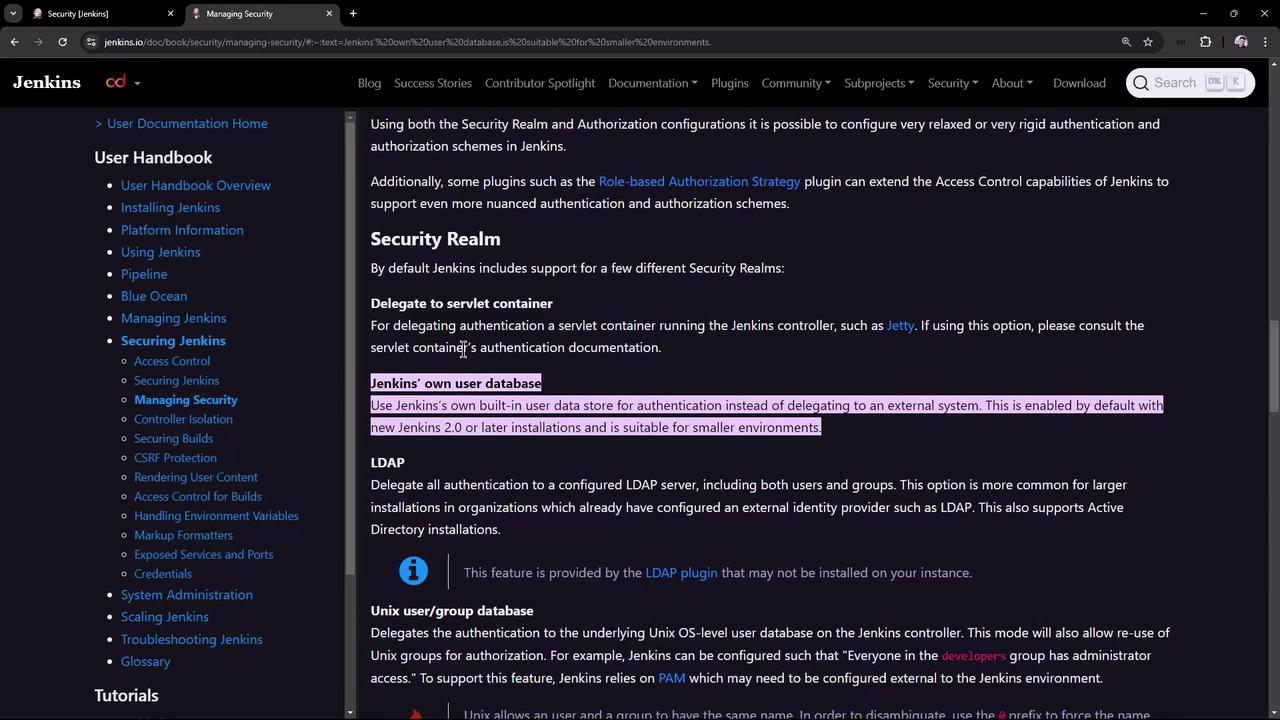
In this guide, we’ll dive into configuring authentication and authorization in Jenkins. By default, Jenkins creates a single admin user and doesn’t allow team members to self-register. You can