In this guide, we’ll walk through generating and using Jenkins CSRF crumb tokens to secure HTTP requests against Cross-Site Request Forgery attacks. You’ll learn how to configure Jenkins for CSRF protection, retrieve crumb tokens via the REST API, and trigger jobs with the proper headers and cookies.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
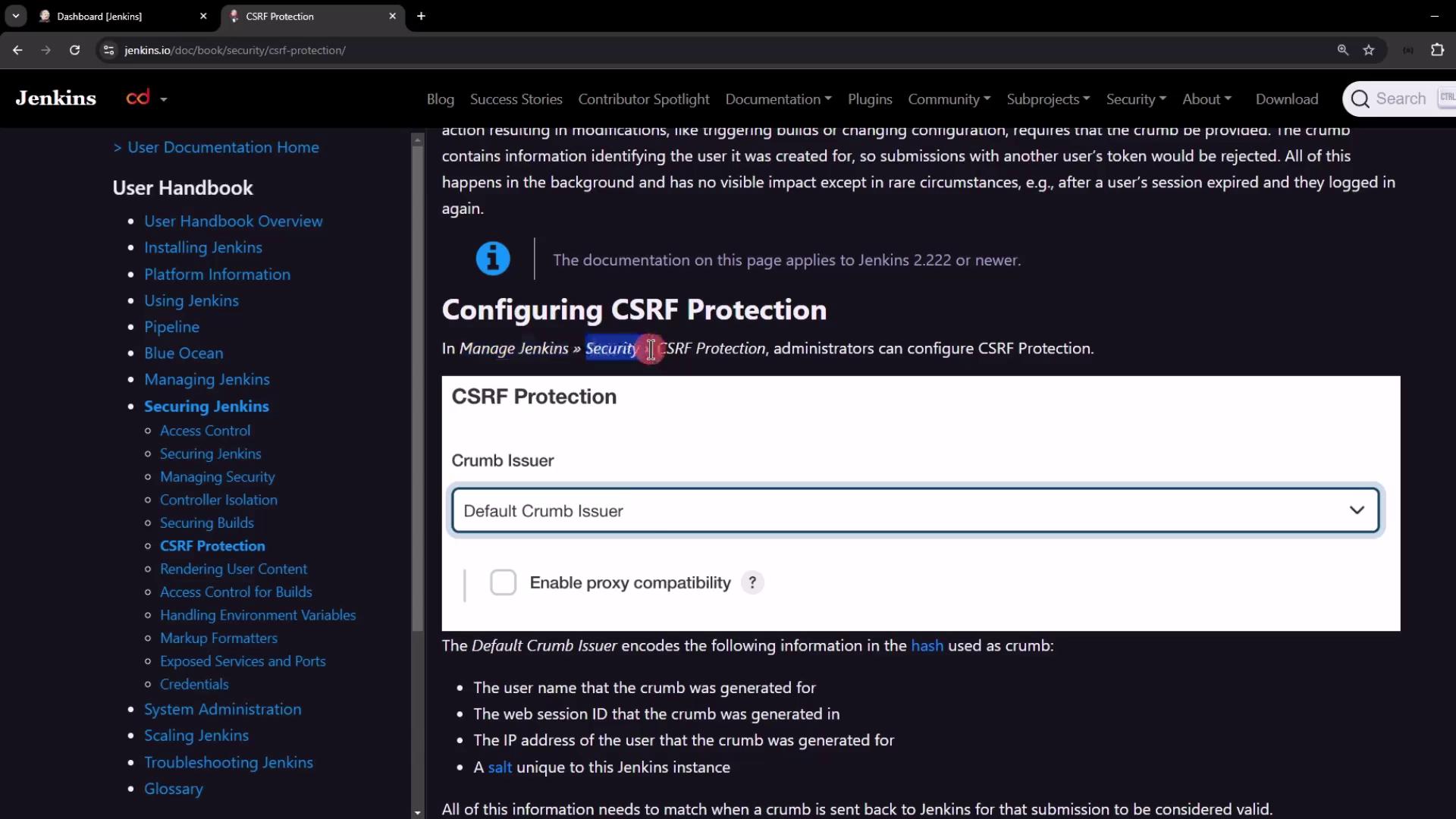
