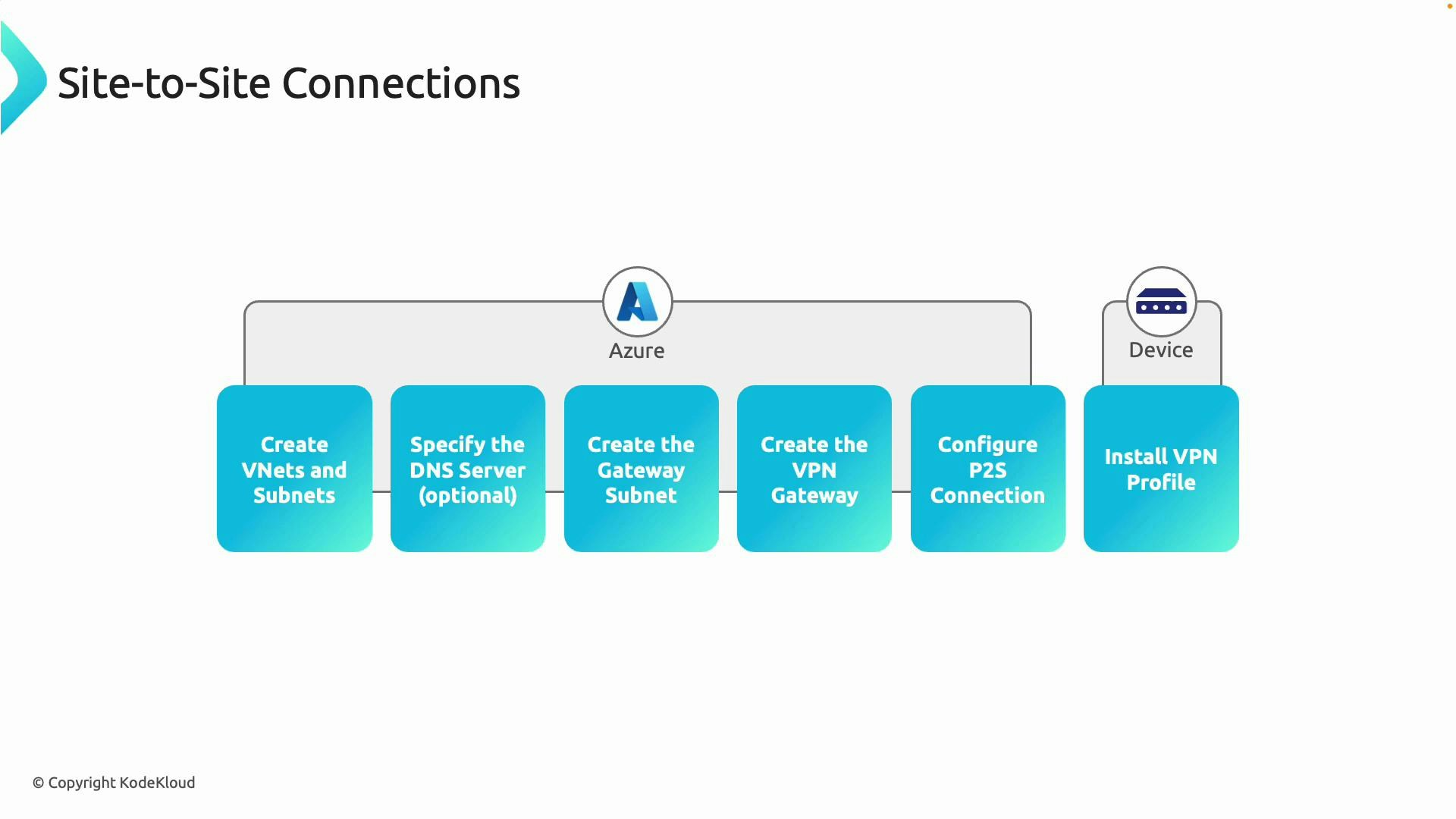
- Create or reuse VNets and subnets.
