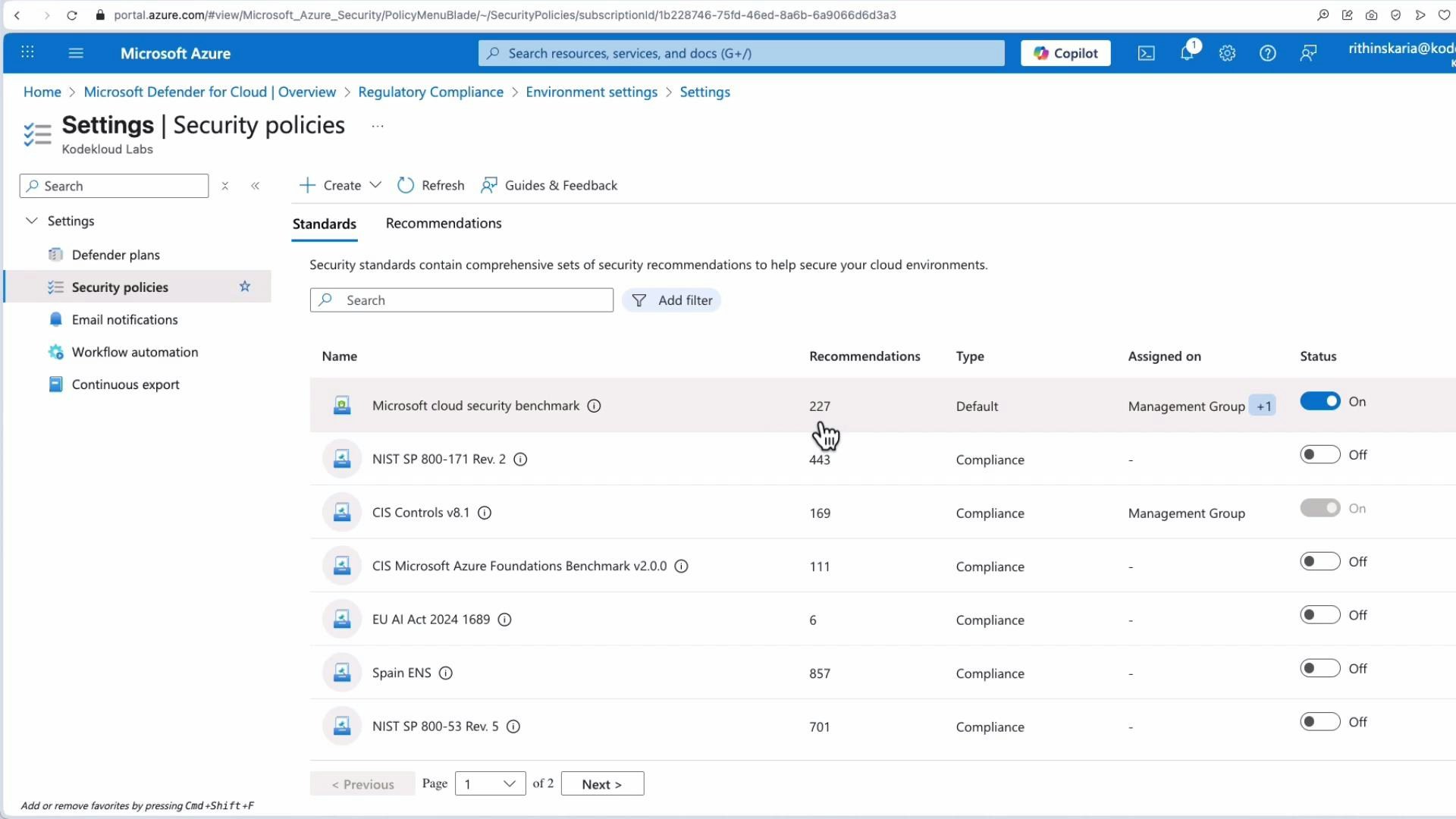
- Centralized compliance view across subscriptions and management groups
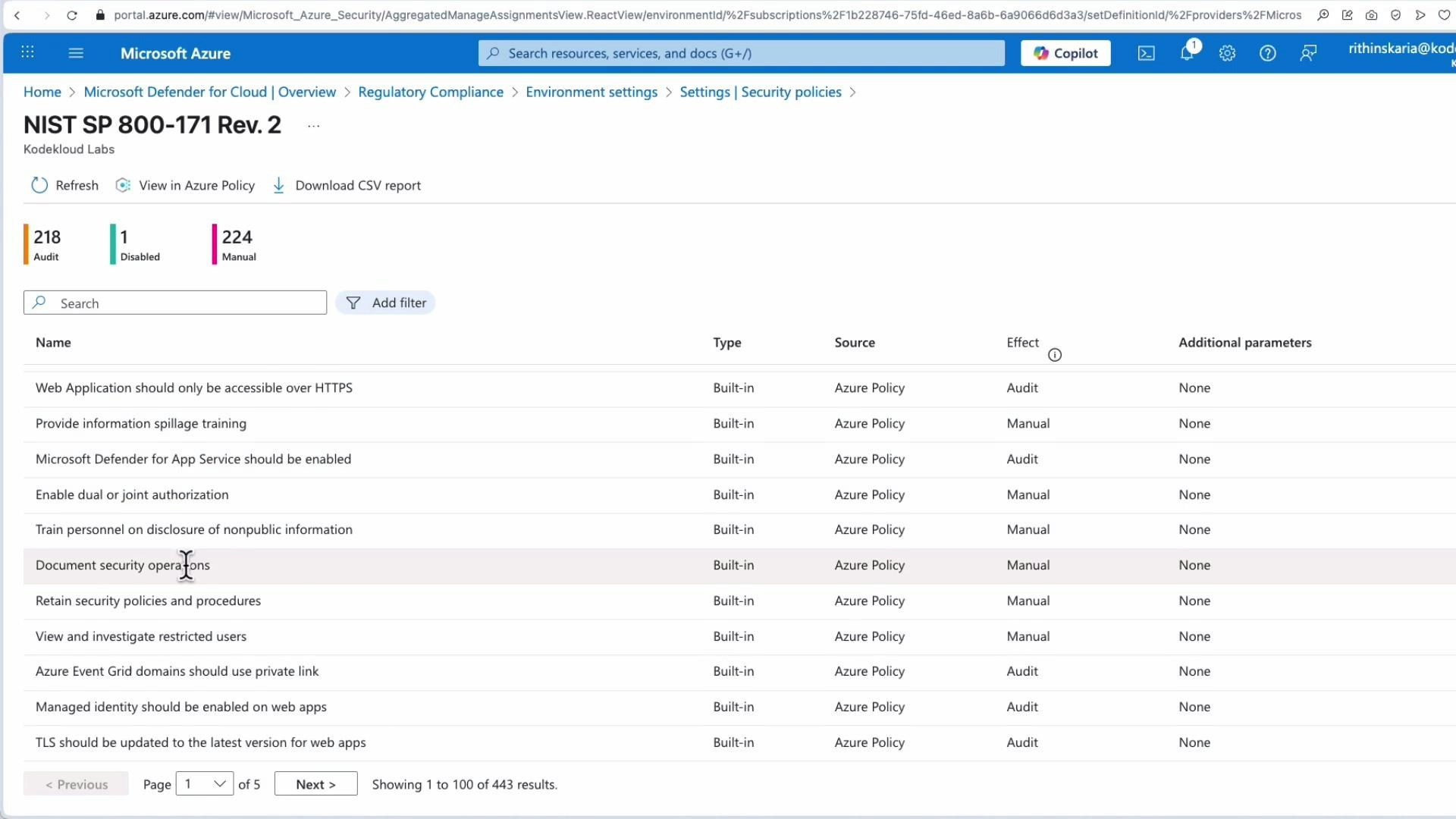
- Built‑in mappings to standards such as Azure Security Benchmark, PCI DSS, ISO/IEC 27001, NIST, and CIS
- Continuous assessment with Secure Score and Compliance score to help prioritize remediation
- Integrated alerts, investigation workflows, automation playbooks, and downloadable reports for auditors
