Why use Network Watcher?
Azure Network Watcher centralizes regional network diagnostics and monitoring. It helps you map topology, validate connectivity, inspect packet flows, capture traffic for analysis, and export telemetry into Azure Monitor and Log Analytics. These capabilities are especially useful for hybrid or multi-region deployments, security investigations, and operational troubleshooting.Tool overview
Below is a quick reference of the core Network Watcher tools and their common use cases.| Tool | Primary use case | Output / Storage |
|---|---|---|
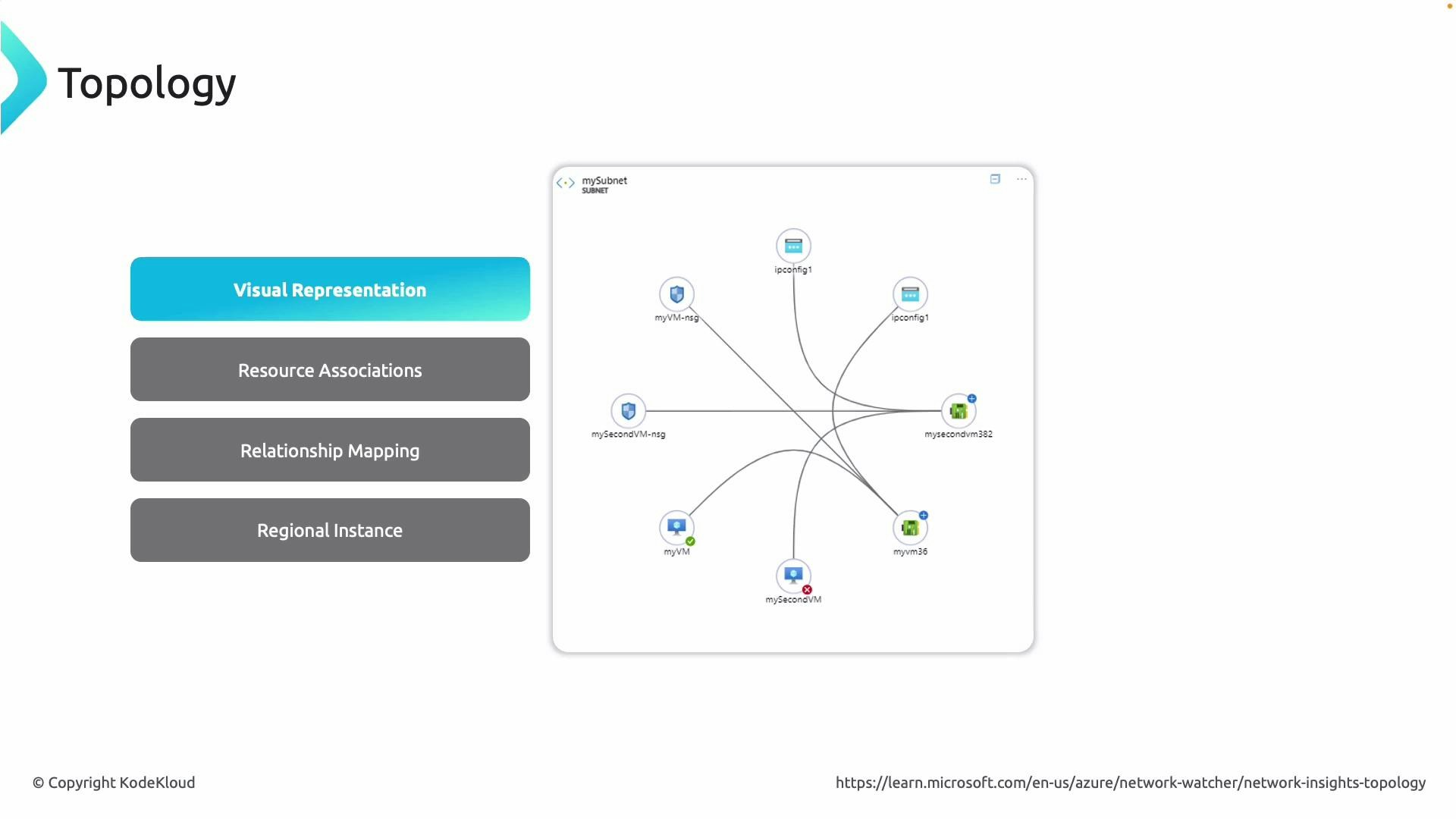
| Topology | Visualize VNets, subnets, NICs, NSGs, IP configurations, and resource relationships | Portal topology map (regional) |
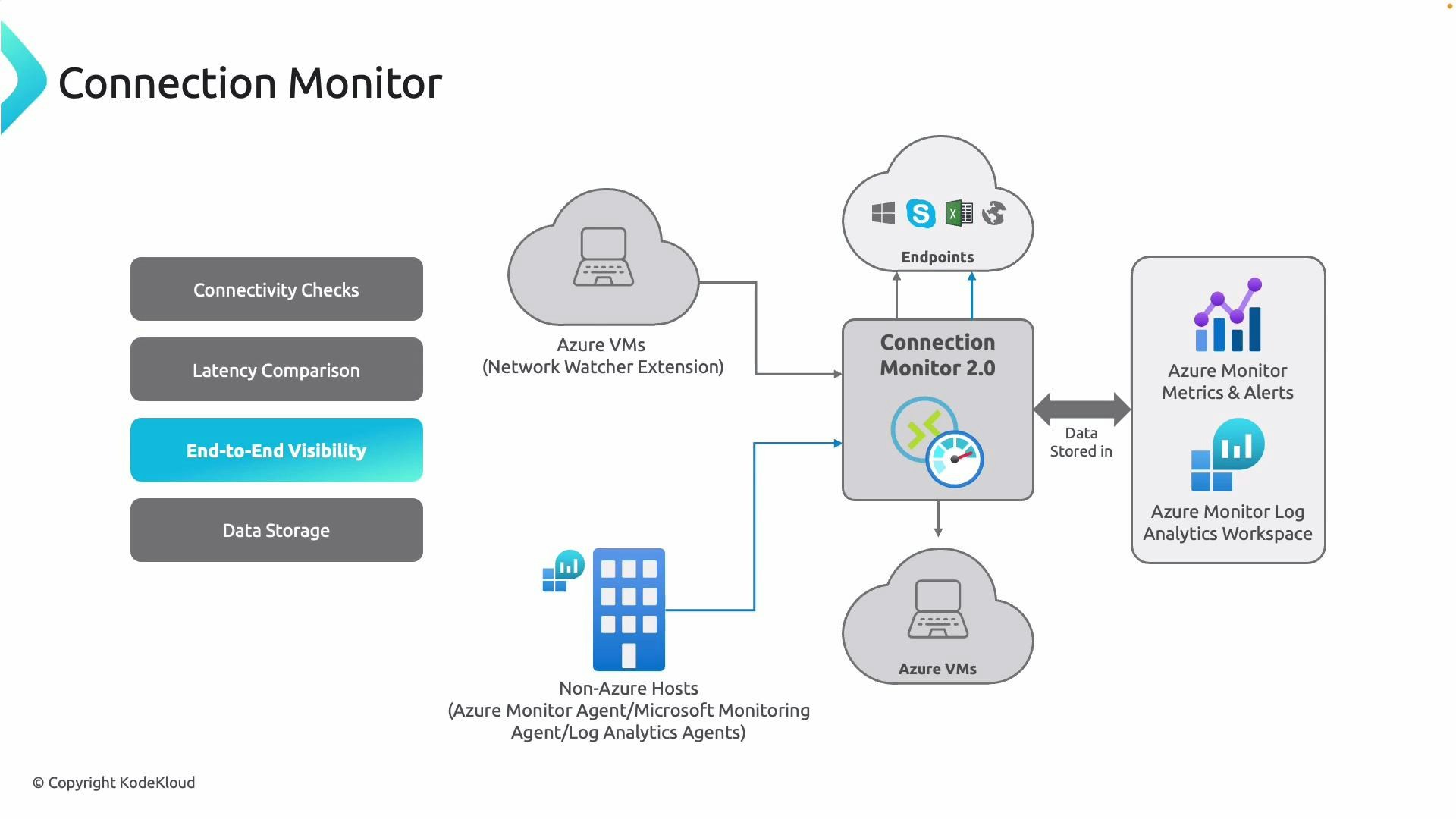
| Connection Monitor | Continuous connectivity checks (latency, packet loss) between endpoints | Azure Monitor metrics, Log Analytics |
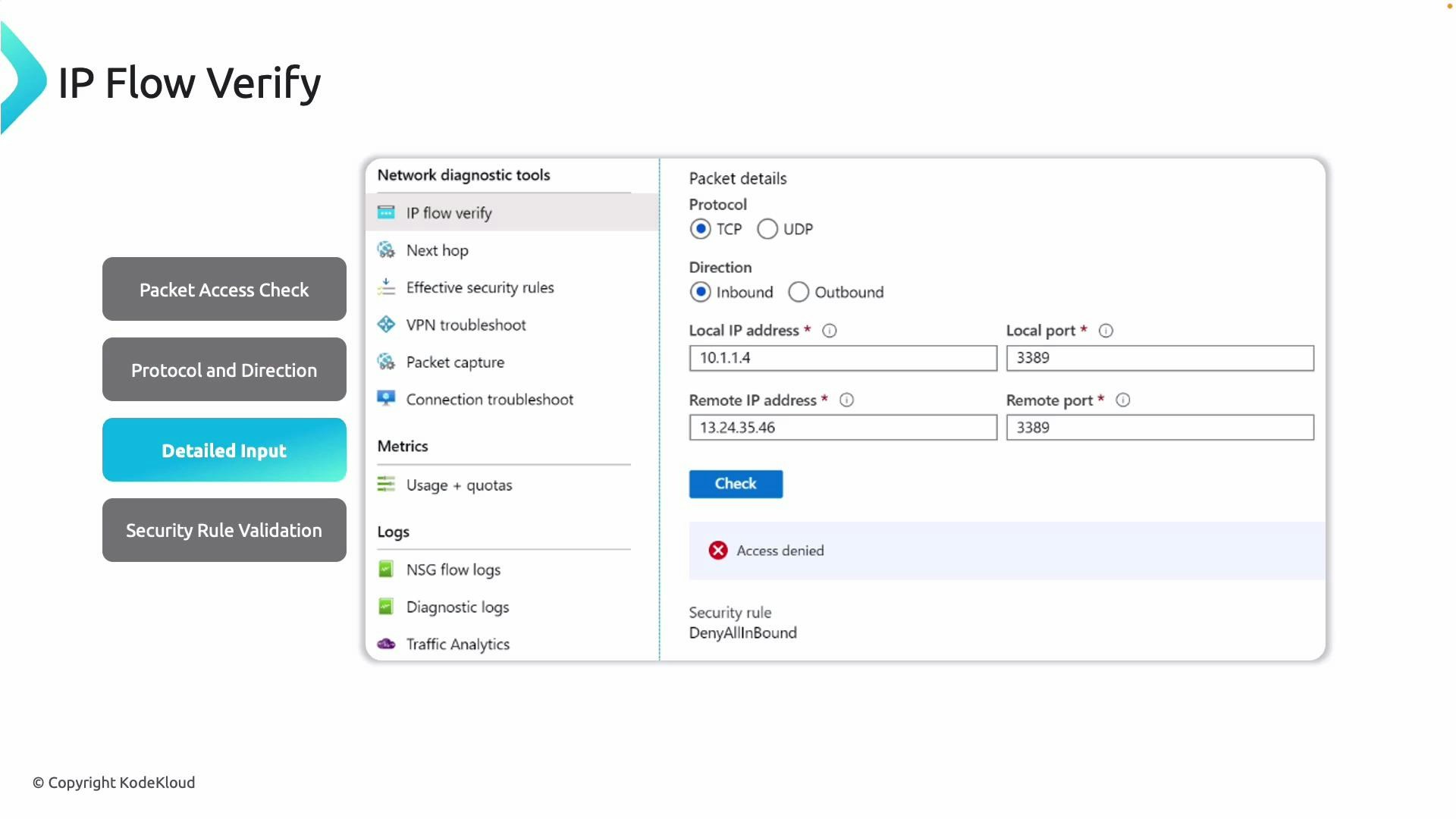
| IP Flow Verify | Simulate a packet flow to determine Allow/Deny against NSG rules | Immediate result + matching NSG rule |
| NSG Diagnostics | Evaluate effective NSG rules on NIC or subnet; explain allow/deny decisions | Rule evaluation report |
| Next Hop | Determine next hop type and whether system routes or UDRs are applied | Next hop type & route table info |
