In this lesson, we explore Verified Permissions—a scalable AWS service that streamlines permission management for custom applications. Verified Permissions centralizes authorization, allowing you to control user access after authentication is set up. Instead of hardcoding permissions in your application, AWS handles policy management for actions like viewing or deleting content. This centralized model enhances security, simplifies auditing, and decouples authorization from core business logic. It leverages the Cedar policy language to define granular permissions. With Verified Permissions, you can manage policies via the AWS console, CLI, or SDK. Billing is based on the number of authorization requests processed each month, encouraging efficient permission management.Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.

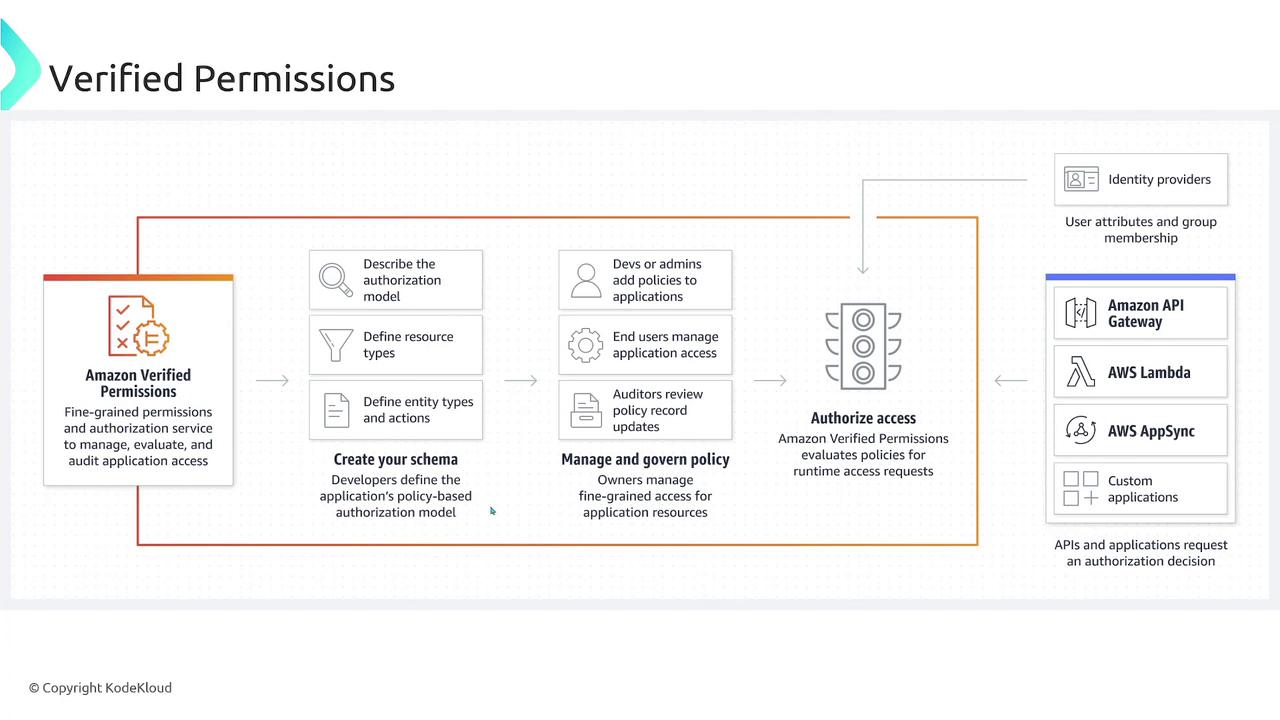
Decoupling authorization from your application development allows you to focus on business logic while ensuring secure, centralized permission management.
- During development, you can define baseline permissions that serve as the foundation for your application.
- End users can also create custom policies, enabling dynamic and flexible authorization based on evolving needs.
Be aware that you’re charged based on the number of authorization requests processed each month. Monitor your workload to manage costs effectively.