In this walkthrough, we’ll adapt our Dynamic Application Security Testing (DAST) with OWASP ZAP to ignore a specific warning—“Unexpected Content-Type”—so that the Jenkins build can proceed uninterrupted.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
1. Identify the Unexpected-Content-Type Warning
Run the standard ZAP API scan:2. Generate and Customize the ZAP Rule Configuration
ZAP supports three levels for each rule:| Level | Behavior |
|---|---|
| FAIL | Treat as error and exit non-zero |
| WARN | Report warning but continue (default) |
| IGNORE | Skip reporting the rule entirely |
-
Generate the default config:
-
Open
zap_default.conf—you’ll see lines like: -
Modify or add the entry for rule 100001 with single tabs:
-
Save this as
zap_ignore_rules.
Be sure to use single tab separators. Mixing spaces or multiple tabs will cause parsing errors.
3. Update Your Jenkins Pipeline
In yourJenkinsfile, add the -c zap_ignore_rules flag to the DAST stage:
4. (Optional) Front-End Cosmetic Change for Demo
Add extra rockets inindex.html to visualize a change in your application:
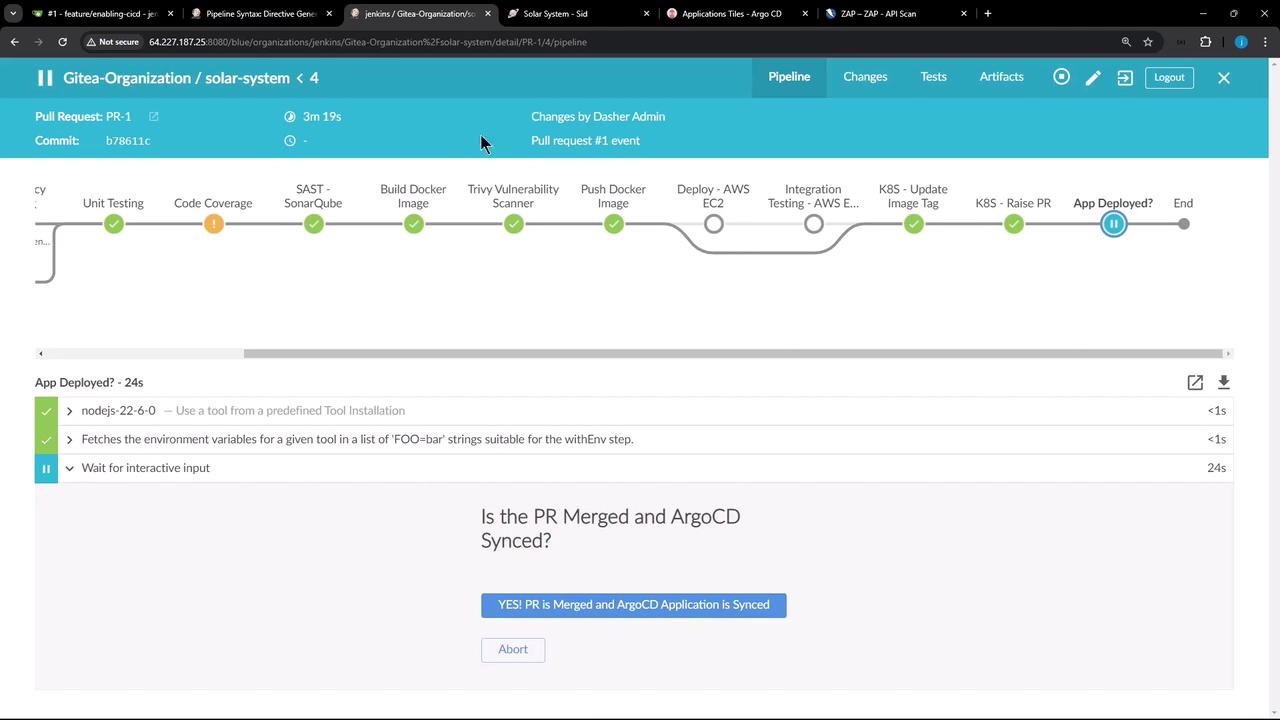
5. Commit, Merge, and Sync with Argo CD
- Commit your changes and open a Pull Request.