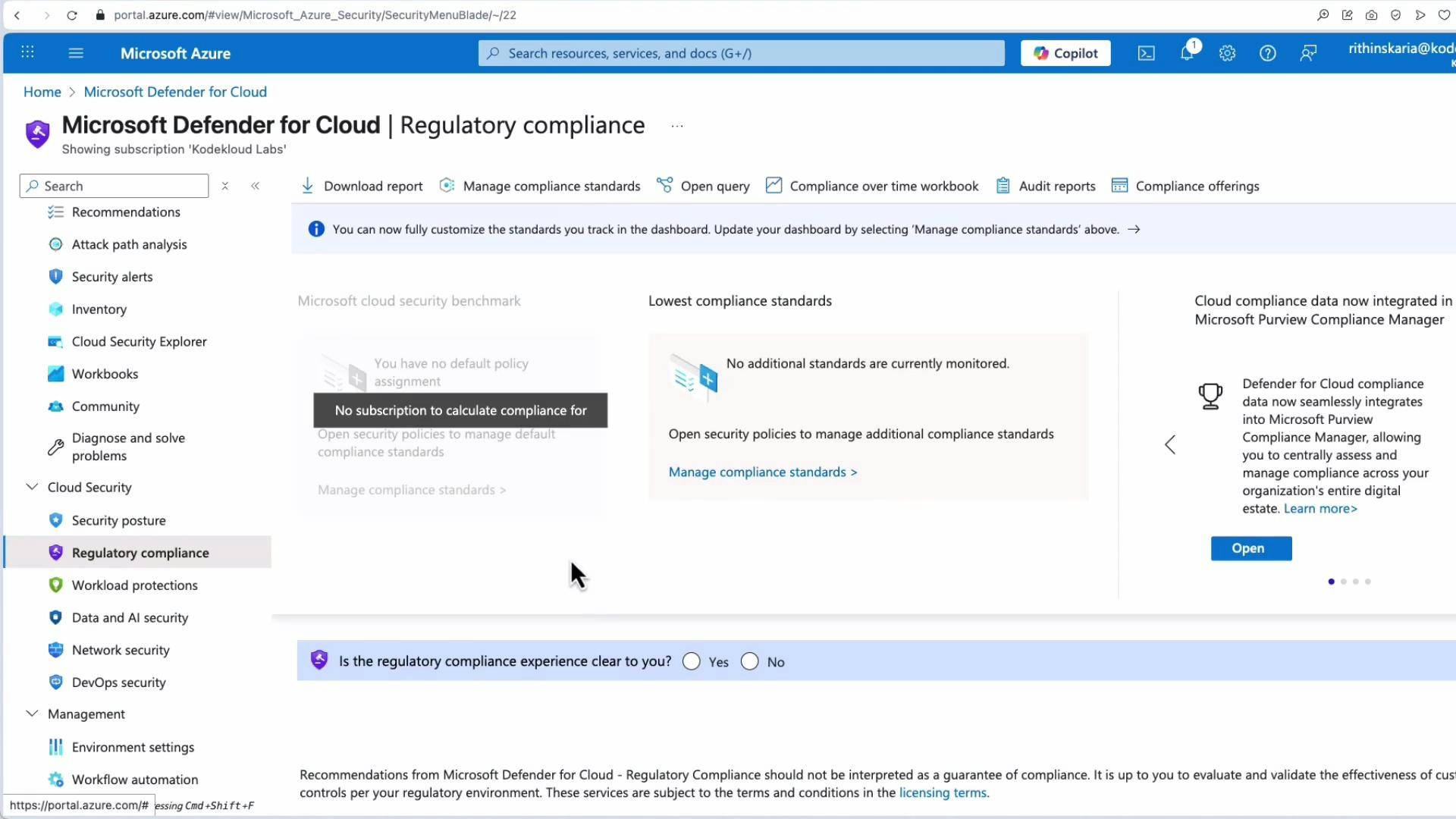
Compliance dashboard and control visibility
At the top level, Defender for Cloud lists the security standards applied to a subscription and shows where those policies are assigned. The dashboard highlights controls (for example, network security) and surfaces how many resources fail each control plus severity to help you prioritize remediation.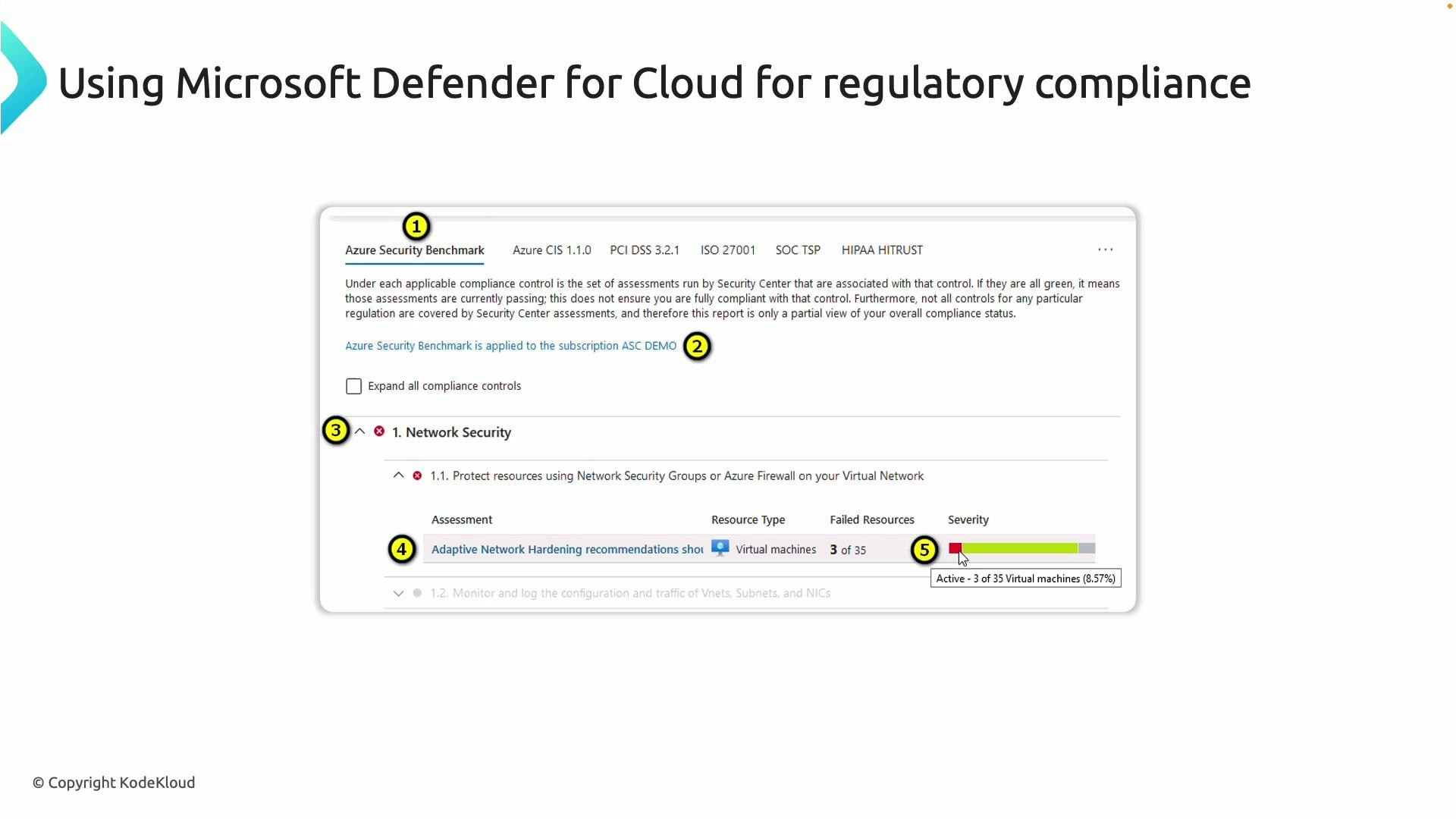
Multi‑framework support, Secure Score, and compliance scoring
Defender for Cloud supports monitoring multiple compliance frameworks at once (ISO/IEC 27001:2013, PCI DSS, HIPAA, Azure Security Benchmark, NIST, CIS, and more). It provides two complementary metrics:- Compliance score — shows how well your environment meets the selected regulatory frameworks.
