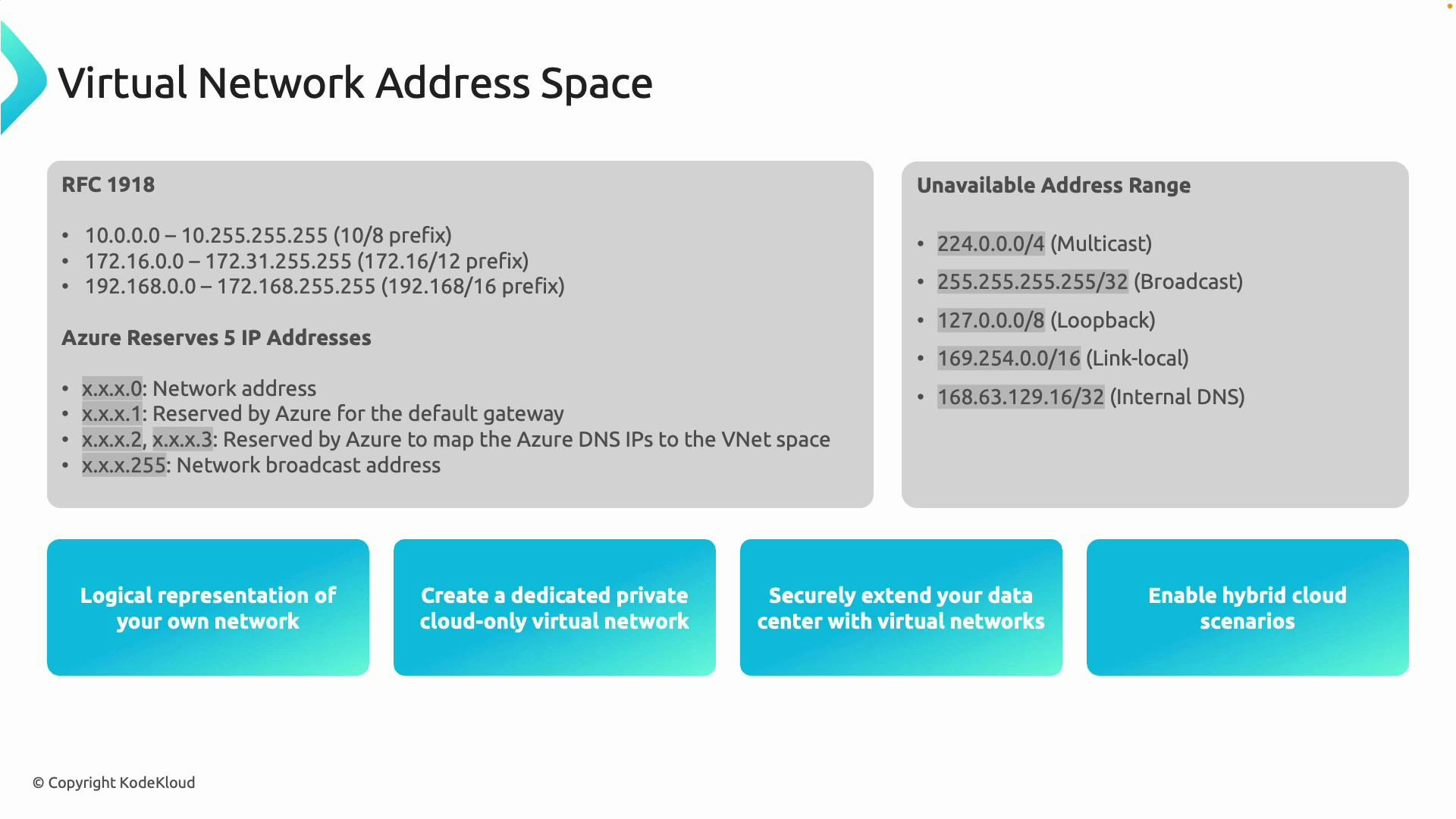
Azure platform reservations and unusable addresses
Azure reserves five IP addresses in every subnet for platform use (the first four and the last address). For example, a/24 subnet contains 256 addresses but only 251 are usable for your VMs and resources.
Commonly blocked or special-purpose ranges you should not use in VNets include:
- Multicast ranges
- Loopback ranges
- Link-local ranges
- Broadcast addresses
- The Azure-managed address
168.63.129.16(platform services)
Do not assign
168.63.129.16 or any special-purpose ranges to your resources. Azure requires these for platform services (DNS, DHCP relays, health probes). Plan your address ranges to avoid conflicts.What are subnets?