- After merge, confirm in Jenkins:
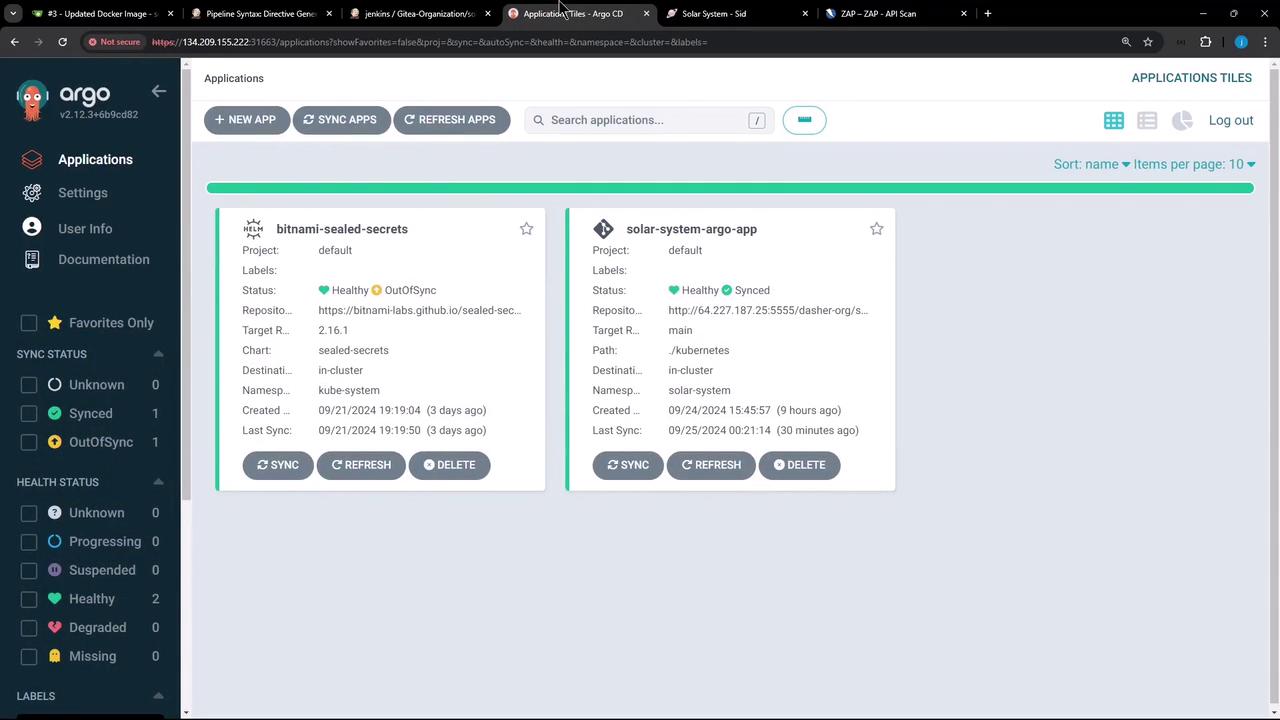
- In Argo CD, sync the
solar-systemapplication:
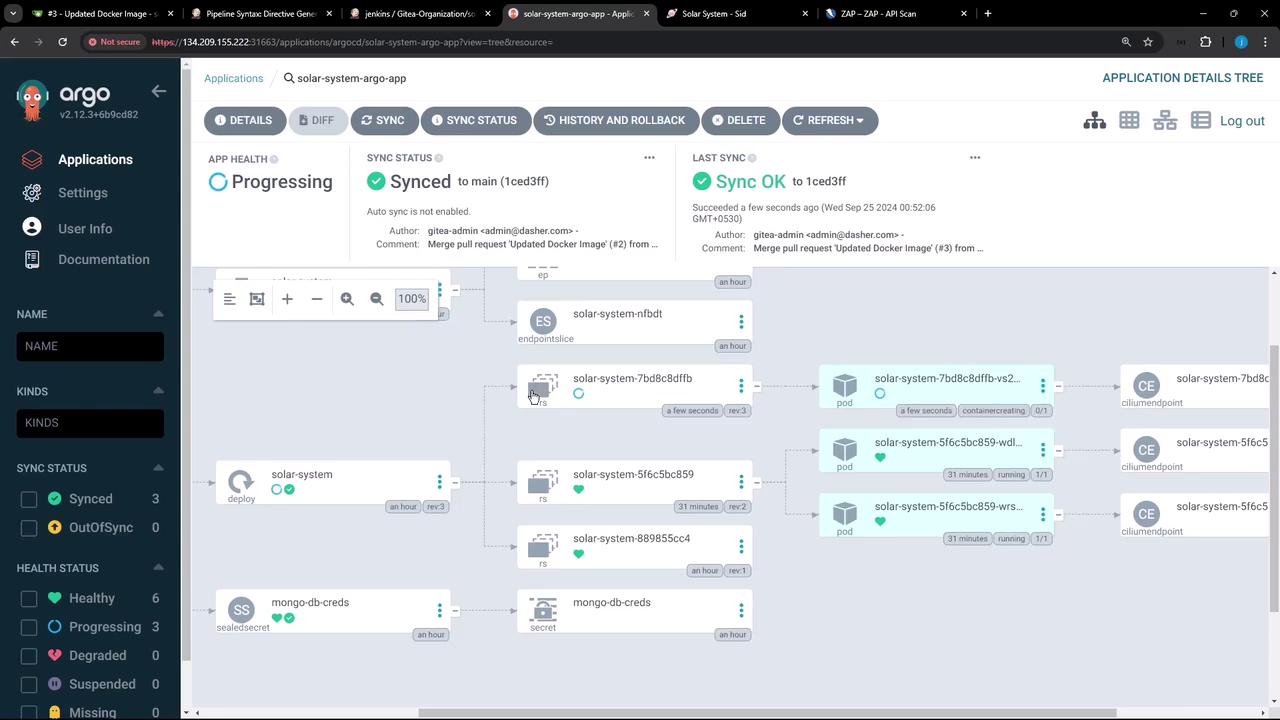
- Once synced, inspect the updated replica set and pods:
6. Troubleshoot Token-Parsing Errors
If you see:zap_ignore_rules likely has spaces instead of tabs.
