Welcome to this technical lesson on Network Access Control Lists (NACLs). In this guide, we will explore the key differences between stateful security groups and stateless NACLs, as well as demonstrate how to configure NACLs to control traffic at the subnet level. Before you begin testing NACLs, ensure that your EC2 instances have security groups configured correctly to avoid interference. Security groups are stateful and typically control traffic for individual instances, whereas NACLs filter traffic for the entire subnet. In our scenario, we configure our security groups to allow all traffic so that NACLs become the primary filter.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
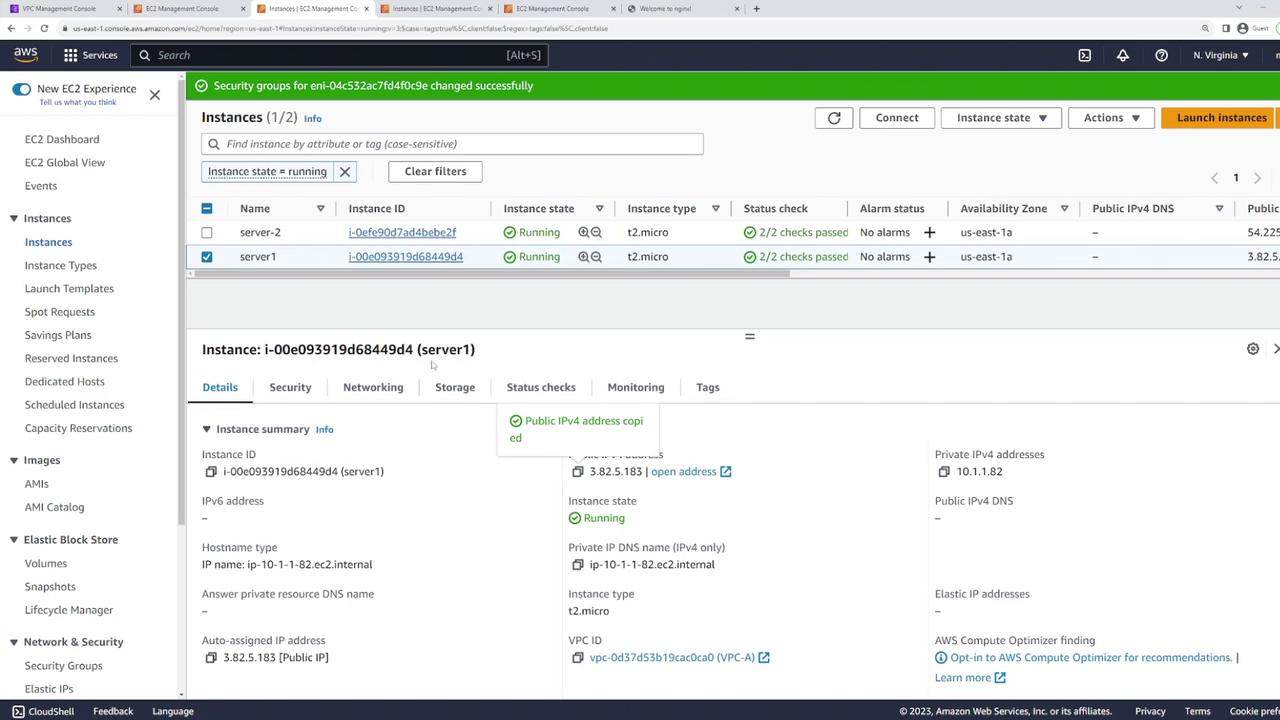
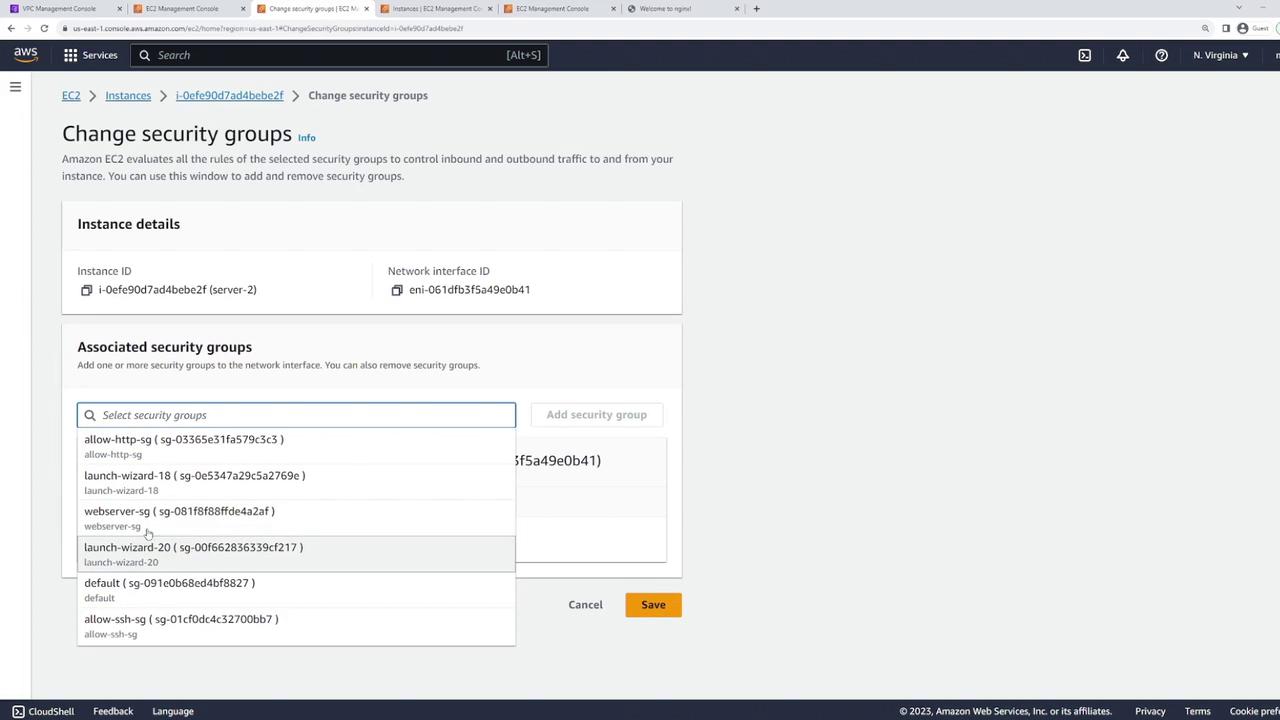
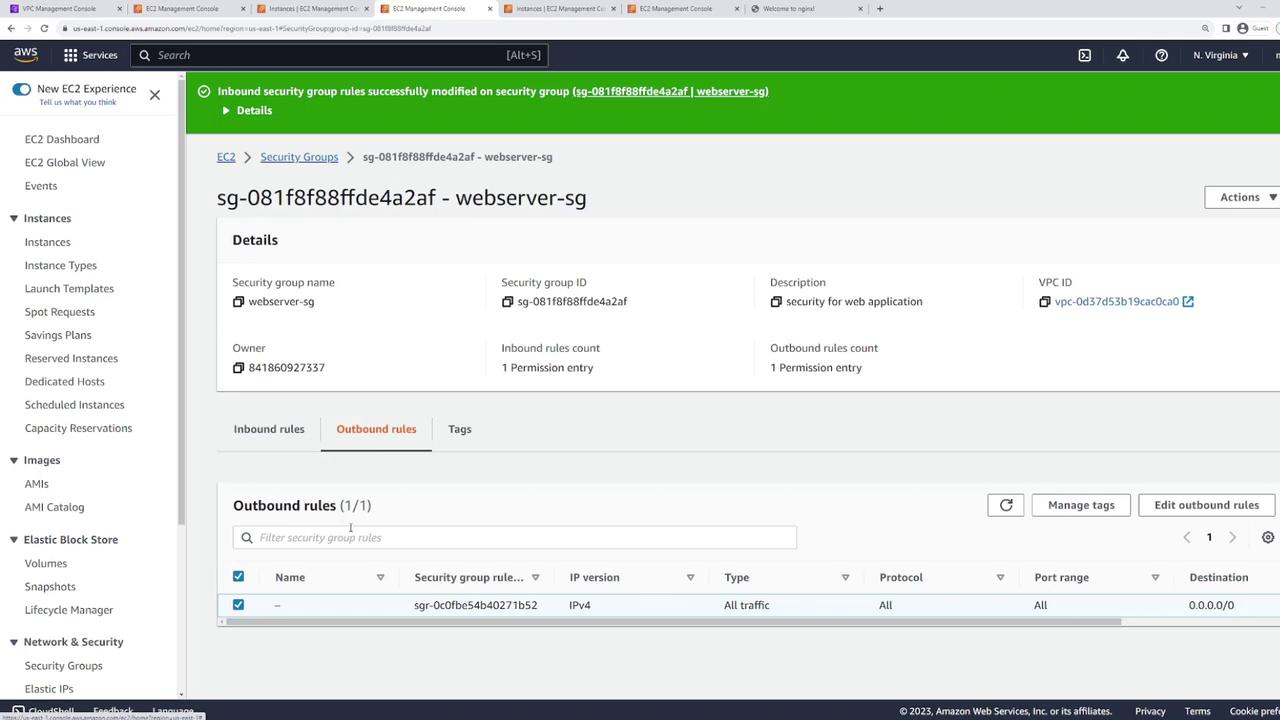
Step 1: Verifying Security Group Settings
Begin by verifying the security groups associated with your servers. For example, one server might be using the “webserver-sg” security group: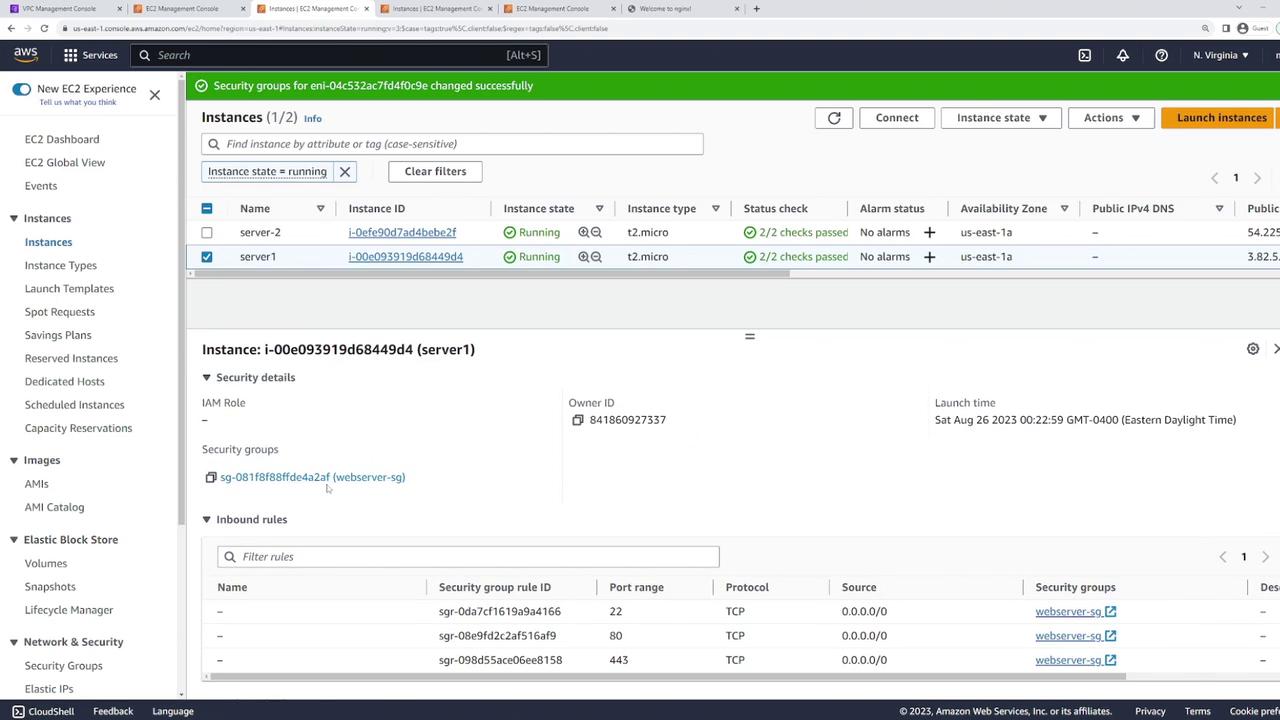