integrate with external identity systems (LDAP or Active Directory) or use the built-in database. Follow these steps to secure your Jenkins instance.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
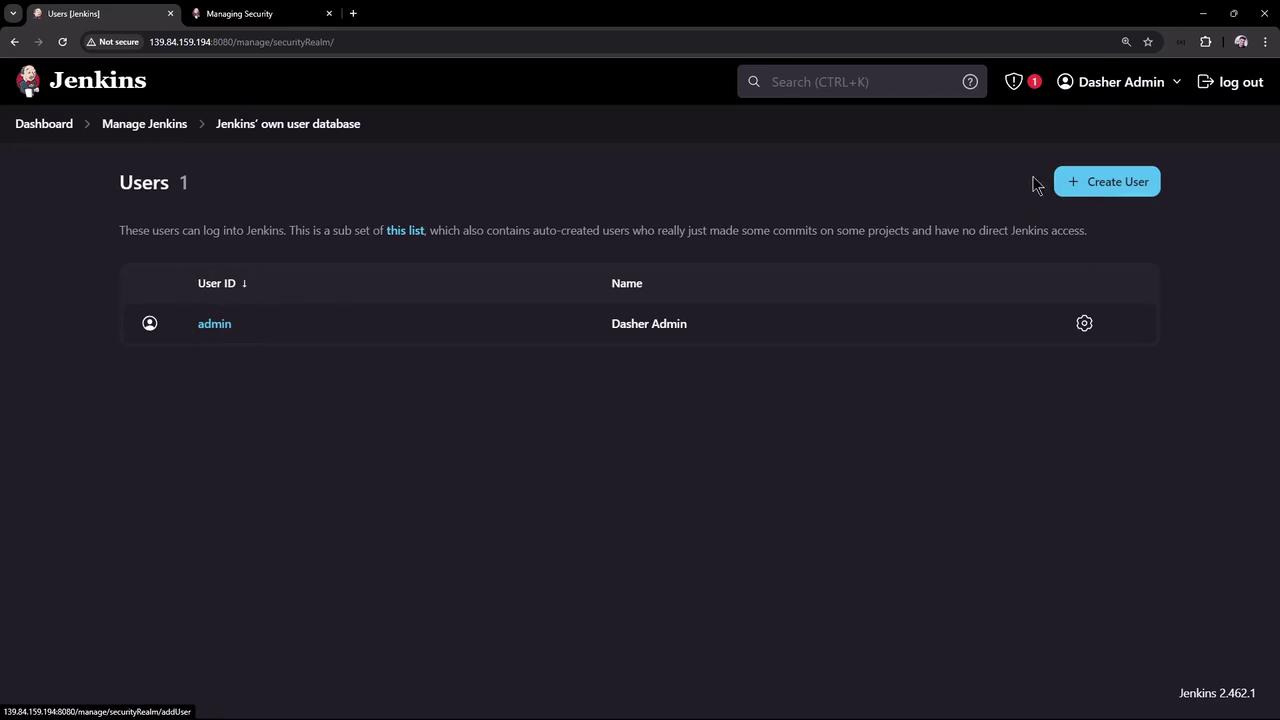