Open the file in an editor and ensure exactly one
<TAB> between each field:7. Verify Final DAST Results
A successful DAST stage shows: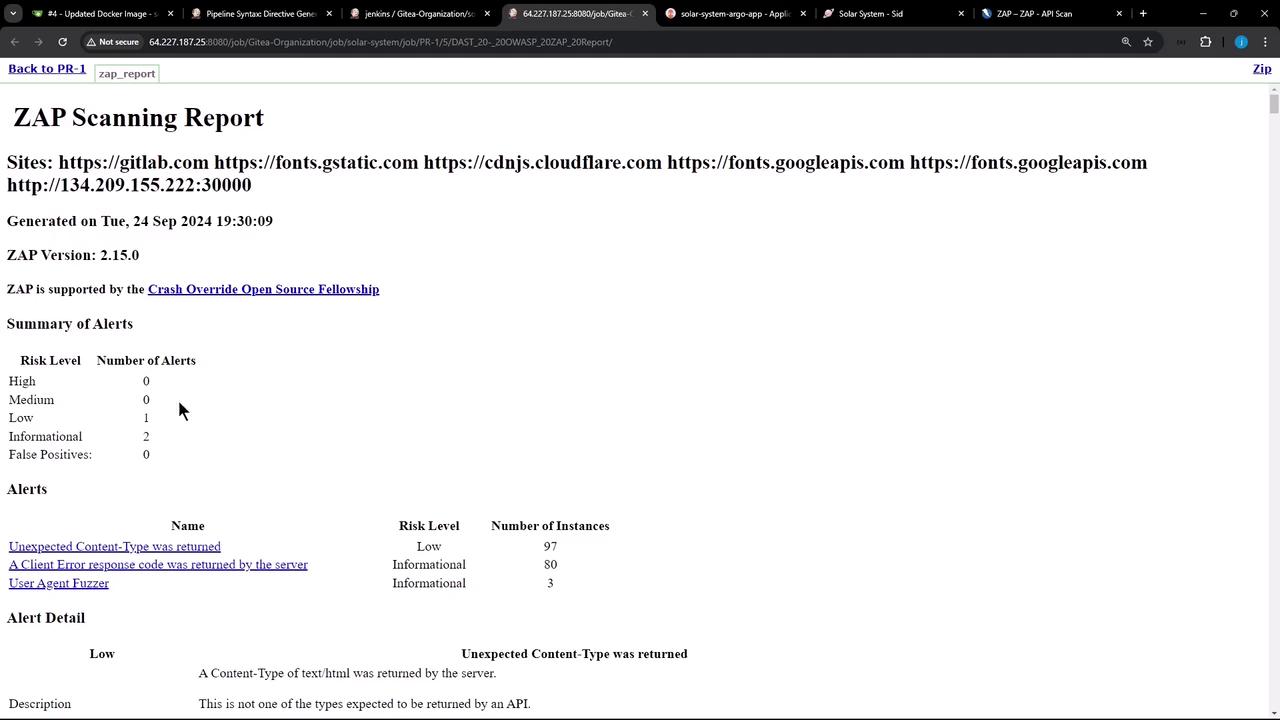
Summary & Next Steps
In this lesson, we:- Ran OWASP ZAP DAST against our API
- Generated and customized an ignore-rules file
- Updated our Jenkins pipeline to use
-c zap_ignore_rules - Published the HTML report in Jenkins
- Synced changes via Argo CD
- Troubleshot tab-delimited config errors