| VPN Troubleshoot | Diagnose site-to-site and P2S VPN issues and route behavior | Diagnostic output saved to storage |
| Packet Capture | Capture raw packets from a VM for offline analysis (tcpdump/Wireshark style) | PCAP files in Storage Account |
| Connection Troubleshoot | End-to-end and hop-by-hop connectivity checks | Hop list, NSG checks, latency/port checks |
| Flow Logs (NSG) | Record allow/deny flow data for NSGs | Storage Account, optionally Log Analytics |
| Traffic Analytics | Visualize and analyze aggregated flow logs | Log Analytics solution dashboards |
Network Watcher features are region-scoped. Some features require the Network Watcher resource to be enabled in the same region as the resources you test. Appropriate RBAC (e.g., Reader or Network Contributor) is required to run diagnostic tools.
Detailed tool descriptions
Topology- Purpose: Generates a regional visual map of networking elements in a VNet (VMs, NICs, subnets, NSGs, IP configurations, private endpoints, public IPs, etc.).
- When to use: Understand resource relationships and dependencies when troubleshooting complex connectivity or routing issues.
- Note: Topology is region-specific — enable Network Watcher in the same region as the VNet you want to map.
- Purpose: Performs continuous connectivity checks between endpoints (VM-to-VM, on-premises-to-Azure, cross-region).
- Telemetry: Measures latency and packet loss over time and stores results in Azure Monitor metrics and a Log Analytics workspace for historical tracking and alerting.
- Best practice: Use for SLA verification, synthetic monitoring, and tracking intermittent cross-region or hybrid connectivity issues.
- Purpose: Simulates a packet through NSG rules to show whether a specific flow (TCP/UDP, inbound/outbound) would be allowed or denied.
- Inputs: Source/destination IPs and ports, protocol, and direction.
- Output: Access result and the matching NSG rule(s) that caused the decision.
- Purpose: Lists effective NSG rules applied to a NIC or subnet (inherited and custom), shows evaluation order/priority, and explains why a flow was allowed or denied.
- When to use: Troubleshoot conflicting rules, unintended deny statements, or when a VM cannot reach an endpoint despite expected rules.
- Purpose: Diagnose VPN gateway issues for site-to-site and point-to-site connections.
- Capabilities: Validates routing/next hop behavior for VPN traffic, detects misconfigurations and tunnel issues.
- Output: Diagnostic data saved to a storage account for offline analysis and deeper troubleshooting.