- (Optional) Specify custom DNS servers.
- Create the gateway subnet and VPN Gateway (or reuse an existing VPN Gateway).
- Configure the Point-to-Site settings on the VPN Gateway.
- Download and install the VPN profile on client devices.
You can reuse an existing VPN Gateway for Point-to-Site connections. Confirm that the gateway SKU supports P2S and the tunnel types/authentication methods you require before enabling P2S.
Configure Point-to-Site in the Azure portal
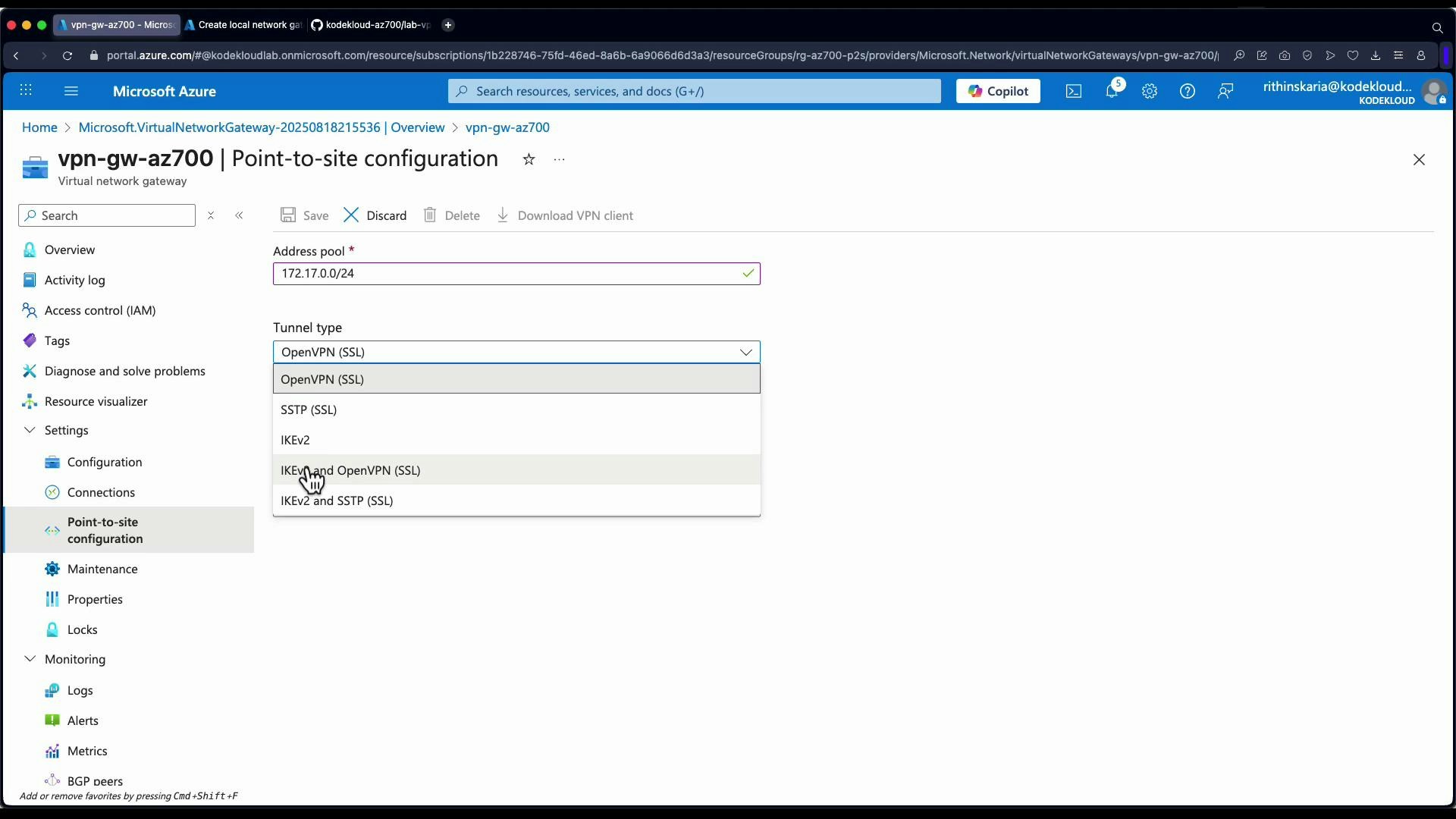
- Open the VPN Gateway resource in the Azure portal.
