- Regions: VNets are deployed into a specific Azure region (for example, West Europe, East US). Choose a region close to your users to reduce latency.
- Subscriptions and resource groups: Every Azure resource lives inside a subscription. Use resource groups to organize related resources (for example: development, testing, production).
- Global networking and peering: Virtual network peering connects VNets across regions and/or subscriptions for private, low-latency connectivity.
- Region determines data residency and latency.
- Subscriptions control billing, quotas, and access boundaries.
- Peering and global networking design affect addressing, security, and operational complexity.
| Resource Type | Purpose | Example use |
|---|---|---|
| Region | Place resources close to users | Deploy VMs in West Europe for EU users |
| Subscription | Billing & isolation | Separate production vs. dev billing |
| Resource group | Logical grouping | Group a web app and its database |
| VNet peering | Private connectivity across VNets | Connect dev and test VNets without public endpoints |
Step 1 — Start the VNet creation wizard
- Sign in to the Azure portal (portal.azure.com).
- Search for “Virtual Network” and open the Virtual Networks service.
- Click Create (or Create + Add) to start the guided setup where you’ll supply subscription, region, resource group, and instance details.
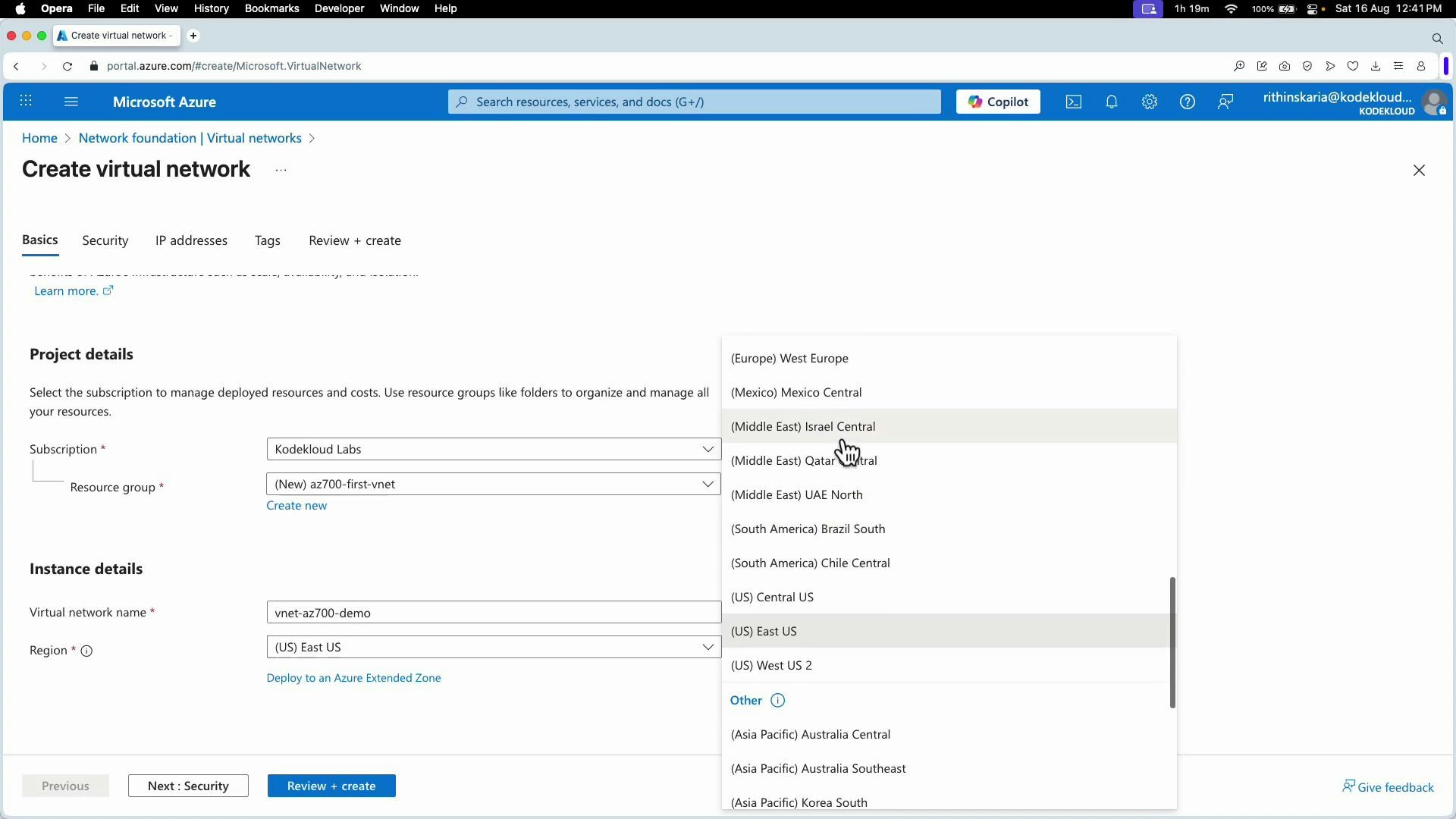
Step 2 — Choose subscription, resource group, name, and region
- Select the subscription that will be billed.
- Create or select a resource group (for example: az700-first-VNet).
- Give the VNet a clear name (for example: VNet-az700-demo).
- Choose the Azure region to host the VNet (for example: West Europe).
Step 3 — Review optional security features
On the Security tab you can opt into managed services such as:- Azure Bastion (secure browser-based RDP/SSH to VMs)
- Azure Firewall
- Azure DDoS Protection
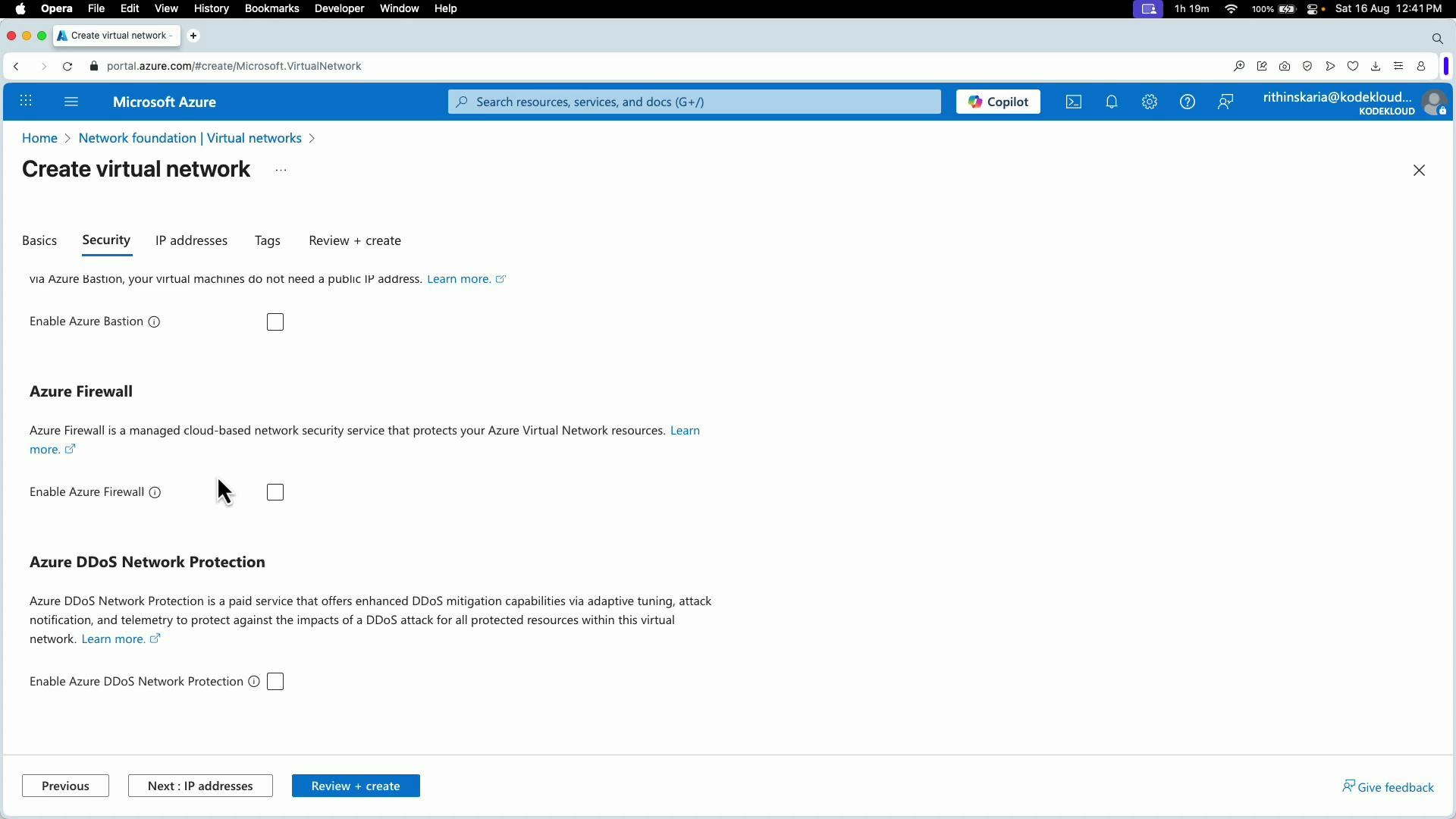
Some Azure services require specific subnet names (for example, GatewaySubnet for VPN/ExpressRoute gateways) and minimum prefix sizes. If you plan to enable managed gateways or firewall services, reserve appropriately sized subnets and correct names up front to avoid migration complexity later.