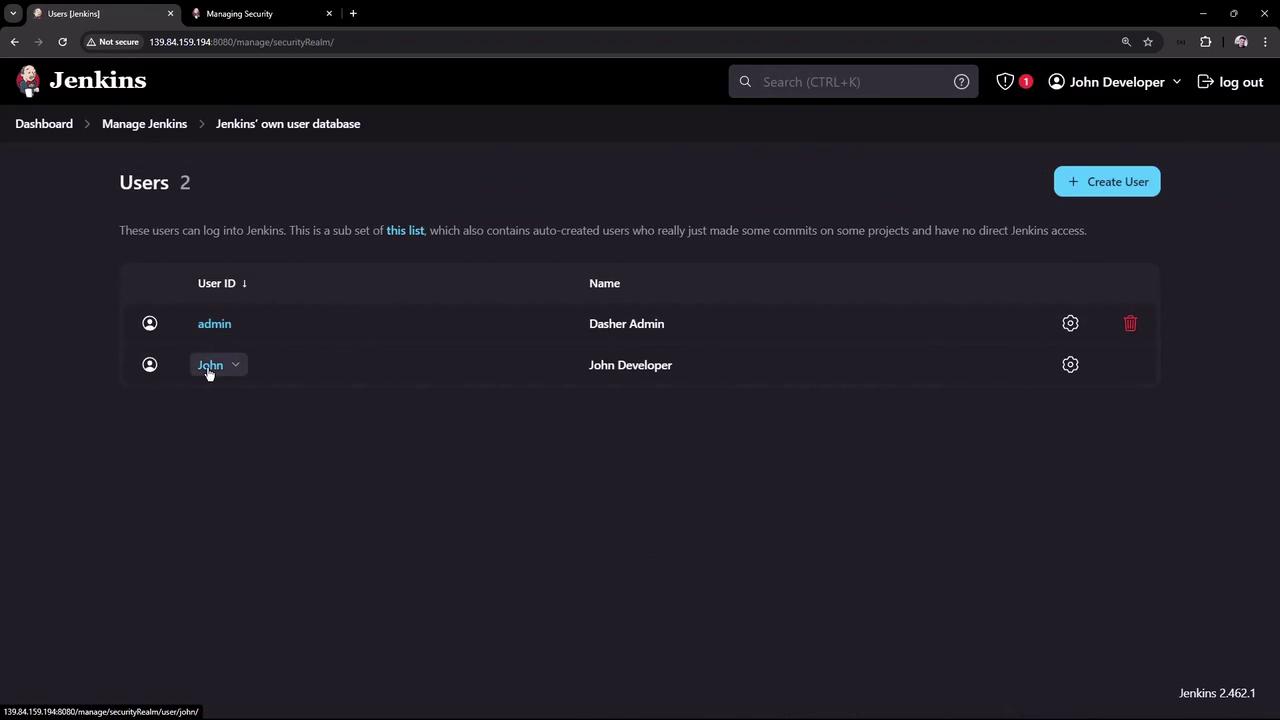
1. Built-in User Database
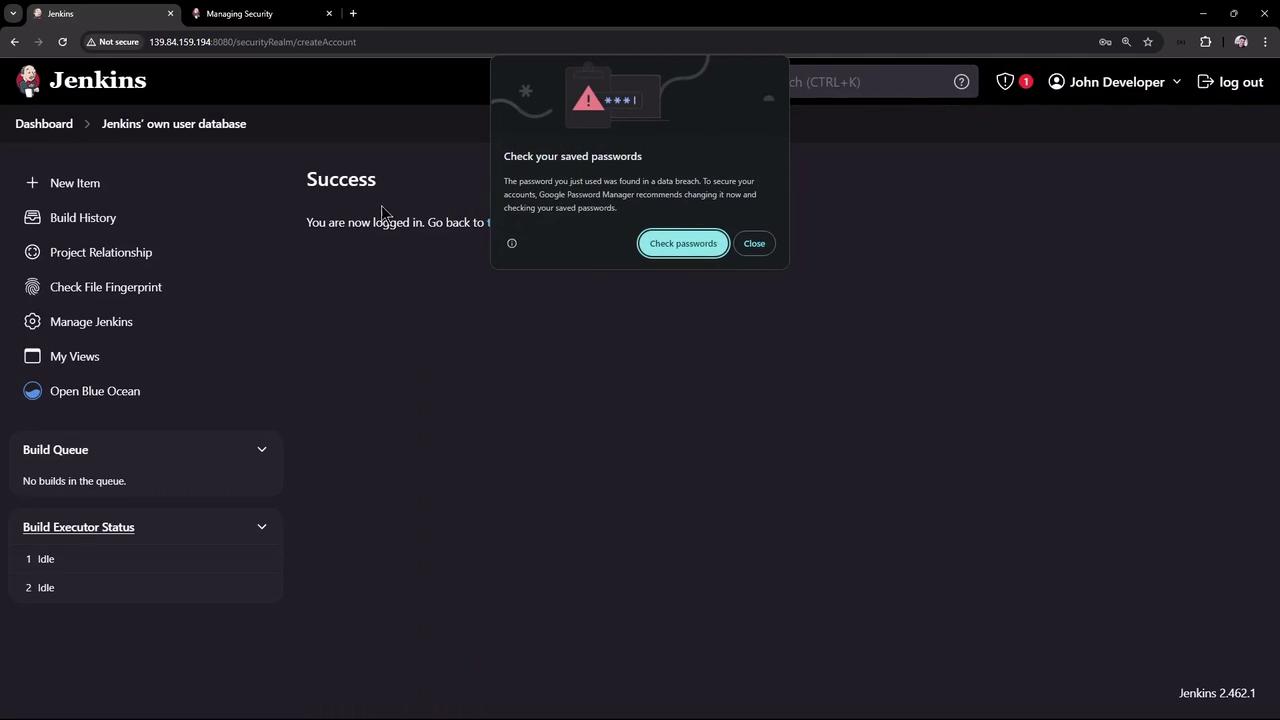
- Log in as the initial admin user.
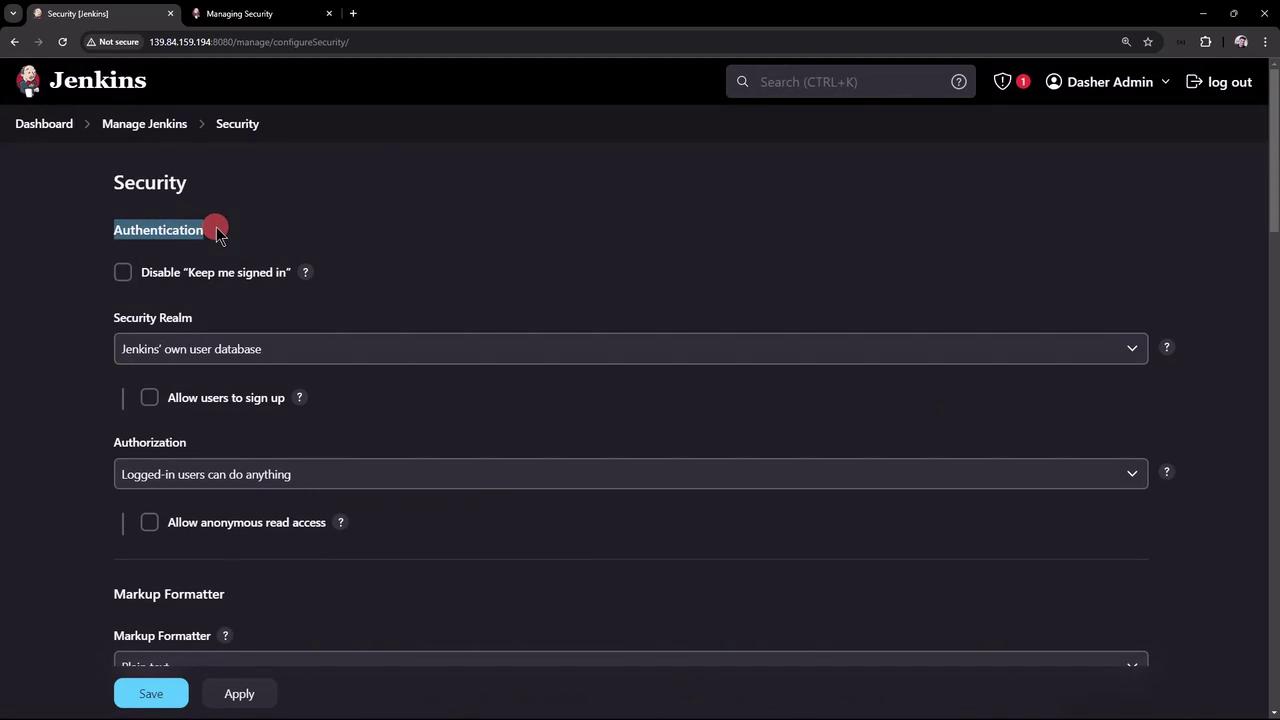
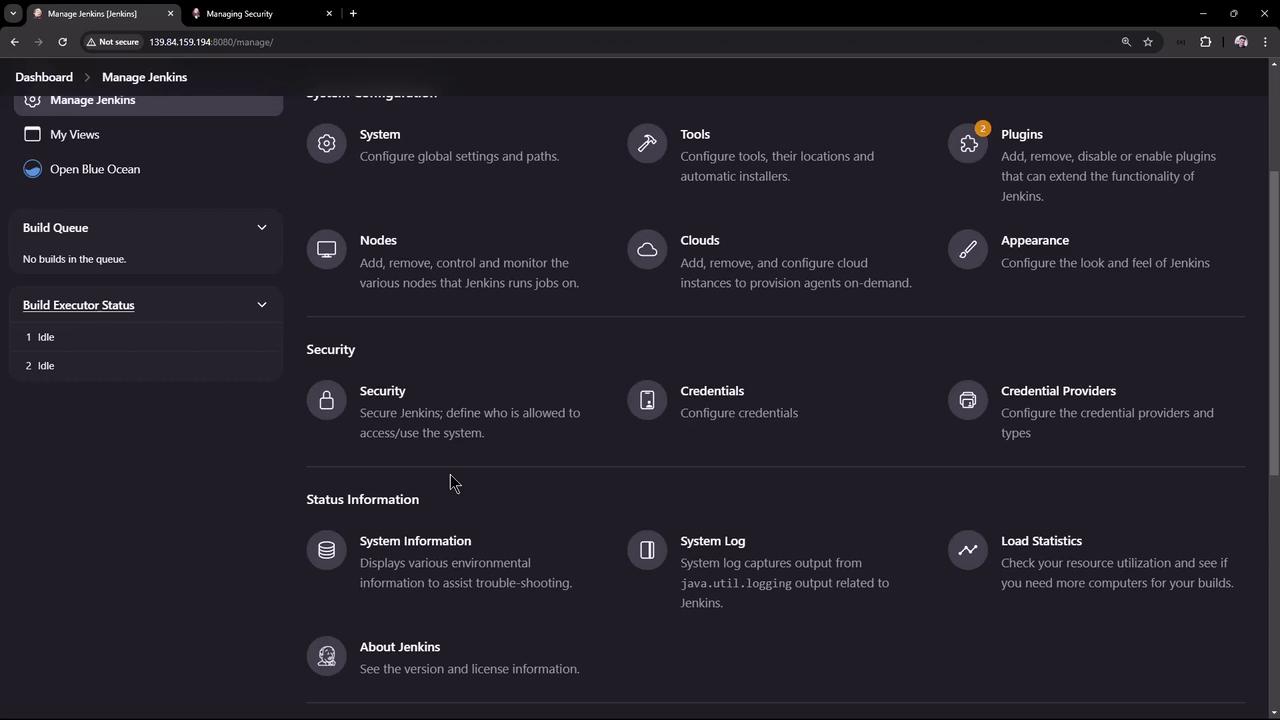
- Navigate to Manage Jenkins → Configure Global Security.
- Under Security Realm, you’ll see the default option:
Enabling Self-Registration
- Under Configure Global Security, disable Keep me signed in.
- Enable Allow users to sign up and click Apply.