- Secure Score — reflects overall security posture across recommendations.
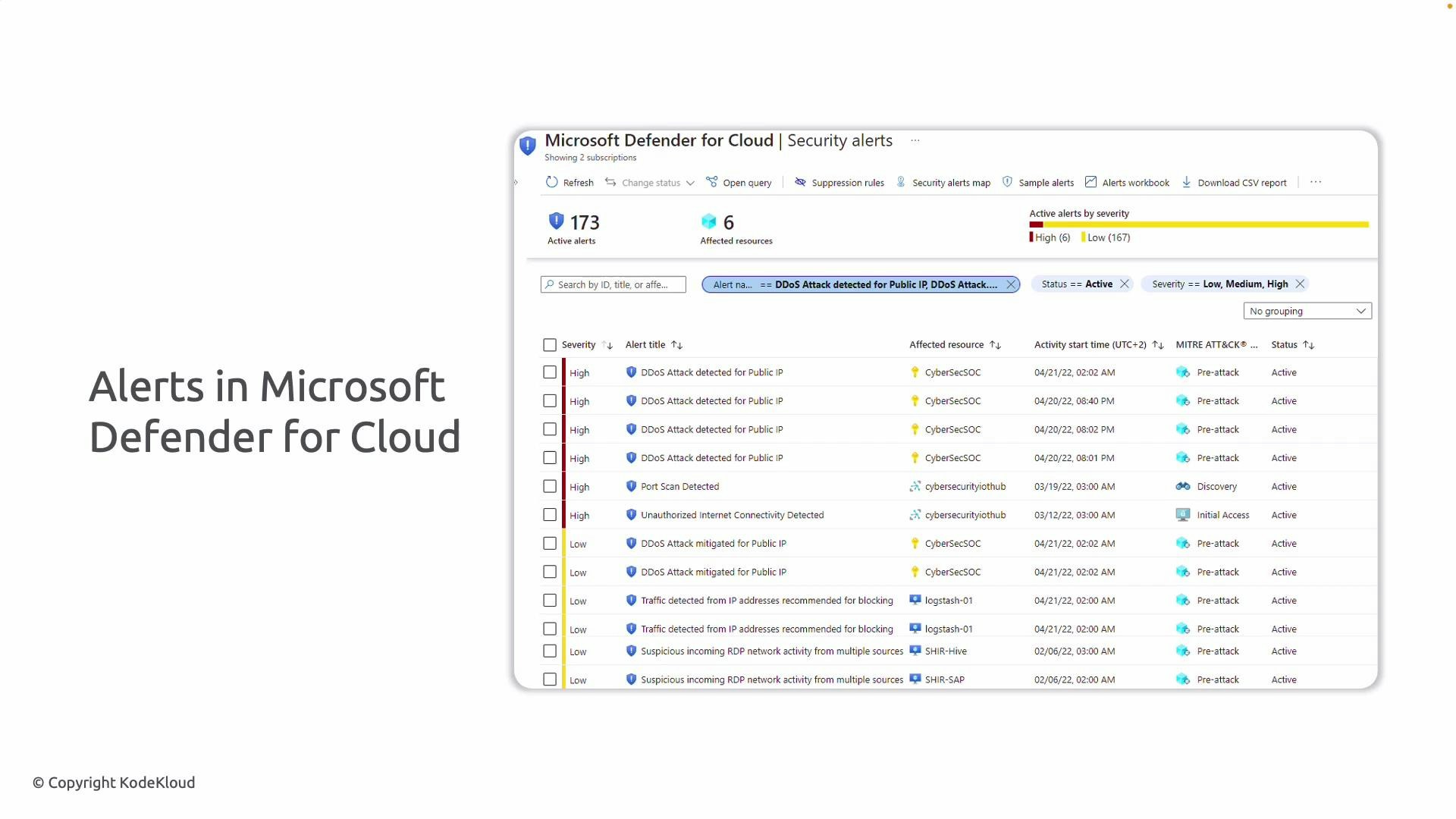
Alerts, investigations, and automation
Defender for Cloud centralizes security alerts (DDoS, suspicious RDP, port scans, anomalous sign‑ins, etc.) and provides:- Severity and affected resources
- Investigation workflows and context
- Direct investigation from the dashboard
- Automation playbooks to remediate or respond to incidents
Where to find these features in the Azure portal
Open Microsoft Defender for Cloud from the Azure portal (search for “Defender for Cloud”). You typically land on the Overview blade. On a newly created subscription you may initially see few recommendations or a message like “No compliance assessment” until the evaluation has run.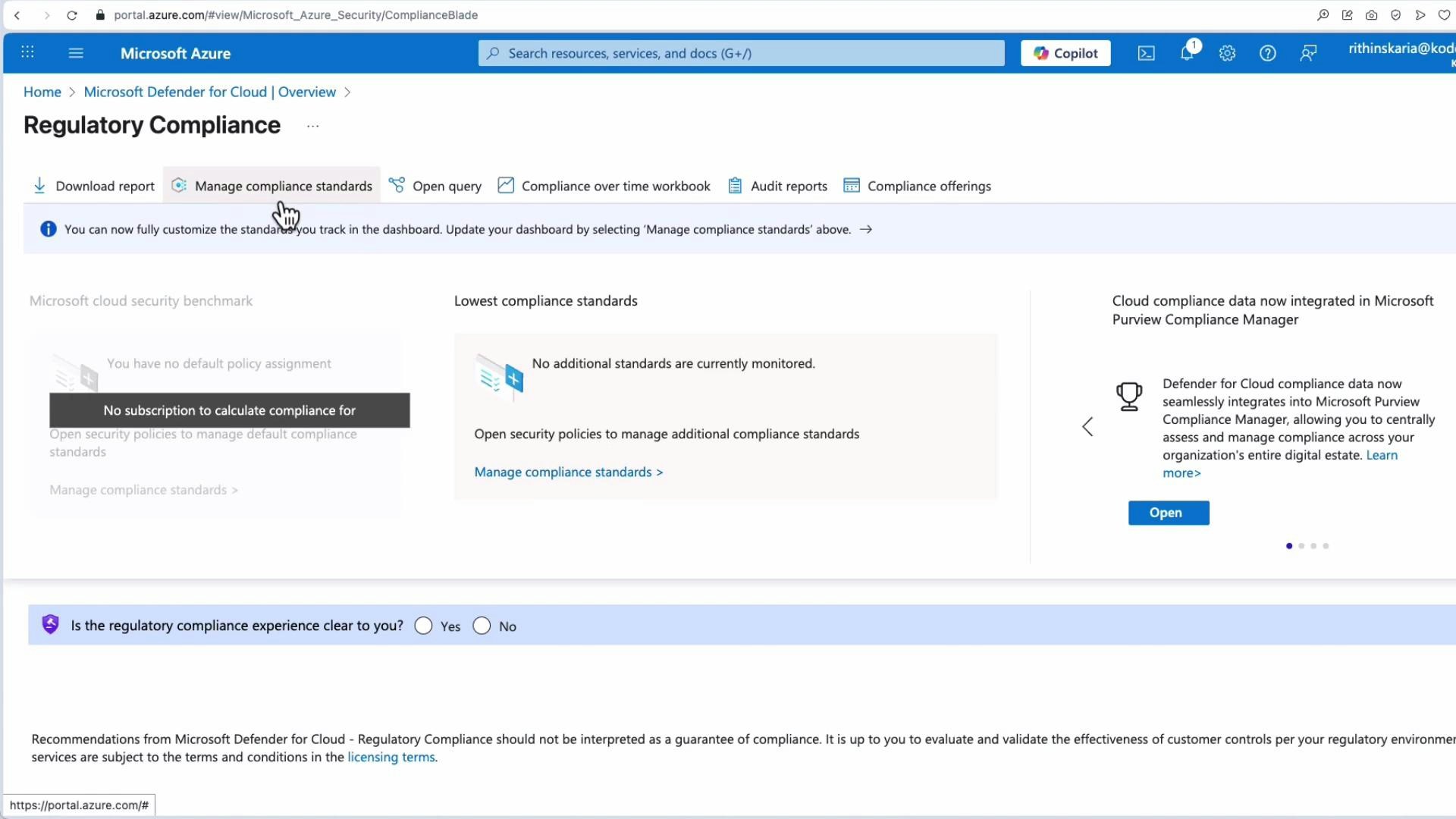