- Select the “Point-to-site configuration” blade.
- Configure these key fields:
- Address pool: the IP range assigned to P2S clients (e.g., 172.17.0.0/24). Ensure the pool is large enough for concurrent clients.
- Tunnel type: OpenVPN, SSTP, IKEv2, or a combination. OpenVPN is commonly used for cross-platform compatibility.
- Authentication type: Certificate, Azure Active Directory (Microsoft Entra ID), or RADIUS.
| Configuration Item | Purpose | Recommendation |
|---|---|---|
| Address pool | IPs assigned to clients | Use a dedicated, non-overlapping CIDR (e.g., 172.17.0.0/24) |
| Tunnel type | VPN transport protocol(s) | Use OpenVPN for broad client support; add IKEv2/SSTP if required |
| Authentication | How clients authenticate | Use Azure AD for centralized identity or certificate auth for simpler setups |
| Gateway SKU | Feature support and throughput | Ensure the SKU supports P2S, required tunnels, and concurrent connections |
- Tenant ID — your Azure AD tenant GUID.
- Audience — the application/audience value used by OpenVPN configuration.
- Issuer — the issuer URL (varies by cloud). Azure includes guidance and links in the portal for authorizing the Microsoft VPN client application in your tenant. You must usually authorize the client application before Azure AD authentication will work.
When using Microsoft Entra ID authentication, ensure the VPN client application is authorized in your tenant and that the Audience/Issuer values match the registered app. Misconfigured values will prevent clients from obtaining tokens.
Download and import the VPN client profile
After saving the P2S configuration, Azure generates a VPN client package (ZIP) for supported platforms. Steps to get the client connected:- In the VPN Gateway blade, click “Download VPN client” and save the ZIP file.
- Unzip the package and locate the platform-specific XML/profile files.
- Open the Azure VPN Client application:
- Click Add -> Import.
- Select the XML profile from the unzipped folder.
- The Azure VPN Client imports the profile and creates a connection entry.
Hub-spoke scenario and gateway transit
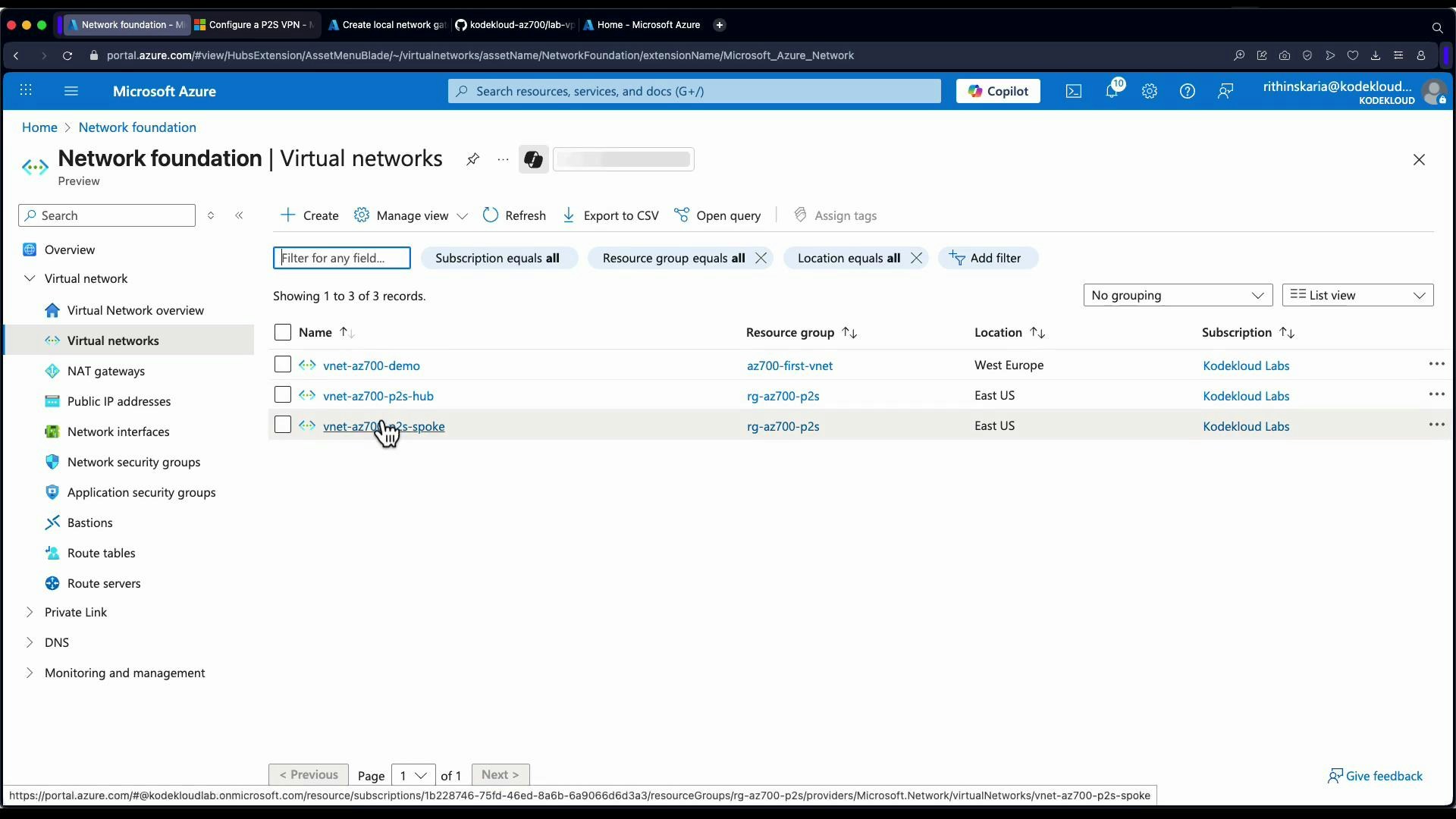
If your VPN Gateway is in a hub VNet and you want P2S clients to access spoke VNets, enable gateway transit through VNet peering.- Open the Virtual Networks blade and identify the hub and spoke VNets.