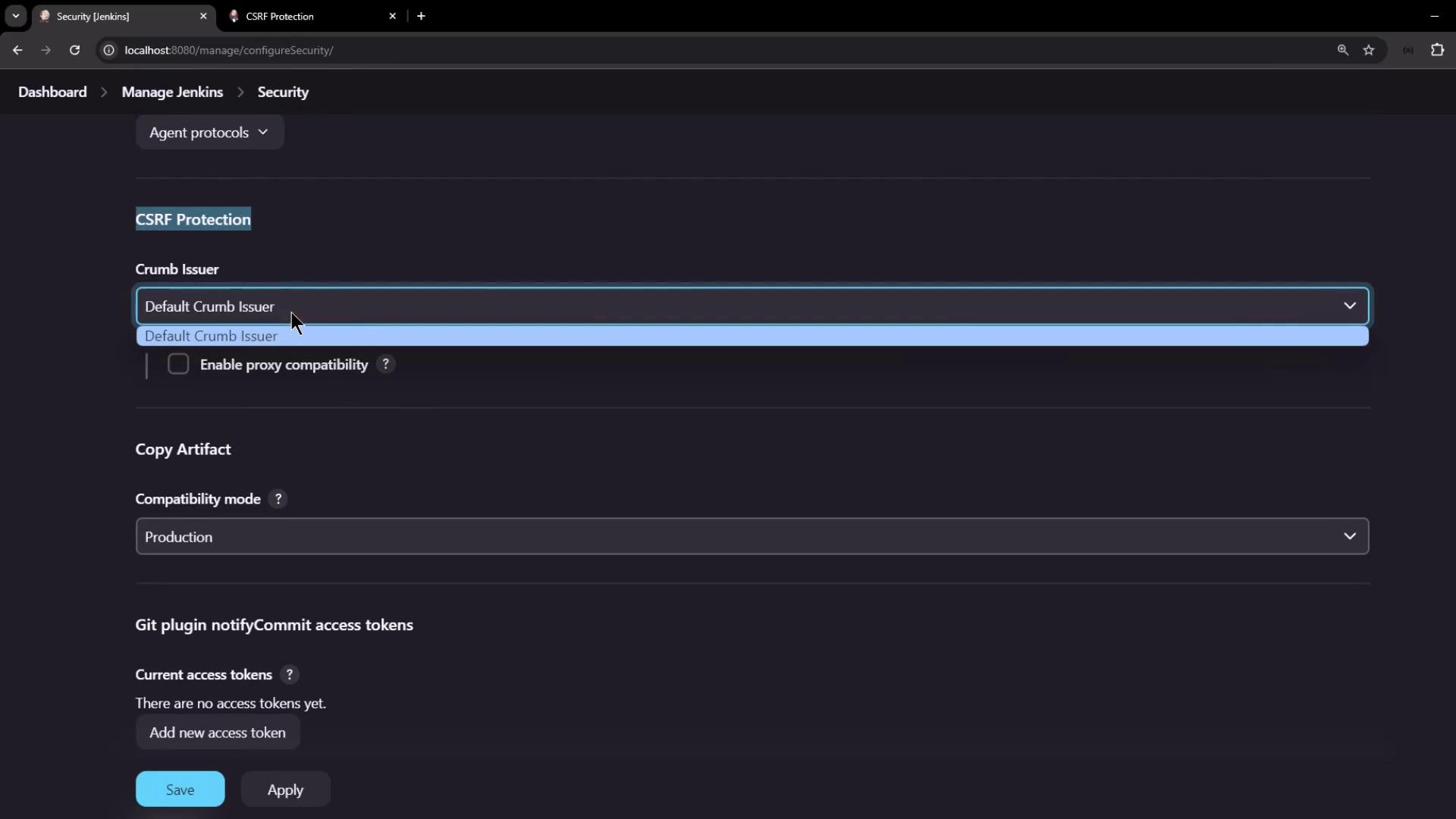
Jenkins CSRF Protection Configuration
By default, Jenkins enforces CSRF protection. As an administrator:- Go to Manage Jenkins → Configure Global Security.
- Locate the CSRF Protection section and confirm it is enabled.
Disabling CSRF protection is not recommended in production. If you must disable it (for testing only), set the system propertyat server startup.