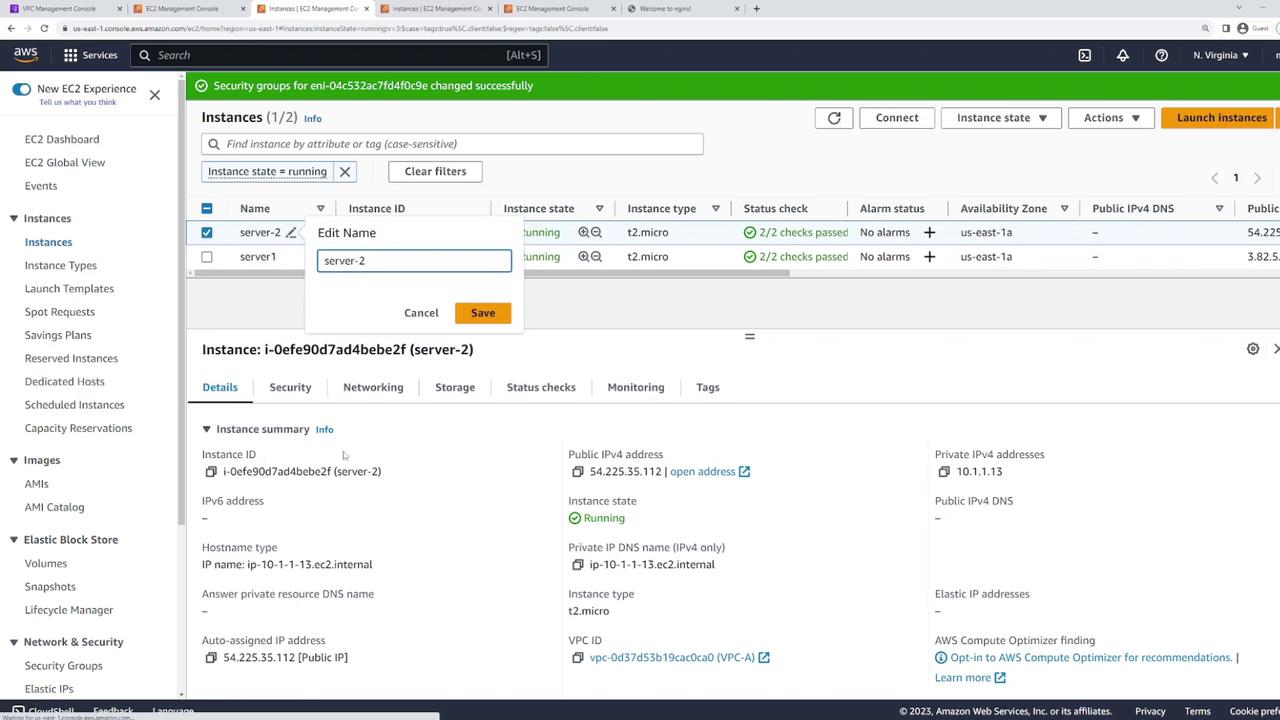
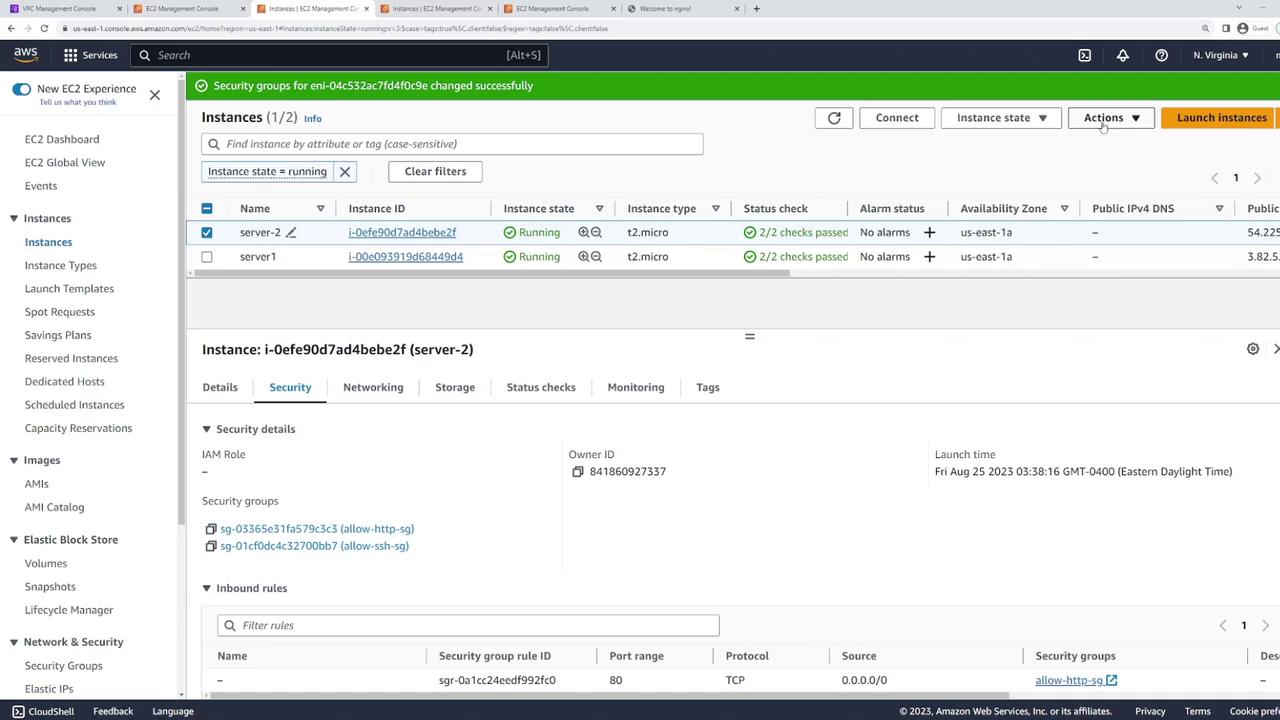
Step 2: Confirming Subnet Consistency
Ensure that both instances reside on the same subnet by checking the networking details from the EC2 console. For example, inspect server one to verify that it is in the correct subnet (e.g., subnet 168.3):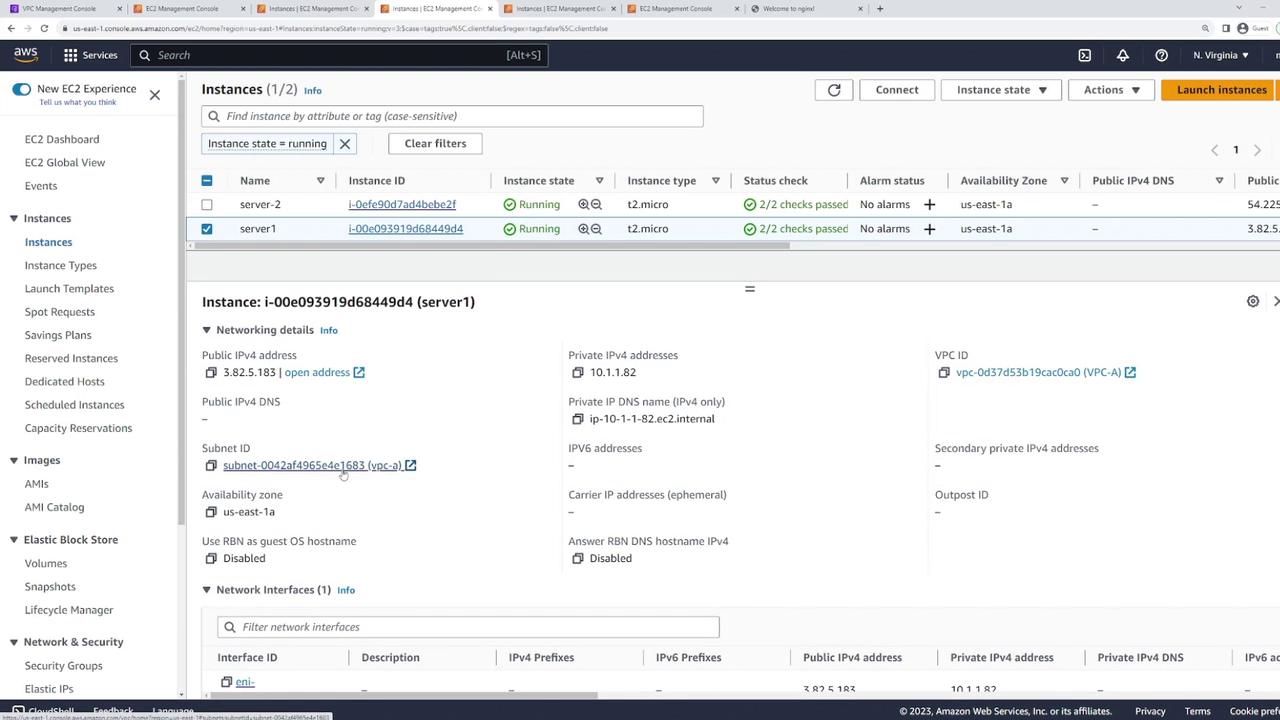