- Click Manage compliance standards from the Regulatory compliance dashboard.
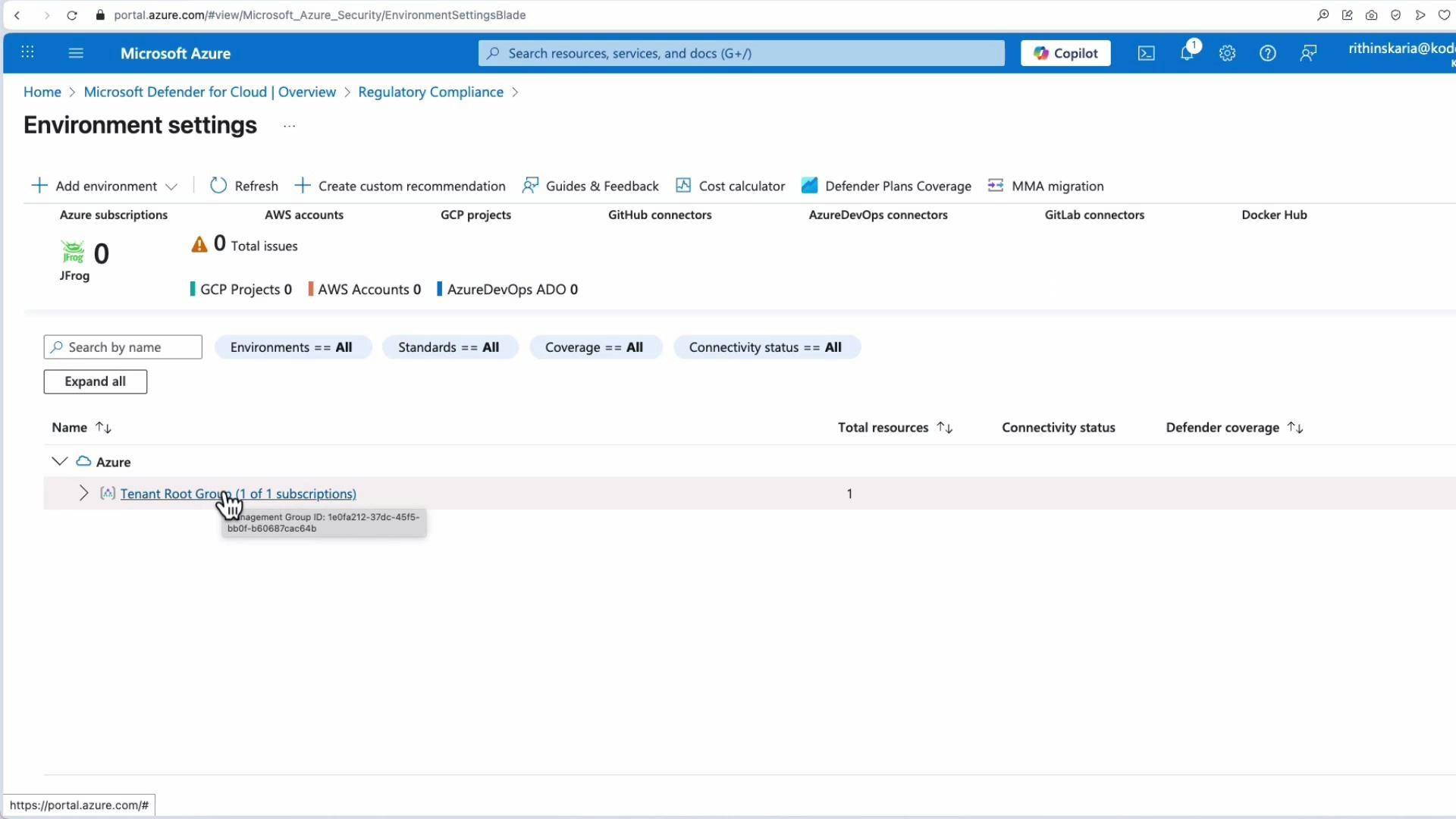
- In Environment settings choose the scope (subscription or management group).
- Select the frameworks you want to monitor and configure any framework-specific parameters (for example, how to audit virtual machines).
When you enable Defender for Cloud or add new policies, it typically takes between 8 to 24 hours (depending on evaluation frequency and number of resources) for recommendations and compliance assessments to fully populate.
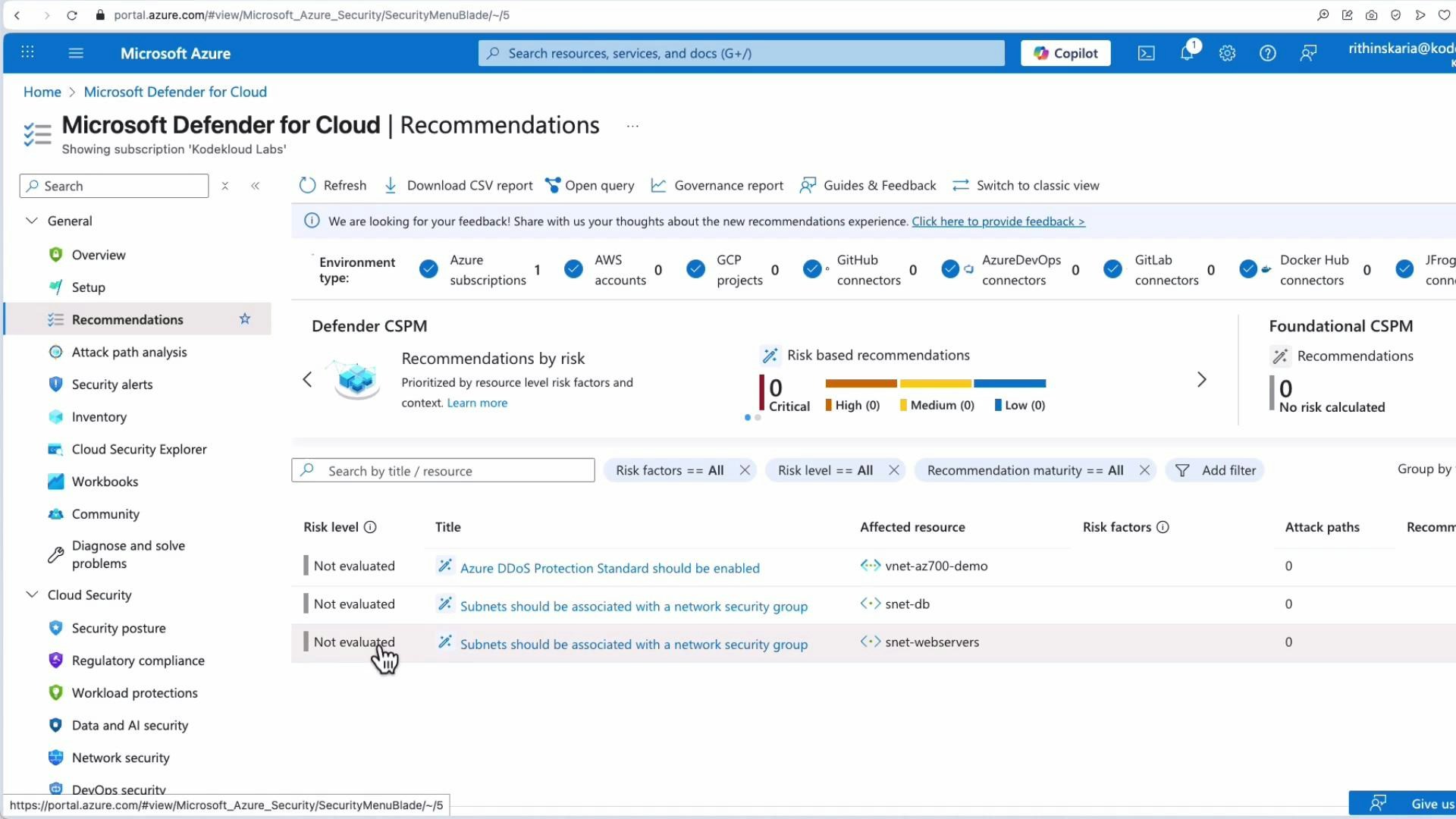
Recommendations and remediations