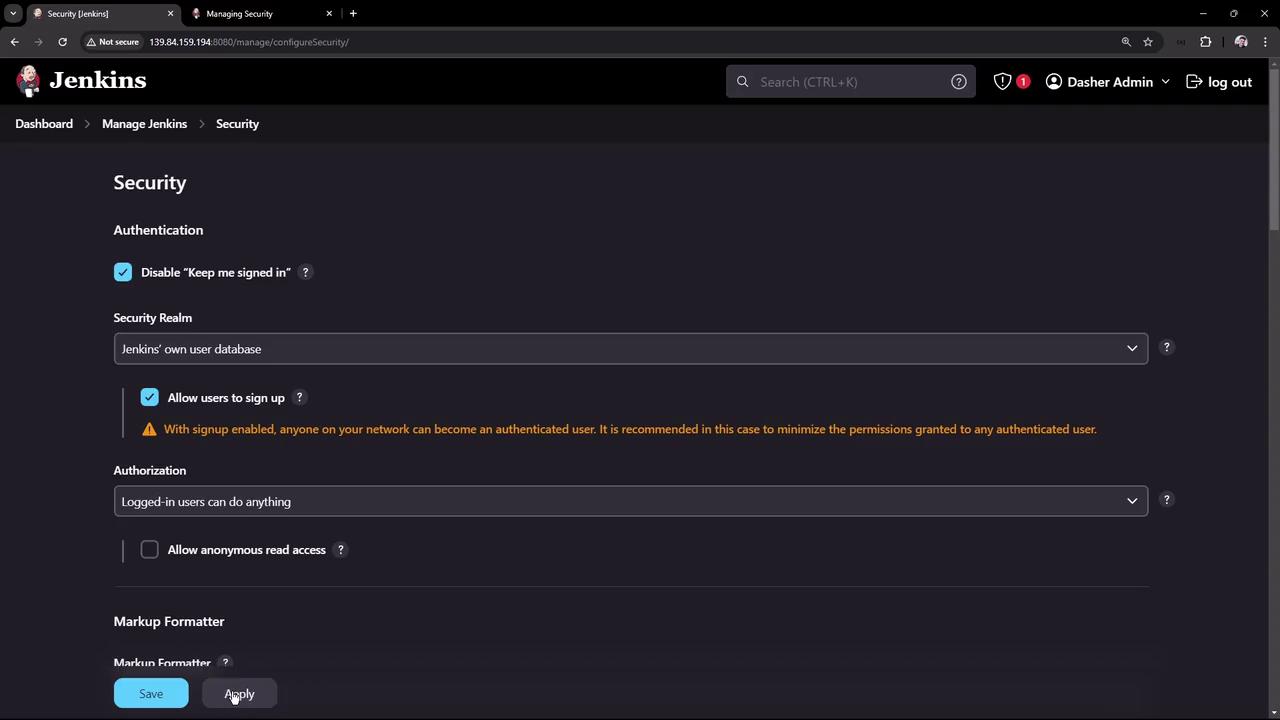
Allowing public sign-up can lead to unwanted accounts. Review registrations regularly or integrate with an external directory for tighter control.
2. Authorization Strategies
Authorization controls who can view, build, or configure jobs. In Configure Global Security, scroll to Authorization. The default is Logged-in users can do anything—only authenticated users have full access. Another setting is Anyone can do anything:| Authorization Strategy | Description |
|---|---|
