What Private Peering Does
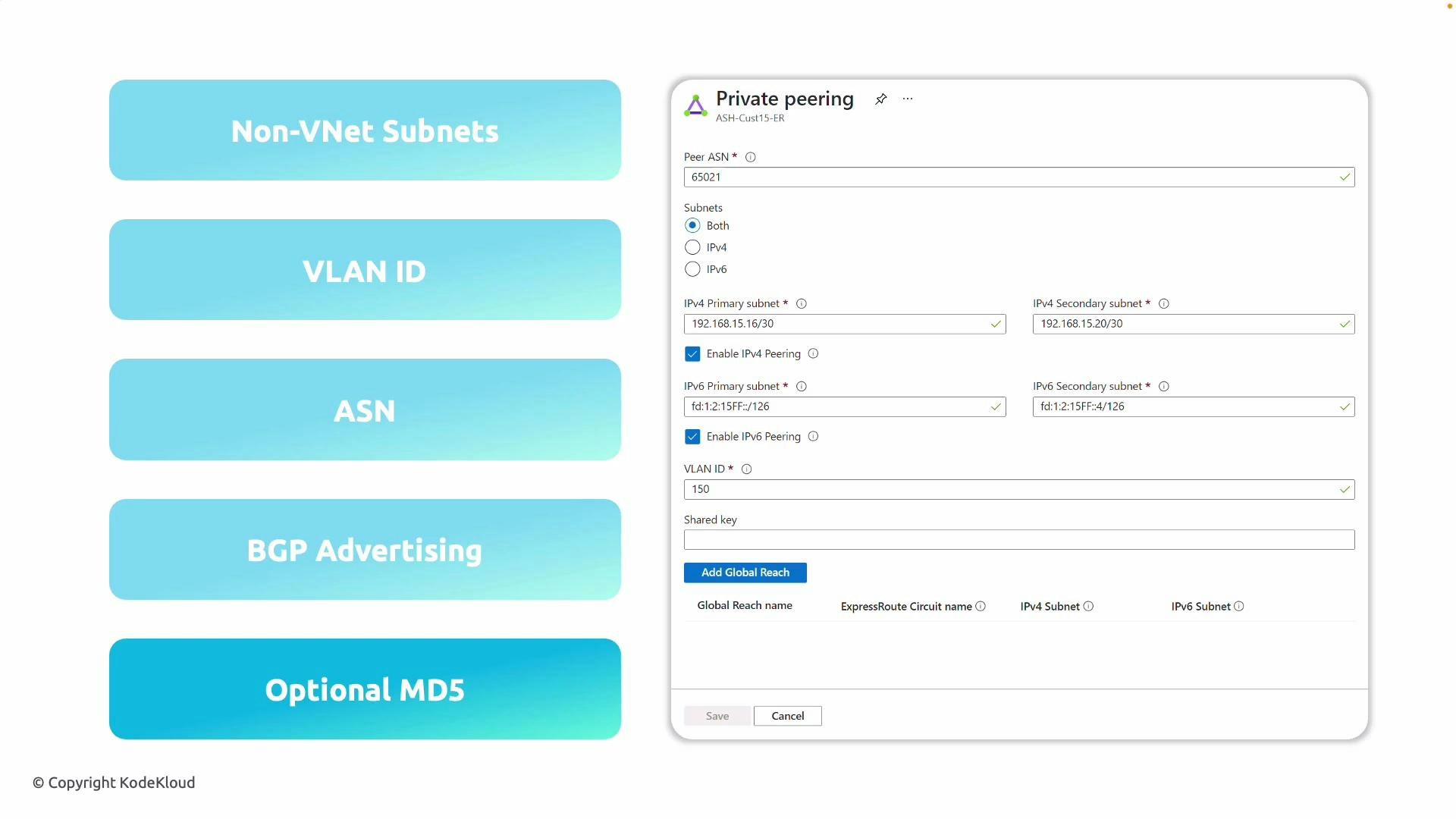
Private peering establishes a dedicated, private network path between your on-premises network and your Azure Virtual Networks (VNets) over ExpressRoute. It uses BGP to exchange routes and requires careful alignment of addressing, VLAN tagging, ASN settings, and (optionally) BGP authentication.Key fields you configure in the portal
When you open the ExpressRoute circuit and select the Private peering tab, you’ll supply several technical details required to establish the BGP sessions. These typically include:- Non‑VNet subnets (BGP peer IPs)
- VLAN ID
- Peer ASN (Autonomous System Number)
- BGP route advertisement configuration
- Optional BGP MD5 authentication
- Optional Global Reach settings
| Field | Purpose | Recommended values / notes |
|---|---|---|
| Non‑VNet subnets (BGP peer IPs) | Point-to-point IPs used for the session between Microsoft Edge and your router | Use a pair of IPv4 /30 subnets (primary and secondary for redundancy). For IPv6, use appropriate prefix (commonly /126). Ensure these do not overlap any VNet or on-prem CIDR. |
| VLAN ID | Layer‑2 tag used on the circuit interface | Match the VLAN configured on your on-prem equipment or provider. |
| Peer ASN | ASN presented by your side of the BGP session | Use your on-prem ASN (2-byte or 4-byte supported), or the ASN your provider specifies if they manage the peering. |
| BGP advertising | Routes you will advertise to Azure | Advertise only the prefixes you want reachable in Azure; avoid overlapping or overly broad prefixes. |
| BGP MD5 (optional) | Session authentication for BGP | Enable where supported; coordinate the password with the Microsoft side. |
| Global Reach (optional) | Interconnects multiple on-prem sites via Azure backbone | Enable if you need site-to-site connectivity across different ExpressRoute circuits and providers support it. |
Step-by-step: What to enter in the portal
- In the ExpressRoute circuit, open the Private peering tab.
- Enter the Peer ASN — the ASN your on-premises router will use.
- Provide the IPv4 point-to-point subnets:
- Primary session: assign one /30 (two usable addresses).
- Secondary session: assign a second /30 for redundancy.
- (Optional) Add IPv6 point-to-point prefixes if using IPv6 (commonly /126).
- Enter the VLAN ID that matches your on-prem VLAN configuration.