Open Recommendations in Defender for Cloud to see subscription-specific security recommendations. Early in setup some items may show as “Not evaluated” until assessments complete. Recommendation details include risk summary, governance impact, remediation steps, available automation, and the option to exempt resources where appropriate.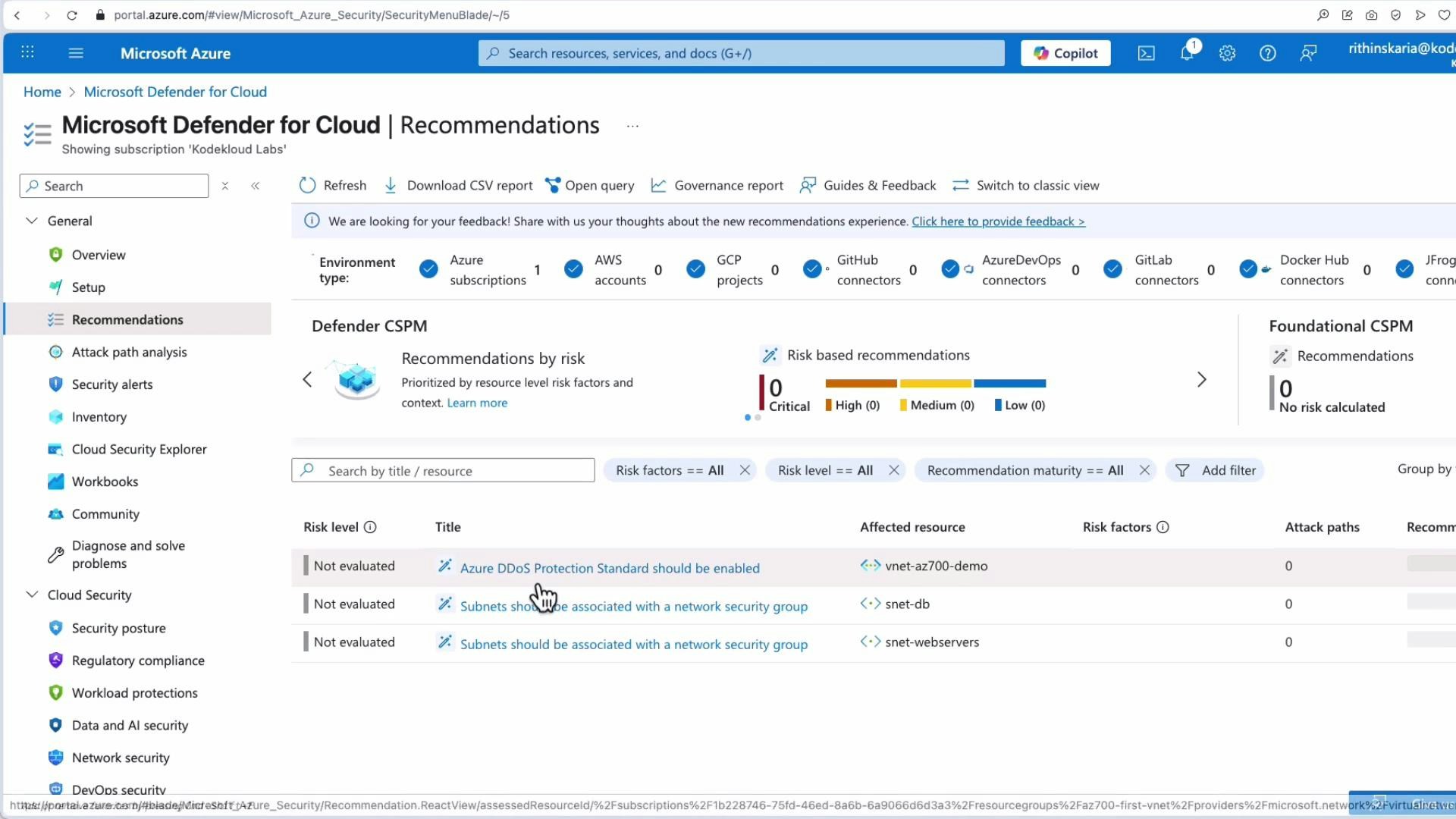
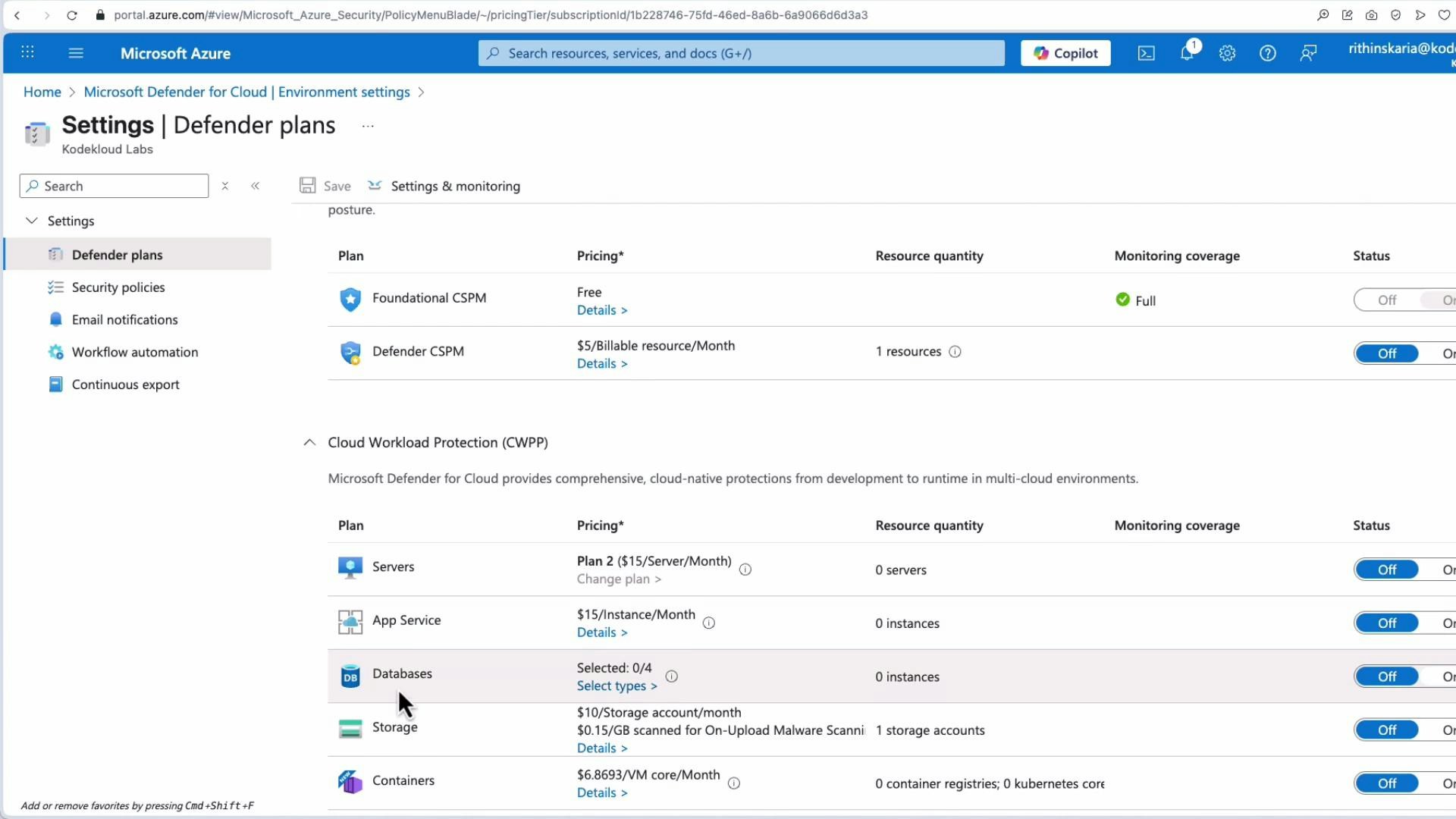
Defender plans and coverage
Defender for Cloud provides additional Defender plans (server protection, App Service, databases, CSPM, CWPP, etc.) for deeper visibility and more recommendations tailored to specific resource types. These plans can be enabled per subscription or workspace.Some Defender plans incur additional charges. Review pricing and choose plans that align with your security and compliance needs before enabling coverage broadly.