A subnet is a subdivision of your VNet address space. Subnets let you organize, isolate, and secure resources — similar to dividing a city into neighborhoods. Example (VNet10.1.0.0/16 split into subnets):
10.1.10.0/24— web servers (subnet0)10.1.20.0/24— databases (subnet1)10.1.30.0/24— management tools (subnet2)GatewaySubnet— required for VPN GatewayAzureBastionSubnetorAzureFirewallSubnet— service-specific placement
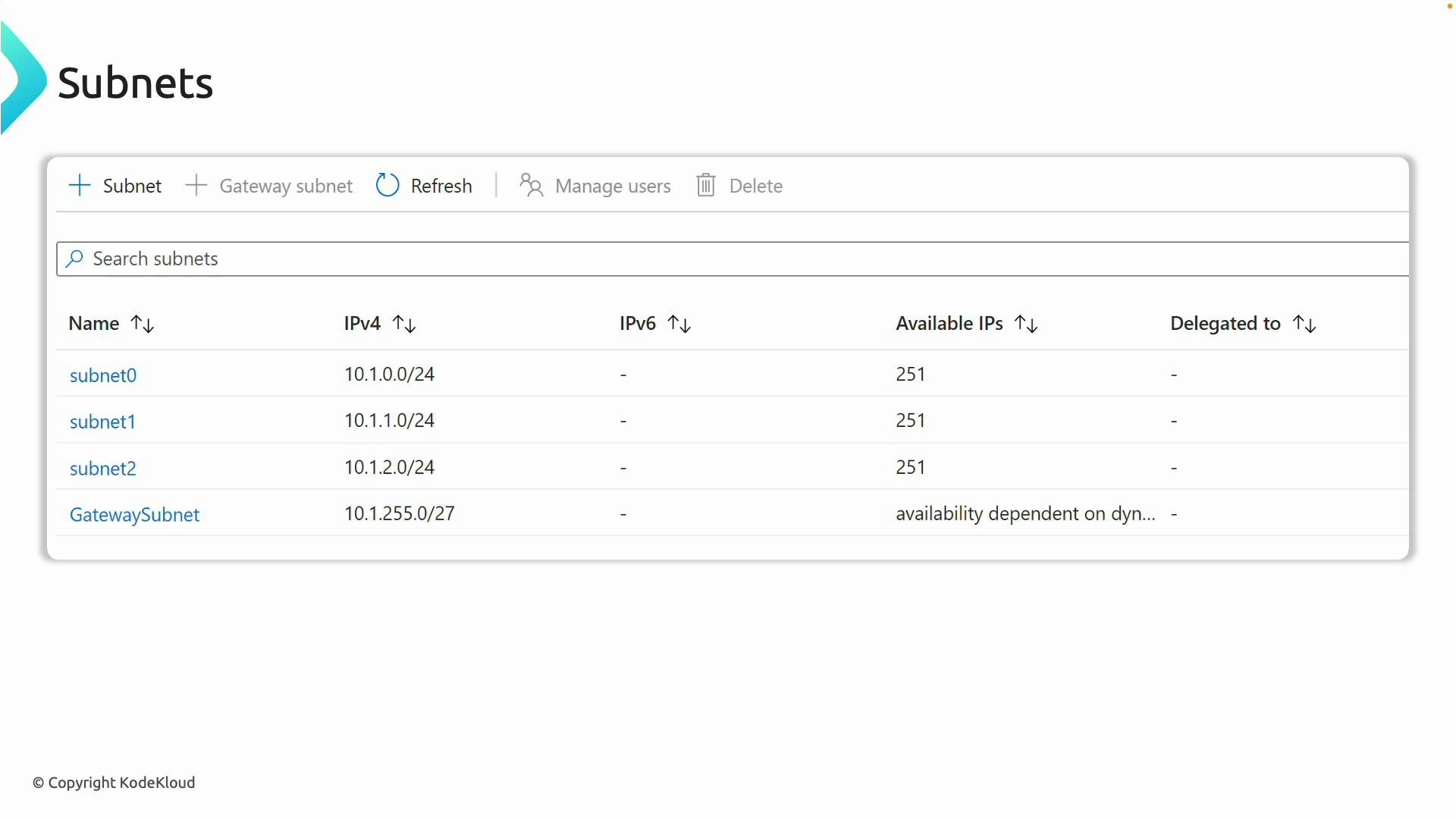
Service-specific subnets
Some Azure services require dedicated subnets and naming conventions:- GatewaySubnet — required for VPN Gateway and ExpressRoute gateway
- AzureFirewallSubnet — used by Azure Firewall
- AzureBastionSubnet — used by Azure Bastion
- Other services may also require dedicated subnets (check each service’s docs)
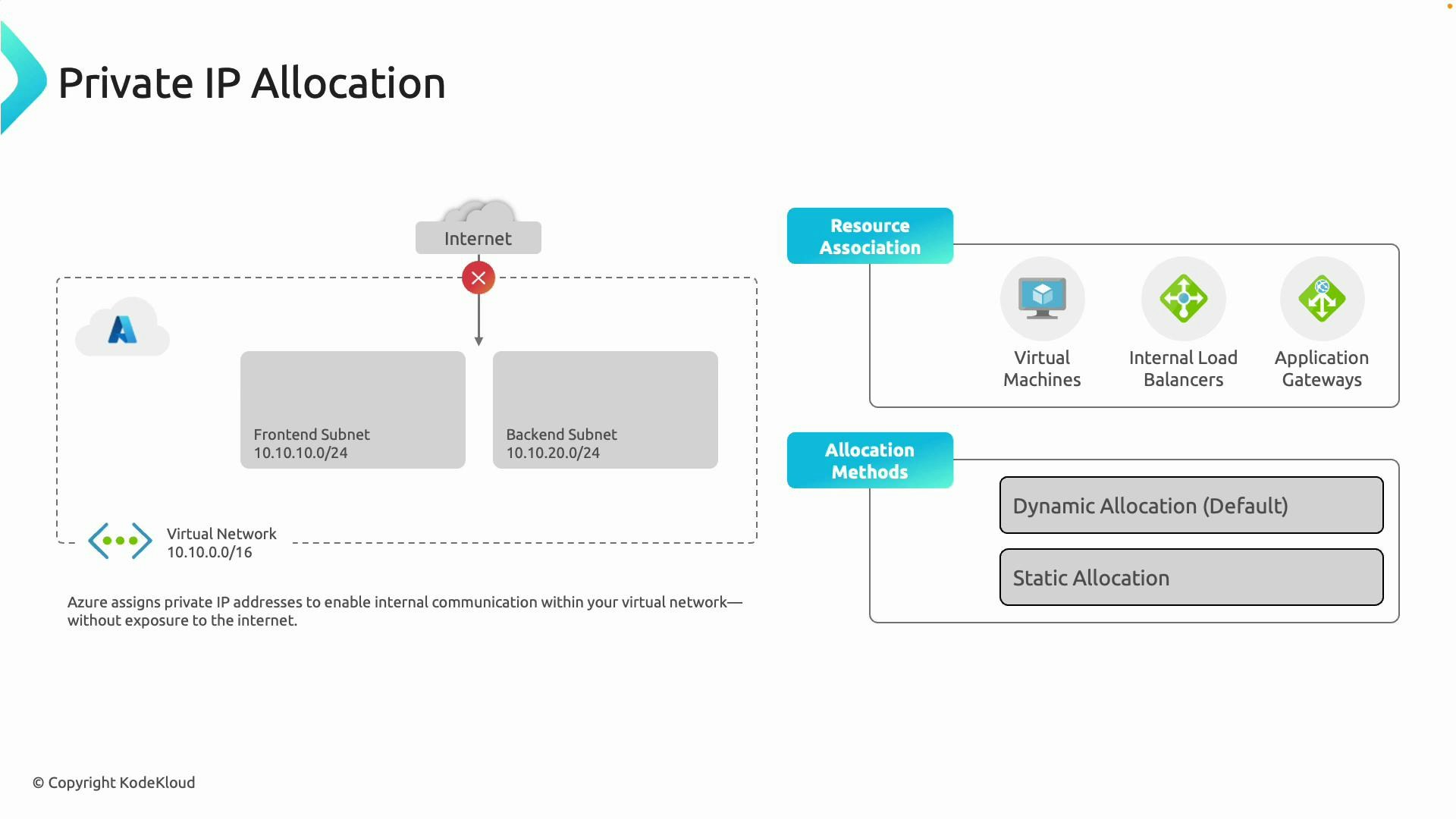
Private IP allocation: dynamic vs static
Resources in a VNet (VMs, internal Load Balancers, Application Gateways, etc.) receive private IPs from the subnet. Allocation methods:- Dynamic (default): Azure assigns the next available IP from the subnet’s DHCP pool when the resource is created. Good for most workloads.
- Static: You assign a fixed private IP (within the subnet CIDR). Use this when other components require a known IP (e.g., database endpoints or static backend pools).
Planning checklist
Use this checklist when designing VNet addressing and subnets:| Task | Recommendation |
|---|---|
| Choose RFC range | Pick 10.0.0.0/8, 172.16.0.0/12, or 192.168.0.0/16 based on scale |
| Subnet sizing | Account for Azure reserving 5 IPs per subnet; pick CIDRs that provide sufficient usable IPs |
| Service subnets | Reserve dedicated subnets for Gateway, Firewall, Bastion, etc. |
| Avoid conflicts | Ensure non-overlapping ranges for VNet peering and on-prem connectivity |
| IP allocation | Use dynamic IPs by default; assign static IPs where a fixed address is required |
| Reserved addresses | Never assign 168.63.129.16 or special-purpose ranges to resources |
Summary
- Define the VNet address space first using RFC 1918 ranges.
- Subdivide into subnets for organization, security, and service placement.
- Azure reserves five IP addresses per subnet; design sizes accordingly.
- Avoid special-purpose ranges and the Azure-managed address
168.63.129.16. - Use dynamic allocation for most resources and static allocation when necessary.
- RFC 1918 — Address Allocation for Private Internets
- Azure special IP 168.63.129.16 documentation
- Azure Virtual Network documentation