Welcome back to this lesson. I’m Michael Forrester, and today we will cover several core security design principles encouraged by AWS. These principles are essential not only for passing the exam but also for designing robust and secure solutions on AWS. When implementing, deploying, or designing services on AWS, it’s critical to ask questions such as:Documentation Index
Fetch the complete documentation index at: https://notes.kodekloud.com/llms.txt
Use this file to discover all available pages before exploring further.
- What aspects of security enhance the service?
- Which design principles strengthen overall security—and which could possibly degrade it if misapplied?
- What is the ultimate security goal we are trying to achieve?
- What principles increase security?
- What principles might compromise it?
- What is our security end goal?

Storing data in raw format without encryption exposes it to unauthorized reading by anyone with access. Encrypting data not only ties into robust access controls but is a fundamental security measure in itself.

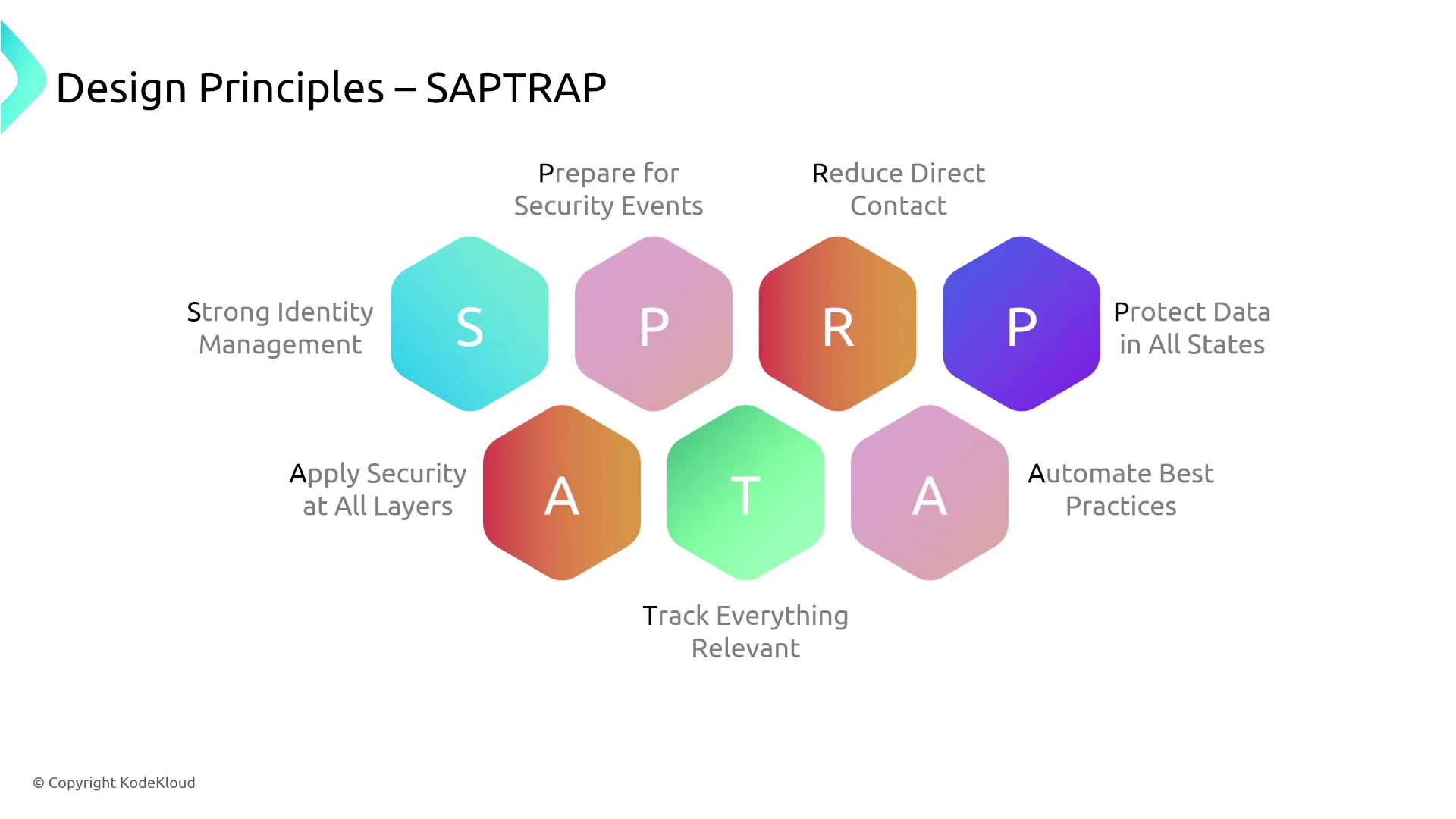
The SAPTRAP Mnemonic
To summarize these principles, remember the mnemonic “SAPTRAP”:| Principle | Description |
|---|---|
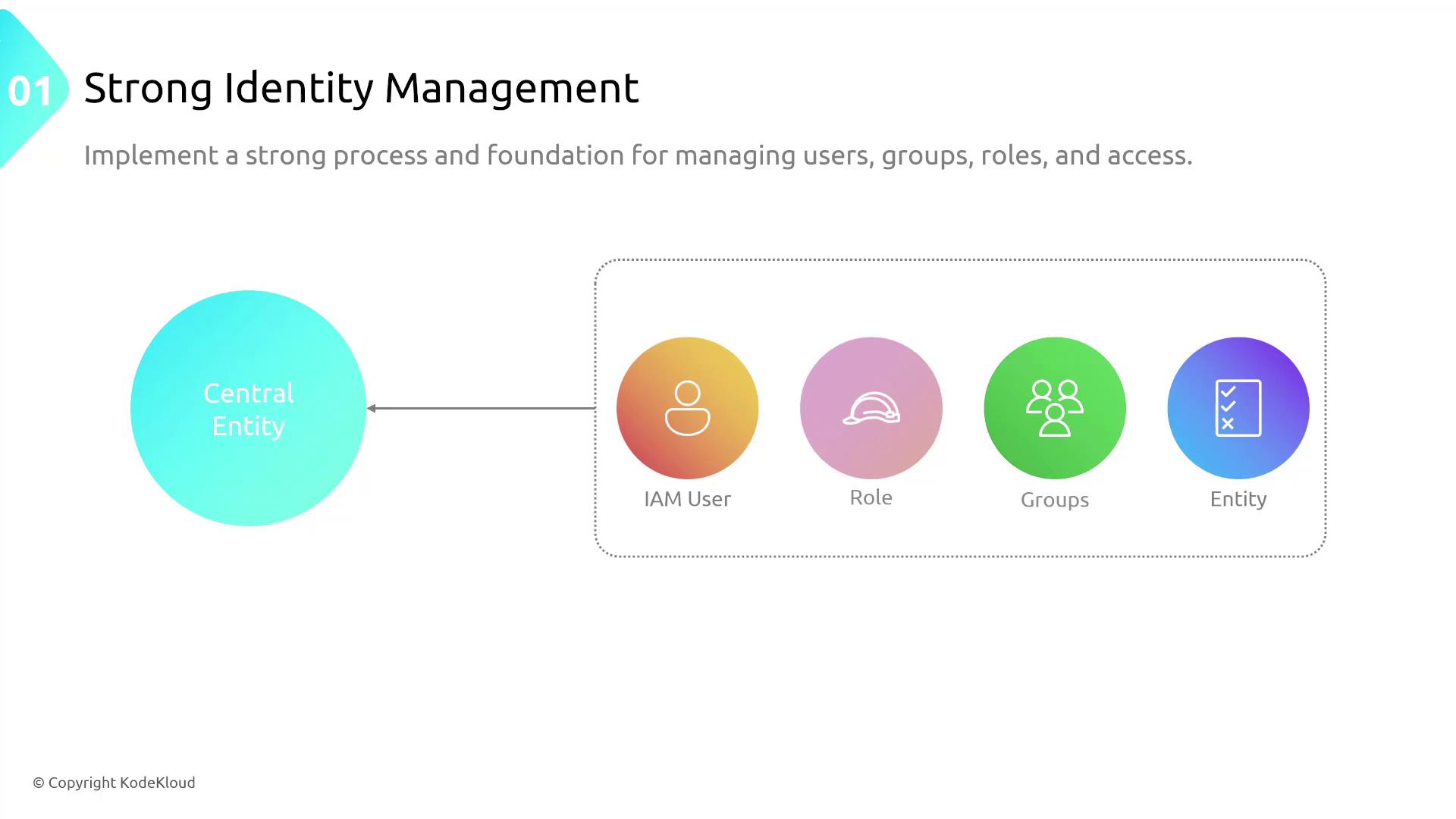
| Strong Identity Management | Robust user, group, and role management through services like IAM and AWS Organizations. |
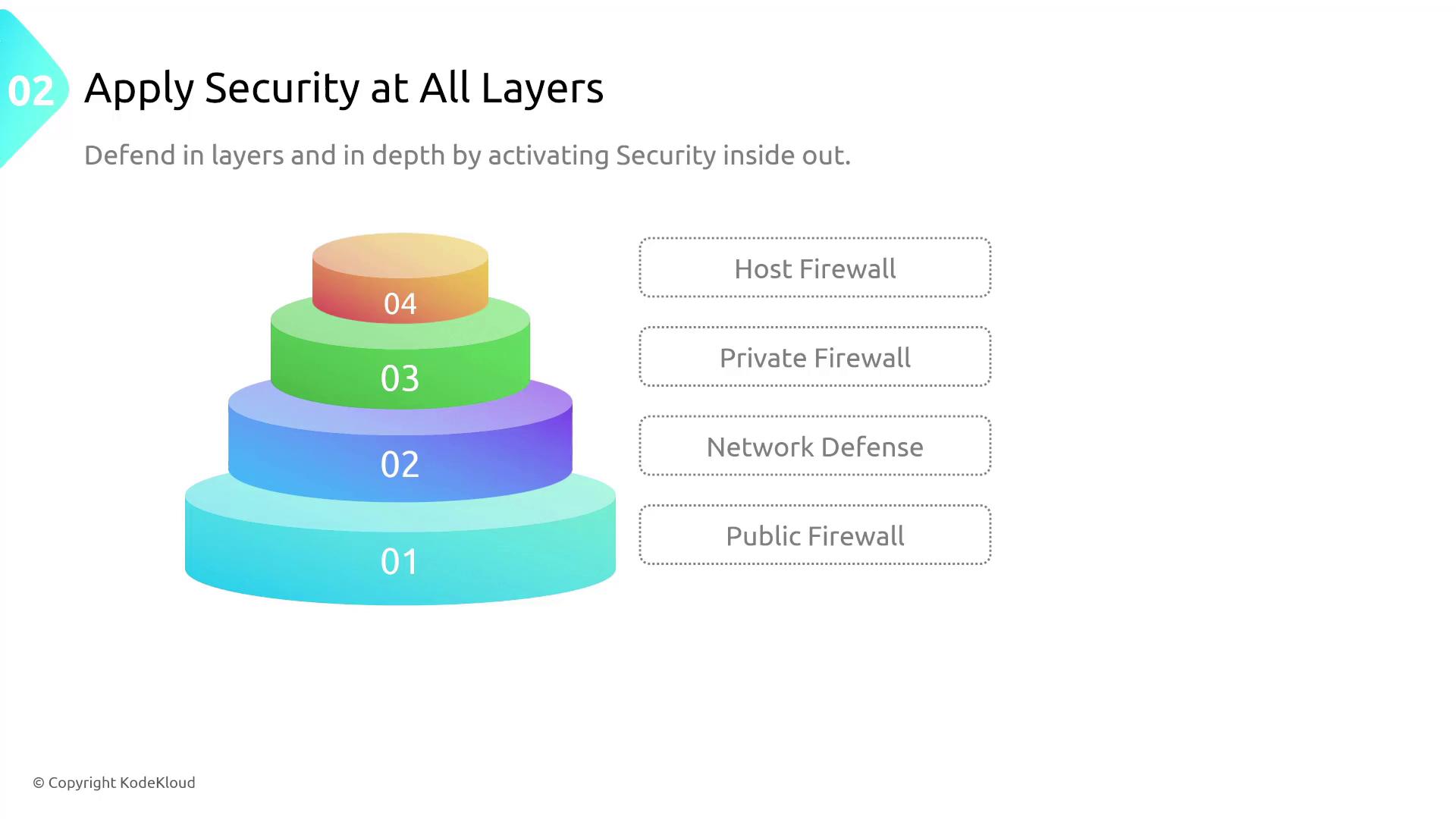
| Apply Security at All Layers | Extend security measures from public firewalls to host and application-level controls. |
| Prepare for Security Events | Develop and follow an incident response plan to handle security breaches effectively. |