- Configure which routes you will advertise (this determines what becomes reachable in Azure).
- (Optional) Enable BGP MD5 and enter the session password if you and Microsoft coordinate MD5 usage.
- (Optional) Enable Global Reach if you plan to interconnect on-prem sites via the Microsoft backbone and your provider supports it.
- Save the configuration and verify coordination with your provider or operations team.
On‑premises configuration checklist
Before activating the peering on Microsoft’s side, ensure your on-premises (or provider) configuration matches exactly:- VLAN ID is identical on both ends.
- BGP peer IP addresses match the Azure-provided /30 addresses.
- Peer ASN is set correctly (2-byte or 4-byte as applicable).
- BGP timers and hold times are compatible.
- BGP MD5 password (if used) is configured on both sides.
- Route filters or route-map policies align with advertised/accepted prefixes.
- No IP address or route overlaps with existing VNets or on‑prem ranges.
Ensure the /30 subnets you use for the BGP peering IPs do not overlap with any existing VNet address spaces or on-premises networks. Overlap will prevent proper routing and can cause connectivity failures.
Example BGP neighbor configuration snippets
Cisco IOS example:Output:
Output:
Security and resiliency considerations
- Use BGP MD5 when your router platform and the Microsoft side support it to mitigate session reset attacks.
- Advertise only the prefixes you intend Azure to reach — filter overly broad or overlapping prefixes.
- Deploy primary and secondary peering sessions (different subnets) to provide router-level redundancy.
- Consider Global Reach if you require private connectivity between multiple on-prem sites via Azure’s backbone.
Troubleshooting tips
- If the BGP session fails to come up, verify VLAN ID, peer IPs, and ASNs match exactly.
- Check for IP overlaps; duplicate subnets prevent proper routing.
- Confirm BGP timers, hold times, and authentication match.
- Review route advertisements and inbound route filters on both sides.
- Use Azure Network Watcher and your router’s BGP show commands to inspect session state and received routes.
Links and references
- ExpressRoute private peering – Azure Documentation
- ExpressRoute Global Reach – Azure Documentation
- BGP MD5 Authentication – RFC 2385 (concept)