Study and practical focus (for exams and real deployments)
From both an exam and operational perspective, focus on these Defender for Cloud capabilities:- Integration of industry standards via built‑in controls
- Continuous assessment and Compliance score / Secure Score
- Actionable recommendations and remediation steps with automation options
- Central alerting, investigation workflows, and playbook integration
- Exportable audit reports for compliance verification
Quick reference table
| Capability | Why it matters | Example |
|---|---|---|
| Built‑in frameworks | Saves time and ensures alignment to standards | Azure Security Benchmark, PCI DSS, ISO/IEC 27001 |
| Continuous assessment | Keeps posture up-to-date and prioritized | Compliance score, Secure Score |
| Recommendations | Actionable fixes and automation | Associate subnets to NSGs, enable DDoS Protection Standard |
| Alerts & automation | Faster response and reduced manual effort | Playbooks to remediate alerts |
| Exportable reports | Evidence for auditors and compliance teams | Downloadable assessment reports |
Links and references
- Microsoft Defender for Cloud documentation: https://learn.microsoft.com/azure/defender-for-cloud/
- Azure Security Benchmark: https://learn.microsoft.com/security/benchmark/azure/
- Microsoft Purview Compliance Manager: https://learn.microsoft.com/microsoft-365/compliance/compliance-manager-overview