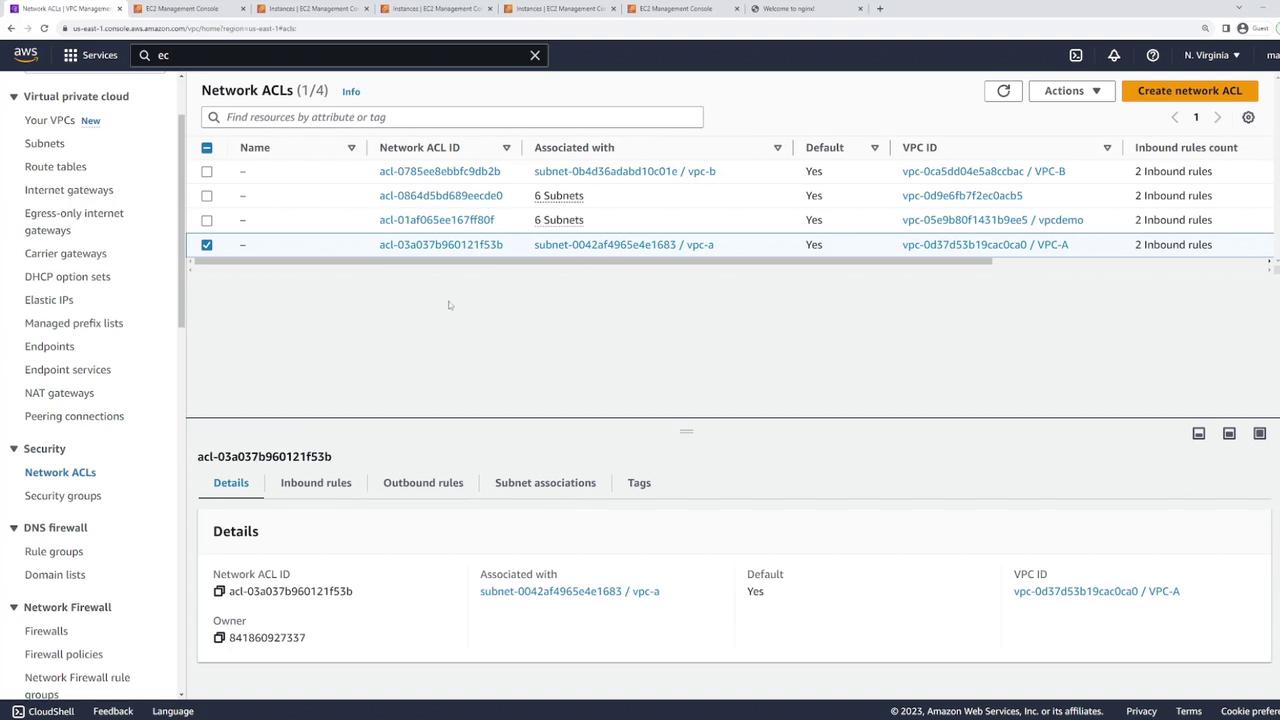
Step 3: Testing Default NACL Settings
To confirm that your configuration is correct, attempt to SSH into an instance. You should be able to establish a connection because the security groups are not restricting any traffic. Below is an example output from a successful ping test and SSH session:Step 4: Modifying NACL Rules