| Track Everything Relevant | Log and monitor all metrics, access logs, and configuration details centrally. |
| Reduce Direct Contact | Minimize manual interventions by using automated tools that enforce role-based access. |
| Automate Best Practices | Integrate automation in security checks, patch management, and scalability processes. |
| Protect Data in All States | Encrypt data at rest, in transit, and during processing to ensure complete data protection. |
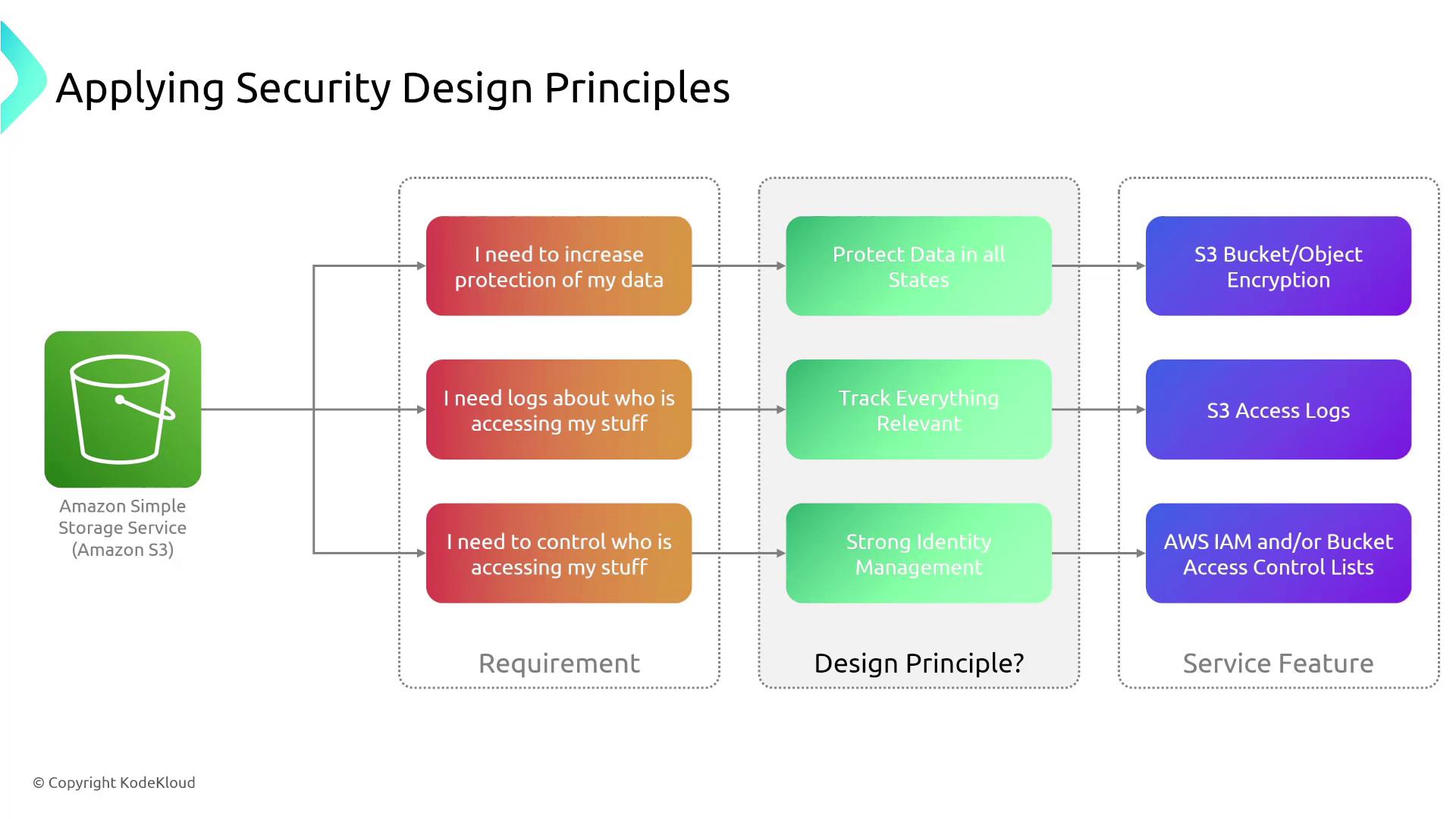
Real-World Example: Amazon S3
Let’s apply these principles to a real-world scenario involving Amazon S3. Suppose a client requires enhanced protection for their S3 data. They would benefit from:- Enhanced Encryption: Protect data at rest and in transit. While AWS now enables encryption by default for new buckets, older buckets might require manual intervention.
- Access Logging: Enable S3 access logging to capture critical details like IP addresses and access patterns, which help in detecting potential security issues.
- Strong Identity Management: Use IAM policies (instead of access control lists) to enforce strict access control and maintain robust security practices.
Summary
Design principles serve as guiding values that help balance security, reliability, and cost in your solutions. Incorporating practices like:- Automating best practices,
- Protecting data in all states,
- Enforcing strong identity management, and
- Applying layered security
While these principles may not appear exactly as-is on the exam, applying concepts like defense in depth and stringent identity management is critical for your security strategy.