| Logged-in users can do anything | Only authenticated users have full access. |
| Anyone can do anything | Public access to all actions without login. |
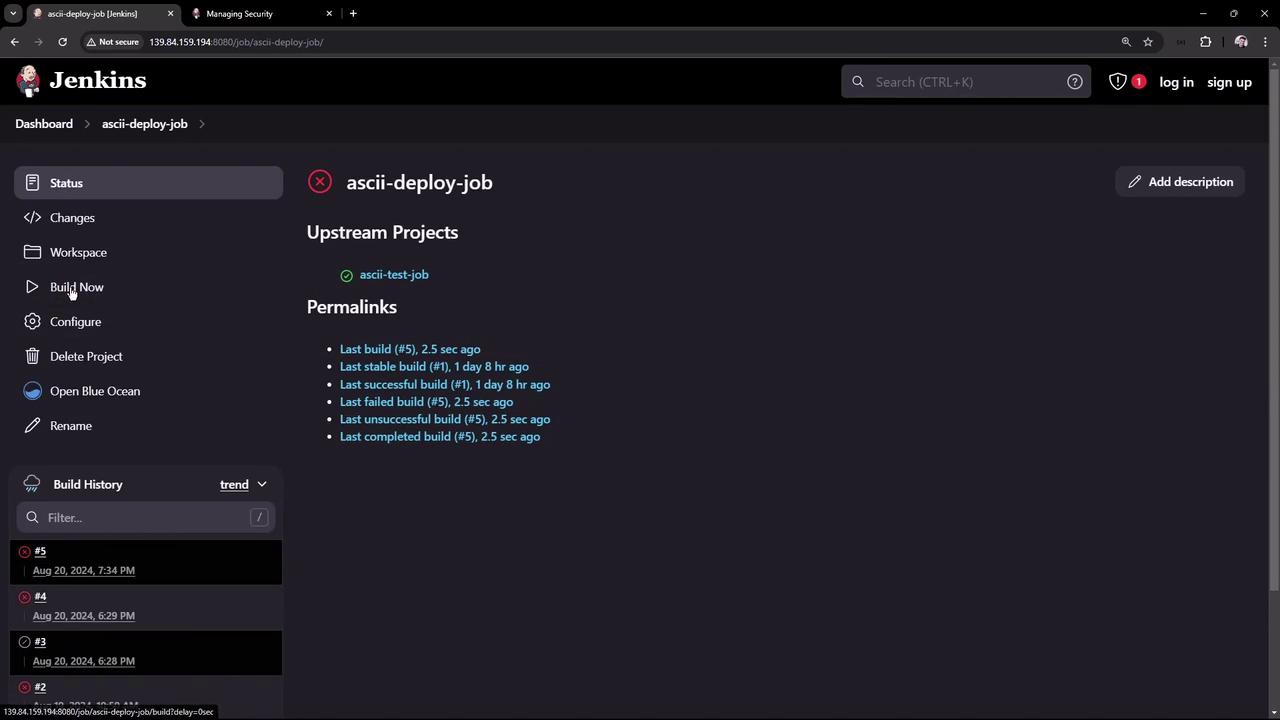
Allowing anonymous users to trigger builds is a serious security risk. Unauthenticated users should never run jobs on a production Jenkins master.
3. Mock Security Realm (Simulating LDAP)
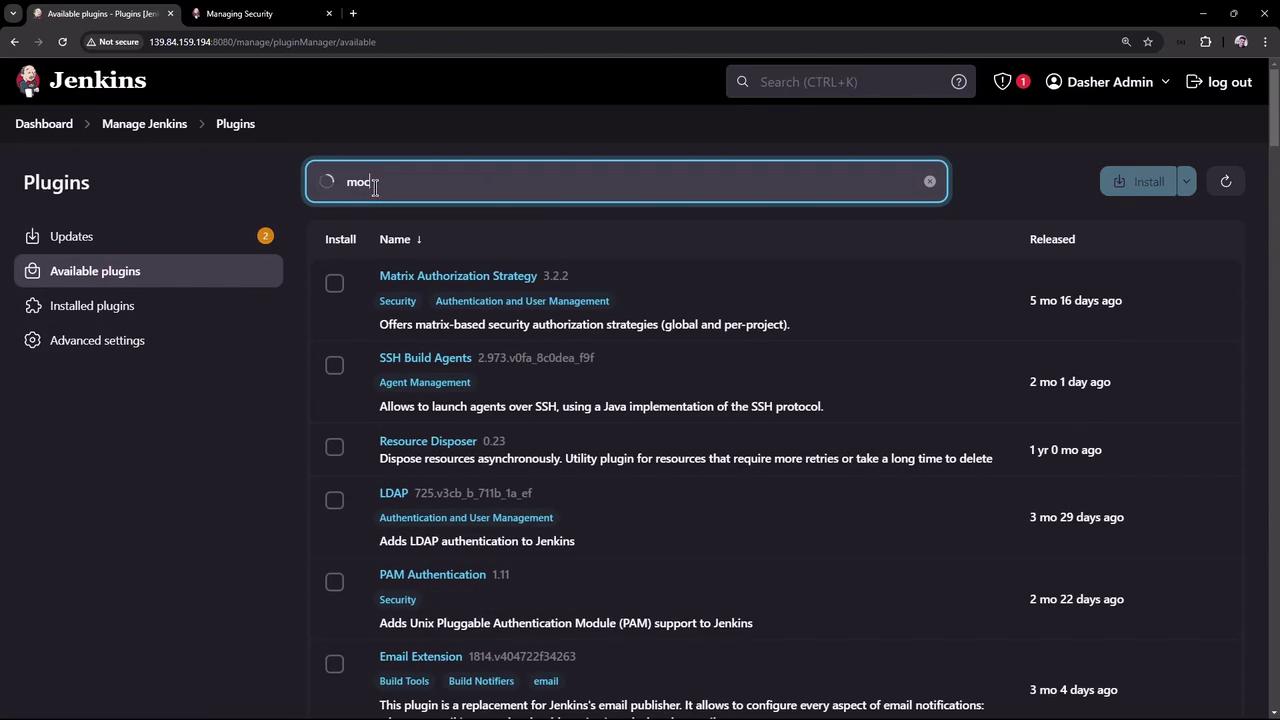
To simulate external authentication without a real directory server, install the Mock Security Realm plugin:- Go to Manage Jenkins → Manage Plugins → Available.