- Purpose: Capture raw packet-level traffic on a VM (similar to tcpdump or Wireshark).
- Filters: Target VM, protocol, IP, or port. Useful for investigating latency issues, dropped connections, or suspicious traffic.
- Storage: Captures save to an Azure Storage account; you can download PCAP files for offline analysis.

- Purpose: End-to-end connectivity tests with hop-by-hop analysis. Includes NSG diagnostics, next hop, path visualization, port checks, and latency measurements.
- Use case: Isolate the network hop where connectivity fails and obtain actionable diagnostics to remediate the issue.

- Purpose: Record NSG-level traffic flows (inbound/outbound) including source/destination IPs, ports, protocol, and the action (Allow/Deny).
- Storage and integration: Flow logs are written to an Azure Storage account and can be forwarded to Log Analytics or SIEM solutions for analysis.

- Purpose: A Log Analytics solution that ingests NSG Flow Logs and provides visualizations, traffic patterns, hotspot detection, and security insights.
- Best practice: Centralize flow logs from multiple regions into a Log Analytics workspace for cross-region analysis and threat hunting.

Using Network Watcher in the Azure portal — step-by-step
- Open the Azure portal and search for “Network Watcher”.
- Select a Network Watcher instance in the same region as the resources you will analyze. The diagnostic tools will appear in the left-hand menu.
- Select IP Flow Verify.
- Choose the target VM and network interface.
- Enter local IP/port, remote IP/port, direction (inbound/outbound), and protocol.
- Run the check — the result shows Allow/Deny and the NSG rule that matched.

- Choose the VM or NIC and run NSG diagnostics by specifying source/destination and port.
- The tool simulates the flow, lists evaluated rules in priority order, and indicates which rule (if any) matched and the resulting action.

- Use Next Hop to discover the next hop type (Internet, VirtualAppliance, VirtualNetworkGateway, VirtualNetwork, VnetLocal, None) and to confirm whether system routes or user-defined routes are being used.

- Select the VPN gateway resource, specify a storage account for diagnostics, and run the troubleshoot job.
- Review the saved output to analyze tunnel status, connection health, and routing for site-to-site or point-to-site VPNs.
- Select Add packet capture.
- Choose the target VM, set a capture name and storage location, and optionally add packet filters (protocol, local/remote IP/port).
- Specify max capture size and duration, then start the capture. Download PCAP files from the storage account for offline analysis.

Packet capture requires the VM agent/extension to be installed on the target VM and may collect sensitive data. Captures and diagnostic storage can incur costs — ensure compliance, access controls, and retention policies are followed.
- Select the source VM and specify the destination (resource URI, FQDN such as https://www.microsoft.com, or IP address).
- Choose protocol (TCP/ICMP), destination port, and which checks to run (connectivity, NSG diagnostics, next hop, port scan).
- Examine results: reachability, probe statistics (sent/failed), average/max latency, and a detailed hop-by-hop path that highlights where failures occur.

- Enable Flow Logs on an NSG and choose a storage account to retain flow data. Optionally route logs to a Log Analytics workspace for analysis.
- Use Traffic Analytics (Log Analytics solution) to visualize and analyze flow logs: identify traffic trends, hotspots, and security-related events across regions when logs are centralized.

Best practices and tips
- Enable Network Watcher in each region where you need diagnostics.
- Centralize Flow Logs into a Log Analytics workspace for unified analysis and Traffic Analytics.
- Limit packet capture retention and control access to storage accounts to minimize exposure of sensitive data.
- Combine Connection Monitor for continuous telemetry with Connection Troubleshoot for on-demand hop debugging.
- Use IP Flow Verify and NSG Diagnostics before making NSG changes in production to reduce risk.