Step 4 — Define address space and subnets (IP addresses)
- Open the IP addresses tab to set the VNet address space and internal subnets.
- The portal often suggests a default address space (10.0.0.0/16). Replace or extend it to match your IP plan (for example 192.168.0.0/16).
- A VNet can have multiple CIDR blocks (add additional address spaces later if needed). Avoid overlaps if you plan to peer or connect to on-premises networks.
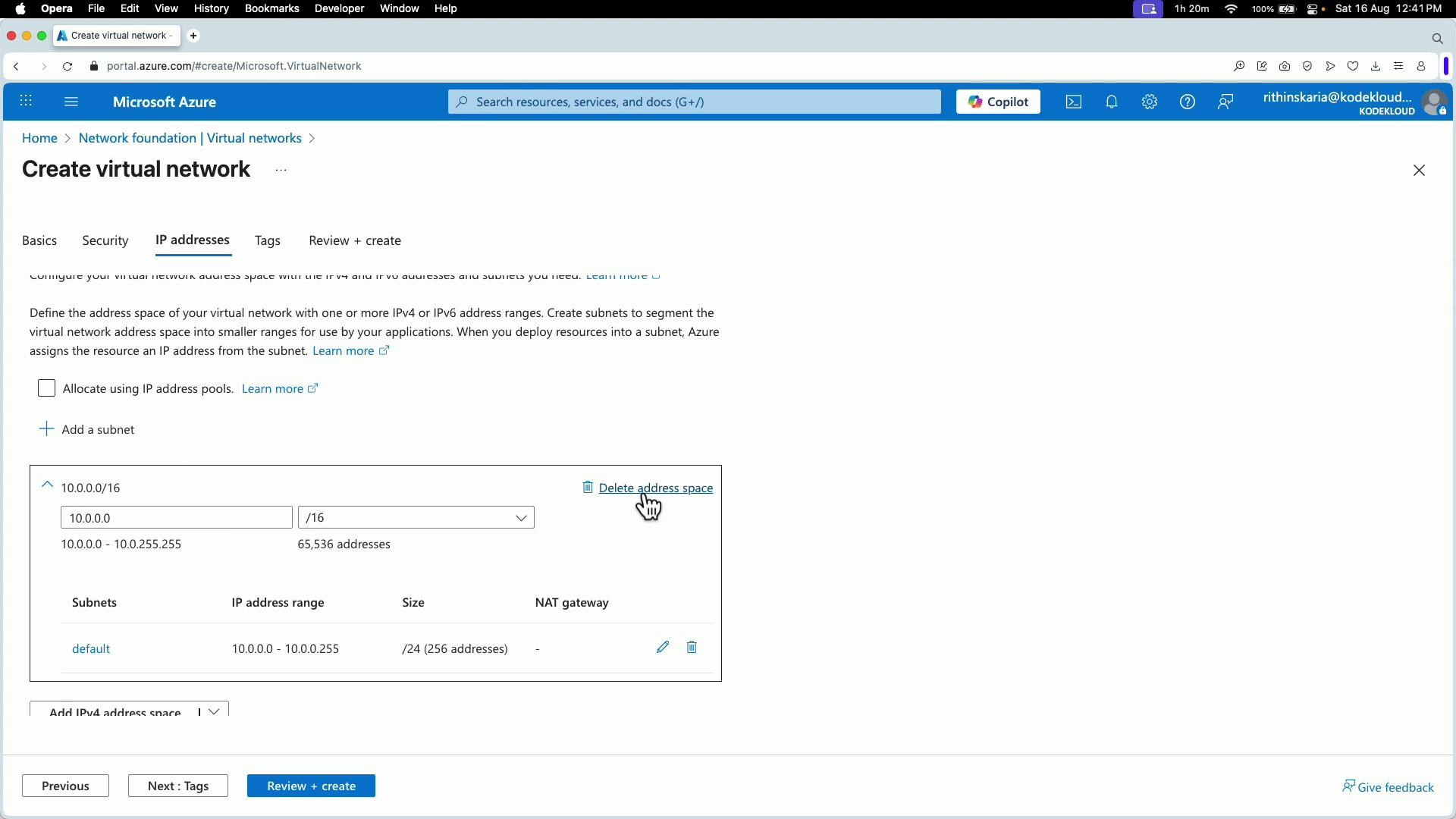
- Click Add subnet to create subnets inside your VNet address space.
- Example subnets:
- SNET-web-servers → 192.168.0.0/27 (32 addresses)
- SNET-DB → 192.168.0.32/28 (16 addresses)
Azure reserves 5 IP addresses per subnet for platform use (the first four IPs and the last IP in each subnet). When planning capacity, subtract 5 from the subnet’s total addresses to determine usable IPs.
| Prefix | Total addresses | Usable addresses (Azure) |
|---|---|---|
| /24 | 256 | 251 |
| /27 | 32 | 27 |
| /28 | 16 | 11 |
| /29 | 8 | 3 |
- You can add more IPv4 address spaces to a VNet later; VNets are not limited to a single CIDR block.
- Always plan for growth and avoid address overlaps when peering or connecting to on-premises networks.
Step 5 — Review and create
- Click Review + create to validate your configuration.
- Azure will run validation checks; if validation passes, click Create to deploy the VNet.
- Click Go to resource to open the VNet blade.
- Under Subnets you’ll see each subnet and available IP addresses (usable = total − 5 reserved).
- From the VNet blade you can later configure:
- Network Security Groups (NSGs) for subnet- or NIC-level filtering
- User-defined route tables
- Service endpoints and private endpoints
- Virtual network peering
- Bastion host, Azure Firewall, DDoS protection, and gateway subnets
- Choose region and subscription based on latency and billing.
- Use consistent naming conventions for VNet and subnets.
- Reserve appropriately sized subnets for managed services (GatewaySubnet, Azure Firewall).
- Plan IP addressing to avoid overlaps with on-premises networks or other VNets you will peer.
- Apply NSGs and route tables to control traffic flow and enforce least privilege.