Now, modify the NACL rules to showcase their stateless behavior. Edit the inbound rules, and change rule 100 so that it allows only SSH access. Configure rule 100 to permit SSH (port 22) from any IP address, and then save the changes. Despite security groups still allowing all traffic, this modification will restrict inbound traffic to SSH only, and a subsequent deny rule will block other protocols. To test this configuration, SSH into the instance using server two: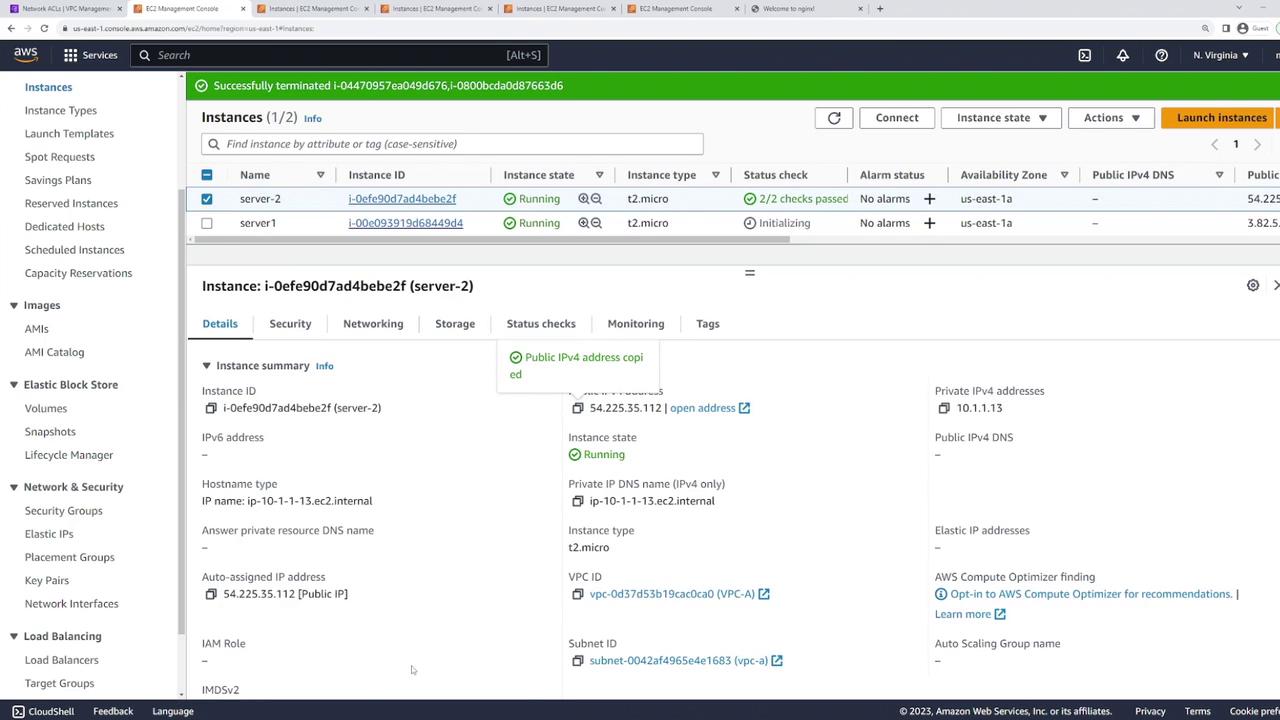
Step 5: Allowing HTTP and HTTPS Traffic via NACLs
To enable web traffic, update the NACL by adding new inbound rules:- Add a rule (for example, rule 101 or 110) that allows HTTP (port 80).