- Search for mock-security-realm and install.
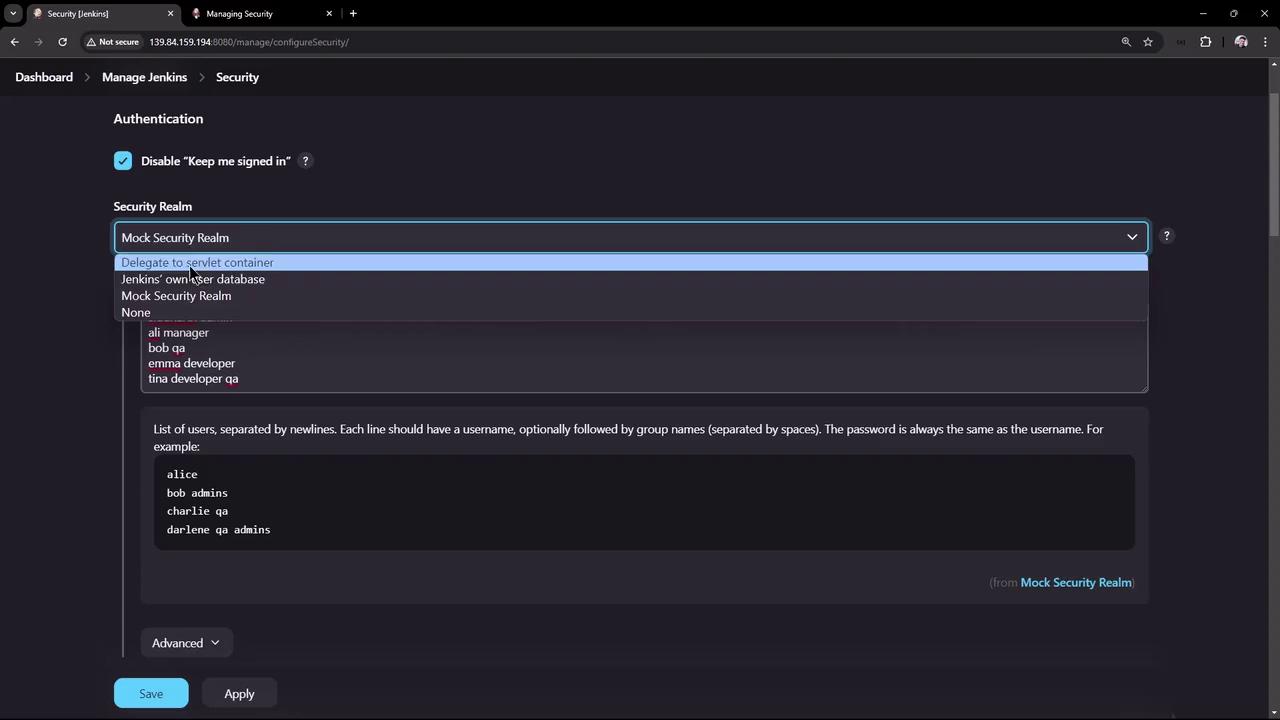
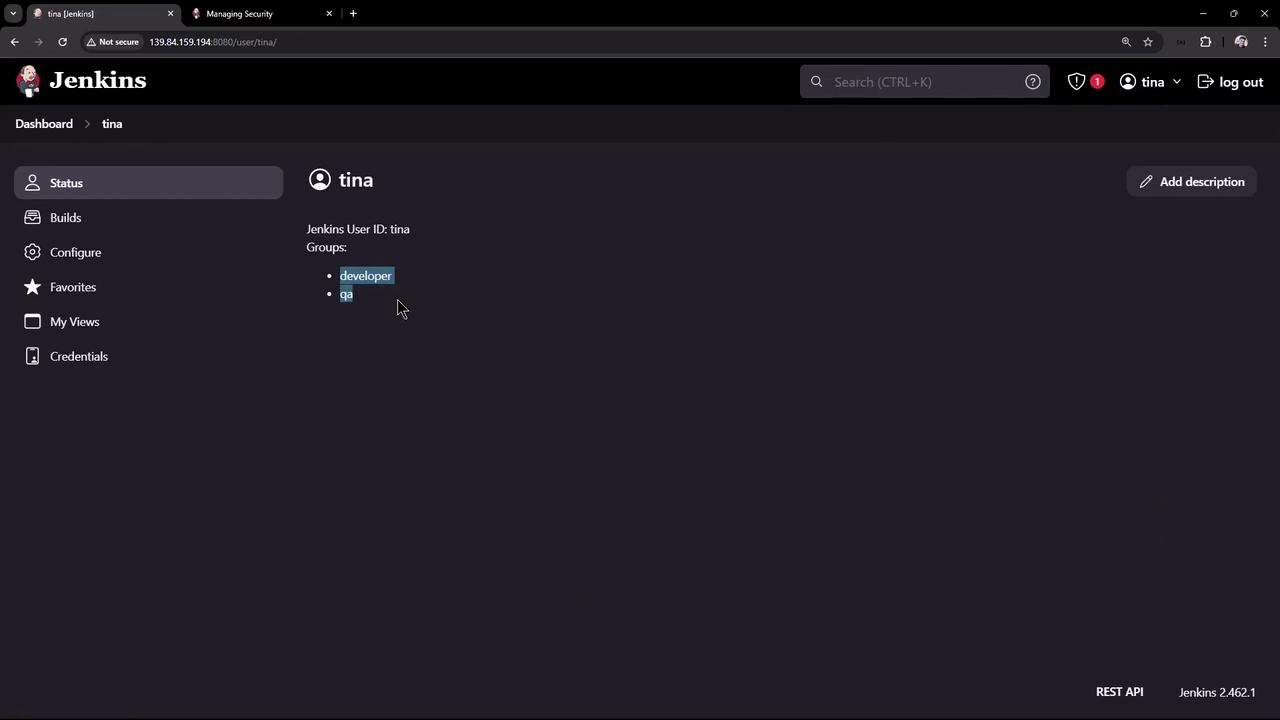
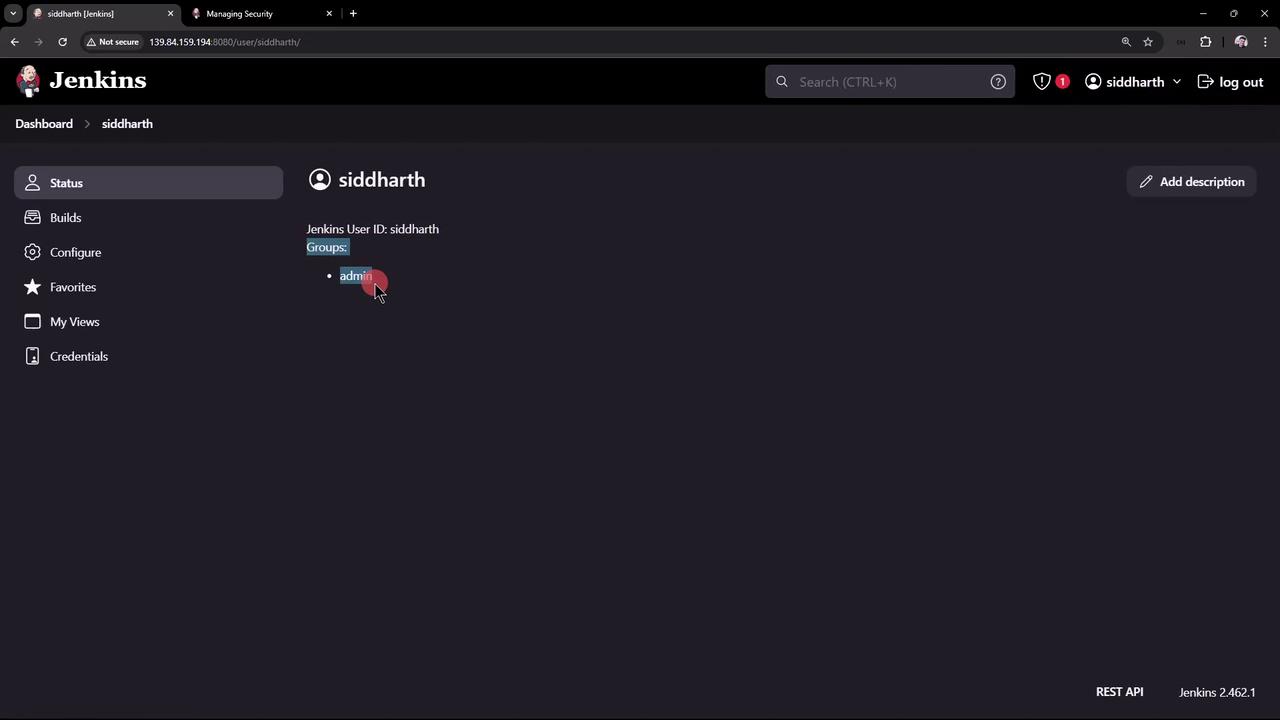
Logging In with Mock Users
Log out, then log in as one of the mock users:- siddharth (password:
siddharth)
- tina (password:
tina)