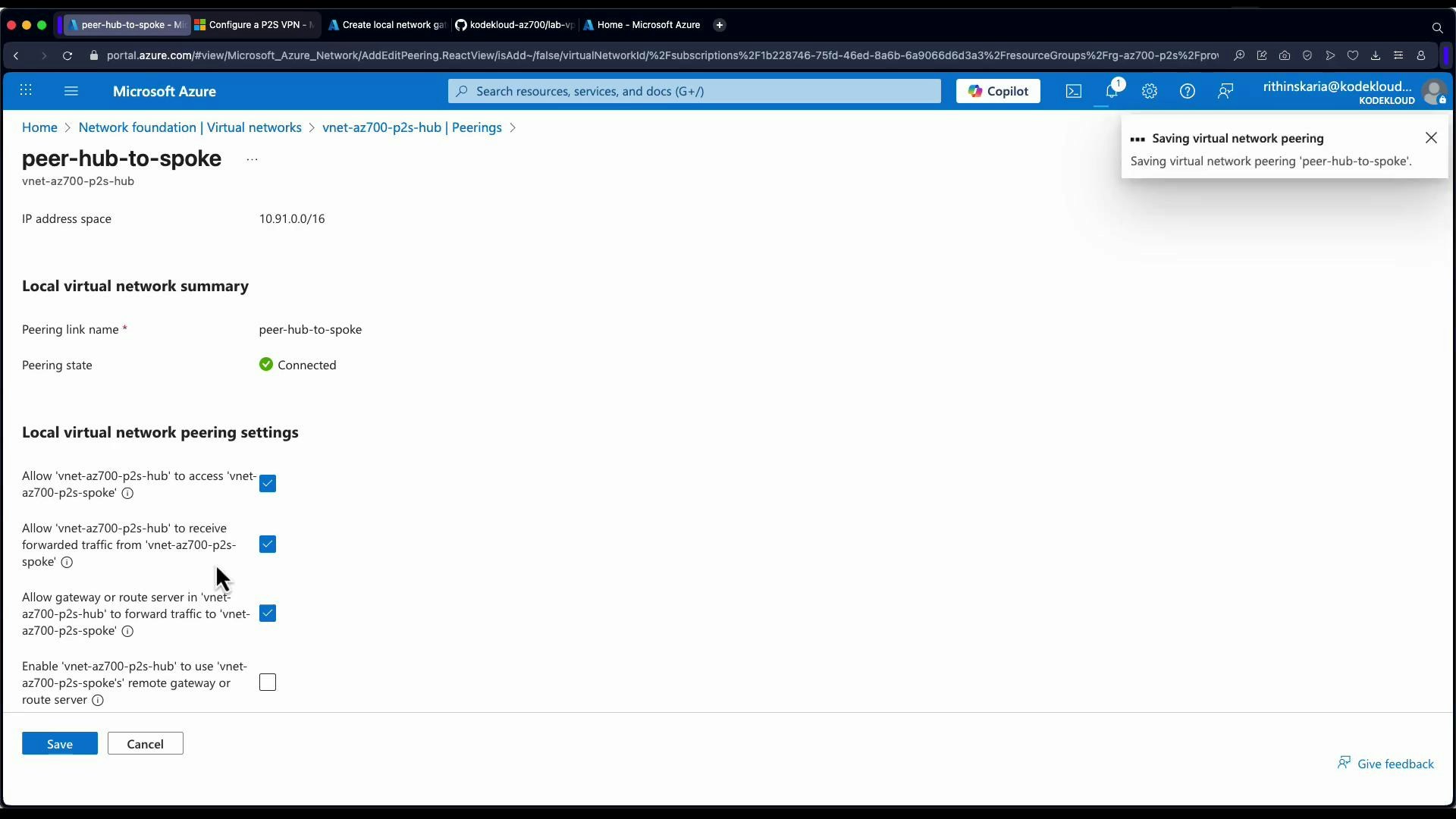
- Edit the hub-to-spoke peering:
- Enable “Allow gateway or route server to be used in the remote virtual network” (portal text may show Allow gateway transit / Use remote gateways).
- Edit the spoke-to-hub peering:
- Enable “Use remote gateway” (so the spoke uses the hub’s VPN gateway).
Verify access to internal resources
With the VPN connected and peering/gateway transit configured:- Test connectivity to internal private IPs (VMs or services without public IPs).
- Verify network security group (NSG) rules allow the necessary inbound traffic from the P2S address pool or hub subnets.
- Confirm effective routes on target VMs or network interfaces if needed.
| Check | Why |
|---|---|
| VPN client IP | Ensure client received an IP from the P2S address pool |
| VPN routes | Ensure routes to the hub and spokes are present in the client |
| VNet peering | Hub peering should allow gateway transit; spoke peering should use remote gateway |
| NSGs / Firewall | Confirm rules permit traffic from P2S CIDR to the target resources |
| Gateway SKU & limits | Ensure SKU supports required tunnels and client count |
References and next steps
- Azure Point-to-Site VPN overview
- Virtual network peerings and gateway transit
- Azure VPN Client download and instructions