- Add another rule (for example, rule 120) to allow HTTPS (port 443).
-
SSH into server two:
-
Install NGINX using the Yum package manager:
If the package downloads hang, it is due to the stateless nature of NACLs. NACLs require explicit inbound rules for the response traffic (return packets) when an outbound HTTP request is made.
Step 6: Implementing Explicit Deny Rules
One of the advantages of using NACLs over security groups is the ability to explicitly block traffic with deny rules. For instance, you can allow SSH by default but insert a high-priority deny rule for specific IP addresses. To demonstrate this, add a deny rule with a lower rule number (e.g., rule 90) that blocks SSH from a defined IP range. This rule will override the general SSH allow rule for that specific range, while SSH from all other addresses will still be permitted.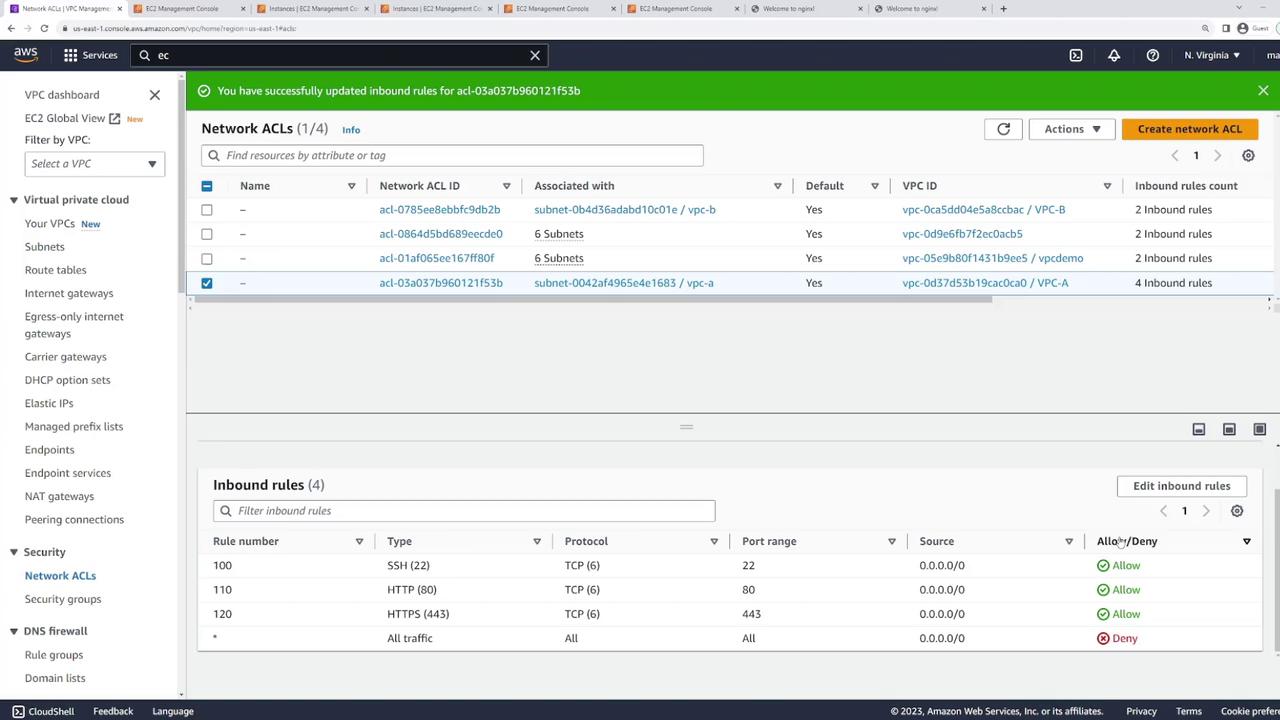
Summary
In this lesson, we covered:- The differences between stateful security groups and stateless NACLs.
- How NACLs operate at the subnet level and require both inbound and outbound rules.
- Configuring NACL rules to allow or block specific types of traffic.
- Demonstrating the practical application by restricting traffic to SSH only and then enabling HTTP/HTTPS traffic.
- Using explicit deny rules to block traffic from specific IP ranges.