-
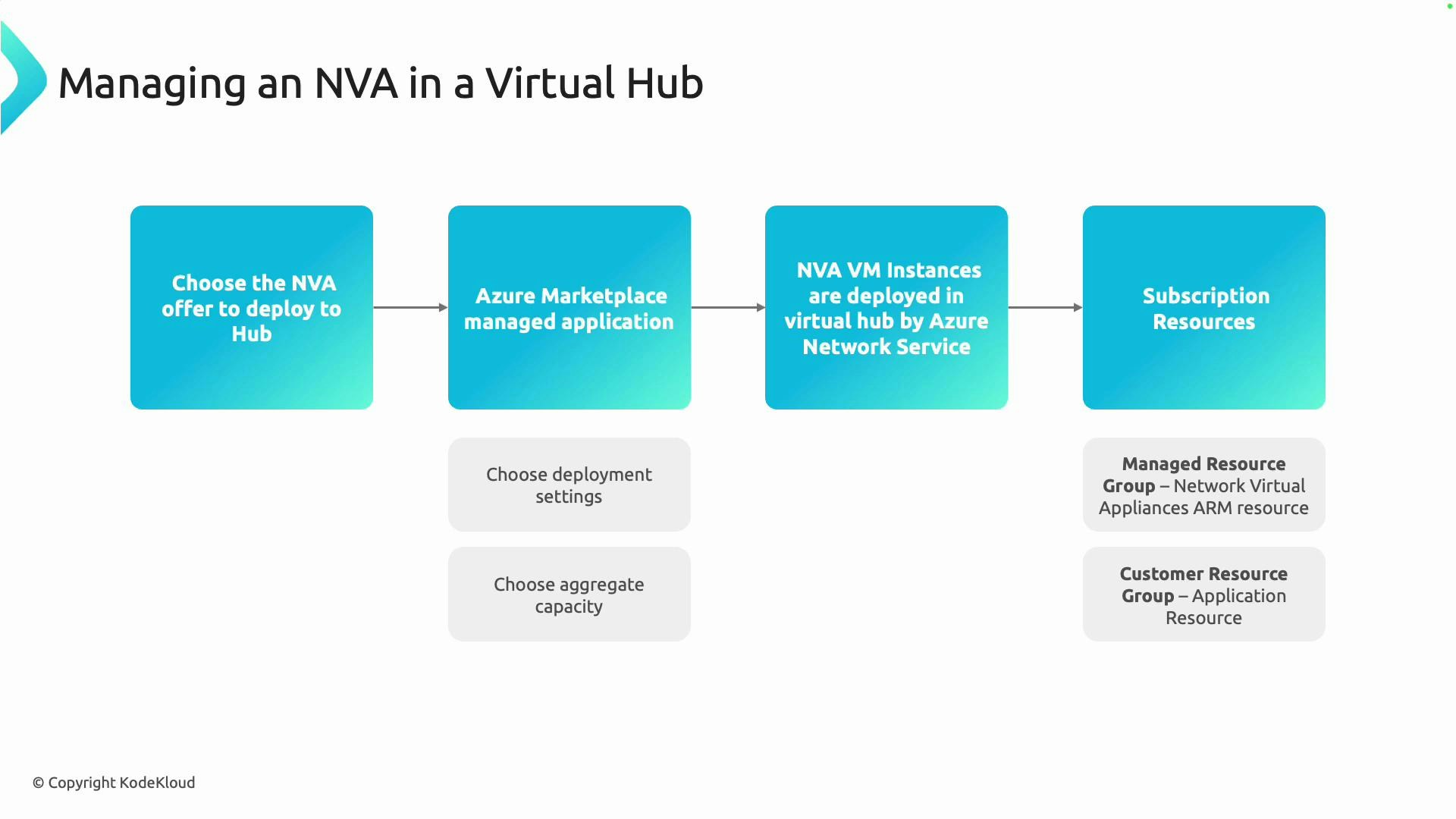
Choose an NVA offer
- Select an NVA that matches your security, routing, and network requirements. The Azure Marketplace provides Microsoft and third-party appliances — firewalls, routers, VPN/SD-WAN devices, and more.
- Check supported features such as throughput, high-availability (HA) options, licensing model, and platform compatibility so the appliance meets your expected traffic and resiliency needs.
-
Deploy as a managed application from Azure Marketplace
- Use the Marketplace managed application workflow to deploy the chosen NVA. Managed applications simplify provisioning and lifecycle management by encapsulating the appliance’s resources and operations.
- During deployment you’ll specify configuration options: VM size, instance count, licensing or bring-your-own-license (BYOL) settings, and any vendor-specific parameters.
-
Specify aggregate capacity and instance sizing
- Aggregate capacity is the total throughput or processing capacity you expect across all appliance instances (for example, aggregated firewall throughput).
- Consult vendor guidance to translate required aggregate capacity into instance count and VM SKUs. Account for headroom, CPU and NIC limits, and licensing constraints when sizing for peak traffic.
-
Azure provisions NVA VM instances into your Virtual Hub
- After Marketplace deployment, Azure provisions the appliance VM instances into the selected Virtual Hub. The NVA integrates with the hub’s routing and connectivity so traffic can be steered to the appliance for inspection or processing.
- Confirm your hub route configuration (hub route tables, route propagation, or custom routing rules) forwards the intended traffic flows to the NVA instances.
-
Resource organization in your subscription
- The managed-application deployment pattern separates vendor-managed artifacts from customer-managed resources for clarity and lifecycle isolation:
- Managed resource group: created and maintained by the managed application. Contains appliance VM instances, extensions, and other vendor-controlled resources.
- Customer resource group: holds your configuration artifacts, monitoring resources, or integration components that you manage.
- Use role-based access control (RBAC) and resource tagging to govern access and billing between these groups.
- The managed-application deployment pattern separates vendor-managed artifacts from customer-managed resources for clarity and lifecycle isolation:
| Resource Type | Purpose in an NVA deployment | Example / Notes |
|---|---|---|
| Managed resource group | Vendor-controlled artifacts and NVA instances | Contains VM instances, extensions, and resources owned by the managed application |
| Customer resource group | Customer-managed configuration and integration resources | Stores templates, automation, or configuration assets you own |
| Virtual Hub | Central connectivity plane for routing traffic to the NVA | Ensure hub route tables are configured to steer traffic to the appliance |
| Route tables / Policies | Control which traffic is inspected or processed by the NVA | Implement custom routes or route propagation as required |
When deploying NVAs as managed applications, do not modify resources directly inside the managed resource group—the managed application controls those resources. Make configuration changes through the vendor’s supported management interfaces or by managing resources placed in the customer resource group.
- Plan capacity and HA topology: design for active/active or active/passive operations according to vendor guidance and Virtual Hub capabilities.
- Verify routing and failover: test route propagation, traffic steering, and HA failover scenarios in a staging environment.
- Monitor and automate: integrate appliance telemetry with Azure Monitor, set alerts, and automate common tasks with Azure Automation or vendor-supplied tooling.
- Azure Virtual WAN and Virtual Hub overview
- Azure Marketplace
- Designing for NVA deployments and routing patterns