Default Crumb Issuer
Jenkins’s Default Crumb Issuer generates a token hash from several session-specific values. All must match when validating an incoming request:| Encoded Value | Description |
|---|---|
| Username | The authenticated user’s login |
| Session ID | Unique identifier for the Jenkins session |
| User IP Address | Client’s source IP |
| Instance Salt | A secret salt unique to this Jenkins node |
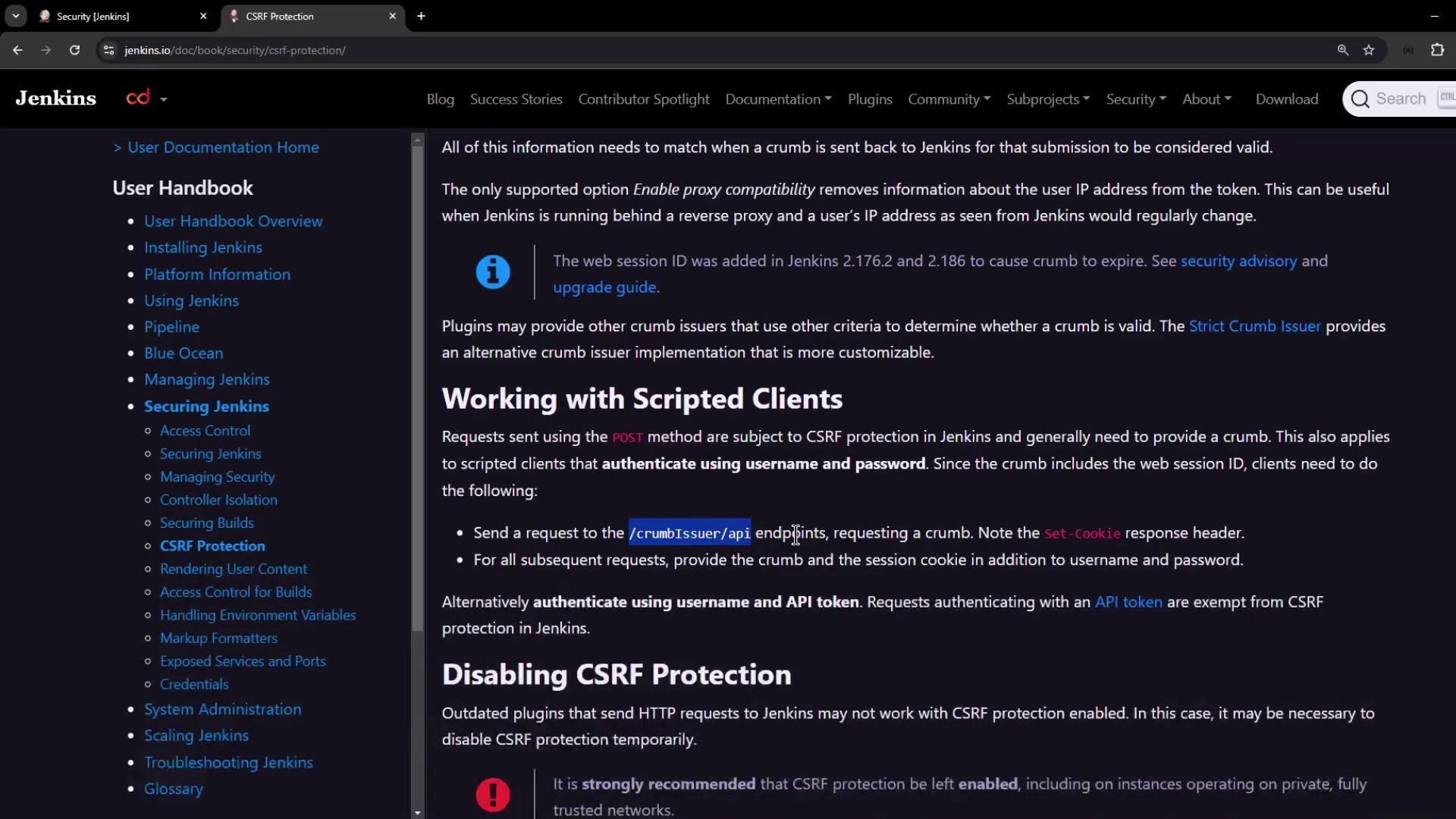
Working with the Crumb Issuer API
The crumb is exposed at the REST endpoint/crumbIssuer/api/json. Authenticate with username/password or API token to receive:
- A JSON payload containing the crumb and header field name
- A session cookie to include on subsequent requests
1. Generate and View the Crumb
2. Inspect Response Headers
View theSet-Cookie header to capture the session ID:
3. Store Cookies with a Cookie Jar
Save the session cookie for later use:Using
--cookie-jar ensures your session cookie is persisted securely between requests.